Capture the flag — CTF for short — is the single most effective way to turn a developer who knows about security into a developer who can do security. A CTF is a hands-on competition where the only way to earn points is to actually break something, extract a secret, and prove you did it. That loop — read the target, identify the weakness, exploit it, verify — is the same loop that a secure-code reviewer, a penetration tester, or a threat-aware developer runs on real code. The difference is that CTF compresses the loop into minutes, gives immediate feedback, and uses a scoreboard to make learning addictive instead of exhausting. This guide walks what CTF actually is, the event formats, the categories that matter, the platforms worth starting on, how to prepare, how to build a team, and — for engineering leaders — how to run an internal CTF that produces measurable security fluency instead of a one-time hype event.
What Is Capture the Flag (CTF)?
In the capture the flag cyber security world, a "flag" is a specific string — usually something like flag{m3m0ry_corrupt10n_1s_fun} or CTF{you_found_the_xss} — that is hidden inside a vulnerable system, file, application, or binary. The goal of the competition is to extract that string by exploiting the system, and submitting the string to a scoreboard earns points for your team. Each challenge has its own flag, its own vulnerability to exploit, and its own point value determined by difficulty.
The ctf meaning most developers meet first is the Jeopardy-style event — a grid of challenges across several categories, each worth a point value, where teams pick what to solve in any order and the highest score at the end of the time window wins. A CTF event can run for two hours (beginner training), twelve hours (most online CTFs), 48 hours (major weekend events like picoCTF or Google CTF), or even a full week (some academic qualifications). The organizer hosts the infrastructure — the intentionally vulnerable services, the scoreboard, the hint system — and the teams connect over the internet or, for some events, on-site.
The format traces back to DEF CON's CTF competition in 1996, which established the attack-defense variant where teams simultaneously defend their own services while attacking other teams' services. Modern CTF culture has grown into a global ecosystem: CTFtime.org lists hundreds of qualifying events every year, universities run CTF teams the way they run debate teams, and companies from Google to Trend Micro run flagship CTFs that draw tens of thousands of participants. The pedagogical point is that offense teaches defense better than defense teaches defense: the developer who has exploited an SQL injection in twenty different challenge contexts writes code that is far harder to SQL-inject than the developer who has only read a slide about parameterized queries.
The Types of CTF: Jeopardy, Attack-Defense, and Mixed
Three formats account for nearly every CTF you will encounter as a developer, and each teaches a slightly different set of skills.
Jeopardy-style. The grid-of-challenges format, also called "task-based." The organizer publishes a board of challenges organized by category and difficulty. Each team works through the challenges independently, submitting flags as they are found, and the team with the highest cumulative score at the event's end wins. Jeopardy is the dominant format in 2026 for online CTFs and for beginners, because it scales to any number of participants, does not require real-time infrastructure defense, and lets teams focus on the challenges that match their skills. Most training-oriented platforms (picoCTF, TryHackMe, HackTheBox) effectively run permanent Jeopardy-style environments.
Attack-Defense. The original DEF CON format. Each team runs an identical set of vulnerable services on its own infrastructure, and the team's job is simultaneously to patch vulnerabilities in its own services (defense) and exploit the same vulnerabilities in other teams' services (offense). Points are earned for successful exploitation of other teams and for keeping your own services running and unpatched-in-the-right-way. Attack-Defense is materially harder than Jeopardy because it combines real-time operations with offensive security — a team needs developers who can patch in production, security engineers who can write exploits, and coordination between the two. It is the format of finals at DEF CON, Pwn2Own, and a handful of invitational events. It is usually not where a developer starts.
Mixed format. A hybrid where the event has a Jeopardy component (challenge grid) and an Attack-Defense component (live services), with the final ranking combining both scores. Mixed formats are common at university CTF finals and at some corporate events because they let participants of different skill levels contribute meaningfully — beginners can rack up points on easy Jeopardy challenges while advanced players carry the attack-defense portion.
For a developer entering the field, the path is almost always Jeopardy first. Spend six months on permanent Jeopardy platforms until the basic categories are familiar, enter a few time-boxed Jeopardy CTFs to experience the competitive format, and only then consider Attack-Defense if the interest and time commitment are there. Skipping the Jeopardy phase to jump into Attack-Defense is a common mistake that produces frustration and burnout instead of growth.
Why CTF Skills Translate Directly to Secure Coding
The skepticism about CTF among engineering leaders usually takes a predictable form: "my developers do not need to learn to exploit things, they need to learn to not introduce exploits." The premise is wrong, and the reason it is wrong is the single most important insight in security training: writing secure code requires recognizing what insecure code looks like at attack time, and there is no faster way to build that recognition than to attack a lot of code.
A developer who has exploited twenty SQL injection challenges, each in a slightly different context — integer-based, string-based, blind, time-based, second-order, through a JSON API, through a header, through a filename — has an intuition for SQL injection that no amount of reading can produce. The intuition shows up at code review: the developer sees a query construction, automatically runs the mental attack loop, and catches the vulnerability before it ships. The same developer, without CTF exposure, reads the same code and sees a query — correctly, but without the attacker's eye. This is the mechanism by which CTF produces measurably better secure code. It is not that CTF teaches security theory; it is that CTF installs the attacker's pattern-matching into the developer's unconscious review process.
The transfer is also specific. CTF skills in web categories transfer to secure web development. CTF skills in reverse engineering transfer to dependency risk assessment. CTF skills in cryptography transfer to correct use of crypto libraries. A developer who has never touched CTF but has spent a week on hands-on web challenges leaves the experience able to recognize XSS, CSRF, SSRF, IDOR, and the common authentication bypasses in production code — not because they were lectured on the patterns, but because they exploited them. This is what we mean when we say CTF is a deliberate practice environment for the attacker mindset, and it is the reason CTF shows up in the internal training curricula of every major tech company even though none of their developers will ever compete at DEF CON.
Essential CTF Categories: Web, Pwn, Crypto, Reverse, Forensics, OSINT
CTF challenges are organized into categories, and each category represents a distinct skill area. A balanced CTF event draws from five to seven categories; a developer-focused program usually emphasizes three.
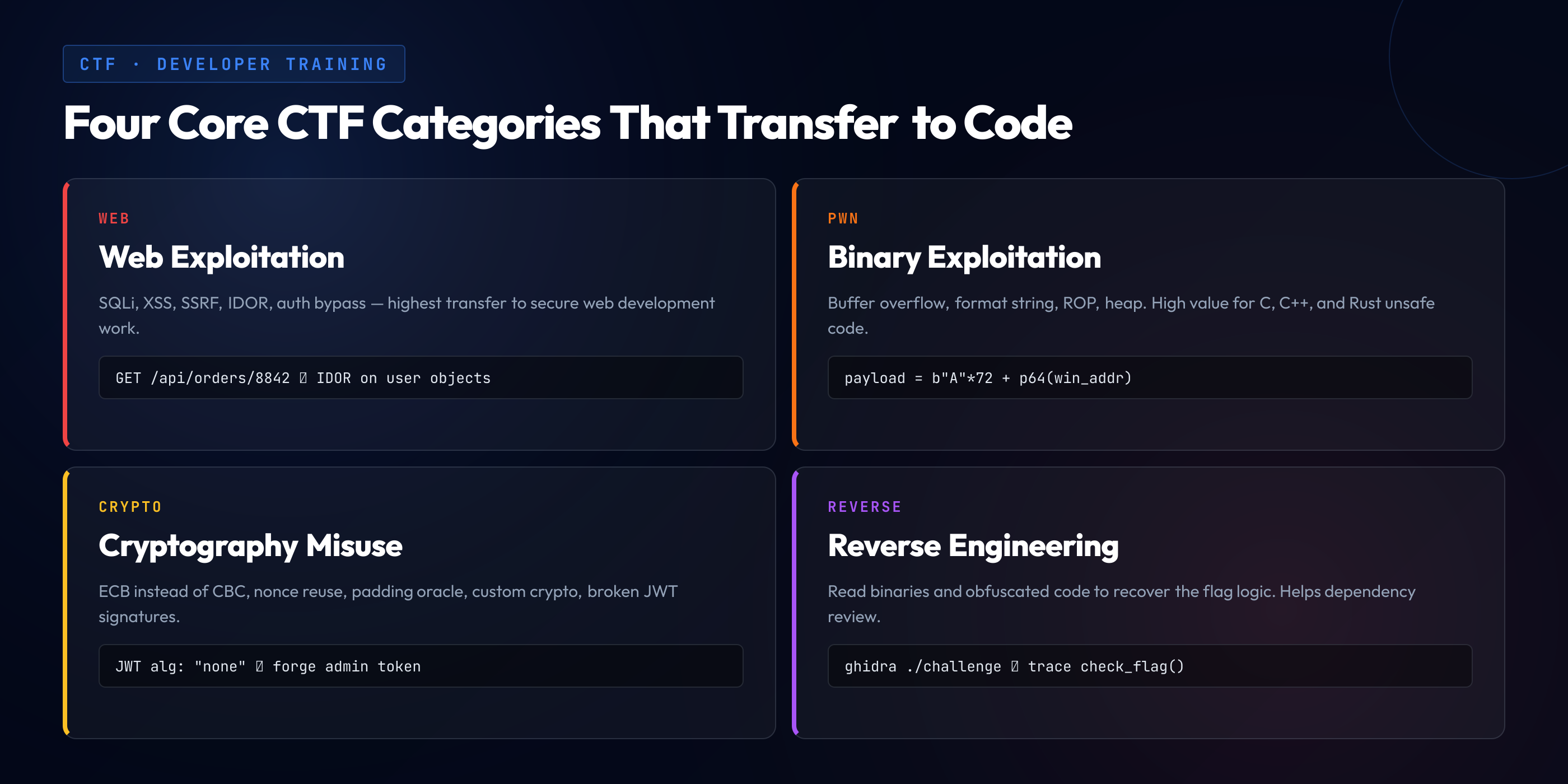
| Category | What you do | Dev transfer |
|---|---|---|
| Web | Exploit web applications: SQLi, XSS, SSRF, IDOR, auth bypass | Highest — direct to secure web development |
| Pwn (binary exploitation) | Exploit compiled programs: buffer overflow, format string, ROP, heap | High for systems languages (C, C++, Rust unsafe) |
| Crypto | Break or misuse cryptographic implementations | High — every product uses crypto incorrectly at least once |
| Reverse engineering | Analyze binaries or obfuscated code to find the flag logic | Moderate — helps with dependency analysis and malware review |
| Forensics | Analyze network captures, disk images, memory dumps | Moderate — helps with incident response |
| OSINT | Find information from public sources (social media, DNS, etc.) | Low for direct coding, high for attack-surface awareness |
| Misc / Stego | Hidden data in images, audio, unusual protocols | Low — good for puzzle practice |
Web. The highest-transfer category for almost every engineering organization, because nearly every organization ships web surface. Web CTF challenges teach the 2026 OWASP Top 10 at a depth that classroom training cannot reach — the developer will meet injection, broken access control, cryptographic failures, insecure design, security misconfiguration, and authentication failures in the form of actual exploitable challenges and leave with a working mental model of each. This is the category that produces the clearest productivity return for a web-focused engineering team.
Pwn (binary exploitation). The oldest CTF category and still a centerpiece at major events. A pwn challenge typically gives the participant a binary (often ELF or Windows PE) with a known vulnerability class — buffer overflow, format string, use-after-free, integer overflow — and the goal is to exploit it to read the flag, usually by crafting input that overwrites the return address or leaks memory. The skills transfer directly to teams working in C, C++, or Rust unsafe code; less directly for teams working in memory-safe languages, though the understanding of what the language's safety guarantees actually protect against is itself valuable.
Crypto. Cryptography challenges teach where crypto libraries go wrong — using ECB mode when CBC is required, reusing nonces, implementing custom crypto instead of calling a library, mishandling padding. The 2026 landscape has enough crypto-related incidents in production systems (weak JWT implementations, broken OAuth flows, misconfigured TLS) that every developer who ships to production benefits from at least a basic CTF-level familiarity with what crypto misuse looks like.
Reverse engineering. Rev challenges give the participant a binary or obfuscated program and ask them to understand it well enough to produce the flag. The skills overlap with debugging, dependency analysis, and malware triage. For teams whose security posture depends on understanding third-party dependencies in depth, some reverse skill is genuinely useful; for most teams, it is a secondary category.
Forensics. Forensics challenges present an artifact — a PCAP network capture, a disk image, a memory dump — and ask the participant to extract information from it. The skills transfer to incident response and, increasingly, to cloud forensics as detection tooling matures. Most developer programs treat forensics as optional.
OSINT. Open-source intelligence challenges are puzzles that require finding information from public sources — a social media post, a DNS record, an archived web page, a code repository. The direct coding transfer is limited, but the indirect value is understanding what the organization's public attack surface actually looks like. A developer who has done OSINT challenges thinks twice before posting the internal architecture diagram on a public blog.
Beginner Platforms: PicoCTF, TryHackMe, HackTheBox, and More
A developer picking up CTF for the first time in 2026 has better learning infrastructure than any generation before. Four platforms dominate the beginner path, and picking among them depends more on learning style than on technical content — the underlying skills converge.
picoCTF. Run by Carnegie Mellon, free, explicitly designed as a teaching platform with challenges organized by category and difficulty, each with writeups and hints. picoCTF is the canonical starting point for a developer with no prior CTF exposure. The 2026 catalog includes hundreds of permanently available challenges from every recent picoCTF competition, and the difficulty curve is gentler than commercial platforms. A developer who spends a weekend on picoCTF finishes with working exposure to web, crypto, forensics, and beginner pwn. Start here.
TryHackMe. A subscription-based platform (with a free tier) organized into "rooms" — guided learning paths through a specific topic, with hands-on labs rather than raw challenges. TryHackMe is the gentlest on-ramp for someone who prefers structure to exploration — the rooms walk through the theory, the tools, and the exploitation step by step. The tradeoff is that the rooms are more scripted than a CTF challenge, so the developer learns the mechanics but sometimes does not build the open-ended problem-solving muscle that a real CTF demands. A good complement to picoCTF, not a replacement.
HackTheBox. A more adversarial platform — less guidance, harder challenges, closer to real CTF experience. HackTheBox runs both a permanent platform (machines and challenges) and a CTF event series. For developers who have spent time on picoCTF or TryHackMe and want harder material, HackTheBox is the next step. The 2026 Academy offering adds structured paths for people who want progression rather than raw difficulty.
OverTheWire. Free, command-line-based, permanent. The Bandit wargame is the classic Linux fundamentals progression; the Natas series is a web progression; the Leviathan, Narnia, and Behemoth series cover binary exploitation. OverTheWire's age (the Bandit wargame predates Twitter) is not a drawback — the fundamentals do not change, and the lack of modern visual polish forces engagement with command-line tooling that every real CTF requires.
The pattern that produces the fastest growth for most developers: start on picoCTF for breadth, use TryHackMe rooms for structure on specific topics as they come up, move to HackTheBox when picoCTF feels too easy, and use OverTheWire throughout as a shell/tooling reference. Six months of two-evenings-per-week engagement across these platforms produces a developer who can contribute in a real team CTF.
How to Prepare for Your First CTF
The first CTF event is where a developer discovers whether they have built enough skill on the practice platforms to compete in a timed, competitive environment. The gap between "I can solve easy picoCTF challenges when I have time" and "I can solve a challenge under time pressure while my team is counting on me" is real and surprises nearly everyone the first time.
Pick a beginner-friendly CTF. CTFtime.org rates every listed CTF on a difficulty scale and publishes the results. Look for events rated "beginner," "introductory," or with names like "[Organization] Beginner CTF." Events like picoCTF's annual competition, the National Cyber League in the US, or university-hosted beginner CTFs are ideal for a first event. Avoid Pro-rated events (DEF CON qualifiers, Google CTF, RealWorldCTF) for a first experience — you will not solve anything and will leave discouraged.
Prepare your toolkit. Most CTF work happens in a Linux environment. Install Kali Linux or a lean Debian/Ubuntu with the common tools: Burp Suite (web proxy), gdb with pwndbg or GEF (binary debugging), Ghidra or IDA Free (reverse engineering), Wireshark (network analysis), CyberChef (encoding/decoding), sqlmap (automated SQL injection), nmap (network reconnaissance), netcat and socat (connection manipulation). Do not wait until the event starts to set up the toolkit — the first hour of a first CTF is stressful enough without also debugging Burp's certificate setup.
Study the previous year's writeups. Most CTF teams publish writeups after events. Before your first event, read ten writeups from the organization's previous year. You will recognize the house style — what categories they emphasize, what difficulty curve they use, what tricks they reuse across years. This reconnaissance is not cheating; it is preparation that every serious team does.
Set a realistic goal. For a first CTF, a realistic goal is "solve three challenges" rather than "place in the top 50." The skill you are building is the skill of performing under the event's time pressure, not the skill of winning. Every challenge solved is progress. Every challenge attempted but not solved is also progress — you now know what category of challenge you need to practice more.
Form a small team. Solo CTFs are harder than team CTFs for reasons that are not about division of labor — they are about motivation. A team of three developers who are all at the same skill level will solve more challenges than any of them would alone, because the social dynamics of "I cannot be the one who gives up first" produce more persistence than individual willpower. Start with colleagues; find a CTF community (Discord, university club, local 2600 meetup) after the first event if you want more serious competition.
Competing at Scale: DEF CON, Google CTF, and Team Building
Beyond the beginner tier, the CTF world has a competitive structure that mirrors professional sports. A handful of flagship events — DEF CON CTF, Google CTF, PlaidCTF, HITCON CTF, RealWorldCTF — draw the top teams globally. Qualifying for these events requires placing in earlier qualifying CTFs on CTFtime. The teams at this tier have dozens of members, specialize by category, practice weekly, and produce original research that advances the field (novel exploitation techniques, new bug classes) alongside their competition results.
Team composition at scale. A serious CTF team has specialists: one or two pwners, one or two web experts, a cryptographer, a reverse engineer, a forensics person, and a coordinator who triages challenges to the right specialists during an event. The specialization matters because modern CTF challenges are deep enough that a generalist who tries to solve a hard pwn challenge will run out of time before a specialist would. The team dynamic resembles a small engineering team more than a hackathon group.
Practice cadence. Top teams compete in CTFs two to four weekends per month, hold internal study sessions between events, and write up each event for the public repository of writeups. The time commitment is substantial — roughly the same as a competitive amateur sport. For a developer interested in reaching this tier, the realistic path is to find an existing team rather than build one from scratch; most universities have CTF teams, many cities have CTF meetups, and the CTF community is welcoming to competent newcomers.
Career adjacency. Competitive CTF performance is a legitimate signal in security-adjacent hiring at tech companies, offensive security firms, and government agencies. It is not required — many excellent security engineers have never competed — but for developers who enjoy the competitive format, CTF success opens doors. The professional value is not "CTF skills directly translate to security engineering jobs"; it is "consistent CTF participation over years is visible, measurable, and rare, and it signals persistence and capability." A natural extension for developers who enjoy the competitive format is moving from CTF into bug bounty programs — same offensive pattern-matching, applied to real production targets, with payouts when findings are valid.
Running an Internal CTF at Your Company
For engineering leaders, the most useful form of CTF is not the external competition but the internal one — a CTF event run inside the company for the company's own developers, with challenges designed to build the security fluency the team actually needs.
The case for internal CTF. The classroom component of developer security training has well-known limits: attendance is spotty, retention is poor, and the content is inherently abstract because it cannot reference the company's actual codebase. An internal CTF solves all three. Attendance is high because the format is engaging and the competition is visible. Retention is high because the learning is hands-on and tied to memorable challenge-solving moments. And the challenges can be designed to mirror the vulnerability classes the company's own code actually exhibits — the checkout service becomes an IDOR challenge, the admin panel becomes an auth-bypass challenge, the payment import becomes an SSRF challenge.
The rollout pattern. Start with a one-day internal CTF for a small pilot team — 20-30 developers — with 15-20 challenges of varying difficulty, at least half of them web-based (the highest-transfer category). Platforms like CTFd, which is open-source and free for internal use, handle the infrastructure. Source challenges from a mix of rewritten public challenges (good for breadth) and custom challenges that reflect your codebase's patterns (good for direct transfer). Run the event on a dedicated day with leadership visibility — this is not a lunchtime optional, it is a training day with the same protected status as any other training investment.
Connect the CTF to the ongoing program. A single internal CTF event produces a short-term spike in security fluency and enthusiasm. An internal CTF event that is connected to the ongoing developer training program, the code review discipline, and the threat modeling practice — that is where compound returns start. A developer who solves an SSRF challenge at the internal CTF recognizes SSRF in code review the next month, identifies SSRF risk in threat modeling the month after, and contributes to the mitigation design. The CTF becomes the on-ramp; the program is the road.
The common mistake. Running an internal CTF as a standalone event without an underlying training program produces a one-time enthusiasm spike that evaporates within a quarter. Running it as the capstone to an ongoing language-specific secure coding training program turns the enthusiasm into sustained capability. The difference is not in how the CTF is run; it is in what exists around it.
CTF Is the Training Loop. The Program Is What Makes It Stick.
A one-time CTF event is fun. A CTF event wired into a year-round developer security program — language-specific challenges, per-role curricula, measurable fluency growth — is what produces engineering teams that ship fewer vulnerabilities quarter over quarter. SecureCodingHub runs this as a platform: hands-on challenge content in the developer's own stack, the attacker-mindset pedagogy CTF encodes, and the measurement layer that turns practice into a metric leadership can track. If you are thinking about internal CTF as the front door to a serious security training program, we would be glad to show you how our platform fits.
See the PlatformCommon CTF Pitfalls (and How to Avoid Them)
The paths that fail in CTF pedagogy are predictable enough to name. Each of them is recoverable, but the recovery is easier if the team recognizes the pattern before it consumes a quarter.
Starting too hard. A developer who reads that DEF CON CTF is the pinnacle and signs up for a DEF CON qualifier as their first event will solve zero challenges, conclude CTF is not for them, and quit. The difficulty curve matters. Start on picoCTF beginner, move to picoCTF intermediate, work through TryHackMe beginner rooms, then graduate to HackTheBox starting points. Skipping the easy tier produces survivorship bias — a handful of developers thrive in the deep end, but the median developer drowns.
Solo grinding without writeups. A developer who works through challenges alone, never reads other people's writeups, and never publishes their own develops idiosyncratic habits and misses the canonical solution techniques. Reading writeups after solving (or after giving up) is how a CTF player learns the patterns the community has converged on. Publishing your own writeups, even if they are rough, forces you to articulate what you did — and articulating is where learning solidifies.
Category over-specialization too early. A developer who decides "I am a web person" and refuses to touch pwn or crypto develops an imbalanced skill set that limits the contribution they can make to a team CTF or to their organization's security posture. Breadth first; specialization after. The web-only developer cannot evaluate whether the team's build toolchain is attackable (that requires pwn/reverse) or whether the authentication flow is cryptographically sound (that requires crypto).
Treating CTF as a hobby, not a training loop. CTF participation that is disconnected from the developer's day-to-day work produces a hobbyist who is good at CTF but whose CTF skills do not visibly change how they write code. The transfer from CTF to production work is not automatic; it requires the developer to consciously map what they learn in CTF to the code they are reviewing and writing at work. Teams that frame CTF as deliberate practice for secure development get the transfer; teams that frame it as Friday-night fun get entertainment but less impact.
Running internal CTF without a program. The enterprise equivalent of treating CTF as a hobby. A one-off internal CTF event produces a memorable day and a three-week enthusiasm tail, then the effects fade. Connect the CTF to the secure SDLC — to the code review discipline, to threat modeling practice, to the ongoing training curriculum — and the CTF becomes the on-ramp to a year-round capability rather than the event itself.
Closing: CTF Is a Training Loop, Not a Hobby
The reason CTF works as a security training methodology is not that it is fun — though it is — and not that it is competitive — though it is that too. The reason it works is that CTF is the shortest path between "I have heard of this vulnerability class" and "I can recognize and exploit this vulnerability class in a new context I have never seen before." Every CTF challenge is a small application of a vulnerability class to a new surface, and the skill of pattern-matching across those new surfaces is exactly the skill that keeps vulnerabilities out of production code.
The developer who spends one evening a week for six months on picoCTF and TryHackMe emerges with a working mental model of the OWASP Top 10 that no classroom training produces. The engineering organization that runs an internal CTF four times a year and connects it to its ongoing secure coding training program produces developers who ship measurably fewer vulnerabilities. The ingredients are not secret: a beginner-friendly starting platform, a team of peers, consistent practice, writeups read and written, and — at the organizational level — the surrounding training program that turns event enthusiasm into sustained practice.
What CTF teaches, in the end, is not the specific exploits. It is the habit of reading any system with the attacker's eye. That habit, installed in a developer's unconscious review process and reinforced across years of occasional practice, is worth more than any number of classroom hours, any compliance-mandated annual training, or any checklist-driven secure coding standard. The frameworks and standards tell the developer what to do. CTF teaches the developer to see why.