Your organization passed its PCI DSS 3.2.1 assessment every year for five years with a twenty-minute annual compliance video that every developer clicked through on mute. That era is over. PCI DSS 4.0.1's future-dated requirements became fully effective on 31 March 2025, which means 2026 is the first assessment cycle where Requirement 6.2.2 is evaluated for real. And 6.2.2 does not describe what your current secure coding training program is. This guide walks the actual language of the requirement, what qualifies and what does not, why most compliance training fails the new bar, and how to build an application security training program that your QSA will sign off on — the first time.
Why 2026 Is Different
PCI DSS 4.0.1, finalized in June 2024, carried forward the structural shift from 3.2.1 that PCI 4.0 introduced in 2022. A block of new requirements was designated as "best practice" until 31 March 2025, after which they became mandatory for all entities in scope. Requirement 6.2.2 — annual secure coding training for developers — is in that block. For most organizations, 2025 assessments either ducked it via grandfather clauses or noted it with remediation timelines. Those workarounds are gone. A 2026 Report on Compliance has to document specific, assessable evidence that every in-scope developer received training that meets the requirement's wording, not the organization's preferred interpretation of the requirement's wording.
That distinction matters because the interpretation gap is large. Compliance teams read 6.2.2 and hear "annual developer training". Assessors read 6.2.2 and look for "secure coding training relevant to the developer's job function and the programming languages they use", with evidence that retention was measured and gaps closed. Those are not the same bar. The space between them is where most failed findings will land in the 2026-2027 assessment cycle, and where a meaningful portion of the current commercial secure coding training market does not actually reach.
What Requirement 6.2.2 Actually Says
The exact text of Requirement 6.2.2 in PCI DSS 4.0.1 reads — and this is worth reading twice, not skimming:
"Software development personnel working on bespoke and custom software are trained at least once every 12 months as follows: on software security relevant to their job function and development languages, and including secure software design and secure coding techniques. Also including, if security testing tools are used, how to use the tools for detecting vulnerabilities in software."
Every clause in that sentence is load-bearing. The assessor working your Report on Compliance will check each one against evidence you produce. Miss any clause and that piece of the requirement is a finding, not a pass.
"Software development personnel working on bespoke and custom software." Scope is everyone who writes or modifies in-scope application code. Frontend, backend, mobile, platform. Contractors count if they commit code. A developer who wrote two config changes in the last year is in scope. Your first evidence artifact is a roster of every person who touched the codebase in the past twelve months, cross-referenced against your training records.
"At least once every 12 months." Rolling 12-month window, per developer. Not a calendar year. If a developer completed training on 4 June 2025, they owe a new training cycle no later than 4 June 2026. Batch-training the entire engineering org in January every year is a common pattern that still technically complies, but any developer hired in February is out of cycle by the following January. Track per-person completion dates, not annual campaigns.
"On software security relevant to their job function." This is the clause that invalidates most off-the-shelf one-size-fits-all training. A backend engineer writing payment processing logic needs different content than a frontend engineer rendering checkout pages. A mobile developer needs mobile-specific threat content. A DevOps engineer writing Terraform for the cardholder environment needs IaC security content. One video for everyone does not satisfy this clause; the QSA will ask how the training was tailored and will want to see differentiated paths.
"And development languages." Language-specific content is explicitly required. Generic "watch out for SQL injection" training does not meet this bar. The developer needs to see SQL injection in the language they actually write — JavaScript for the Node.js engineer, C# for the .NET engineer, Java for the Spring engineer, Python for the Django engineer. This is the clause that catches the highest number of programs that assumed they were compliant. Video-based generic training fails it without exception.
"Including secure software design and secure coding techniques." Both design and coding. Not just "here are ten vulnerabilities". The training needs a design-level component — threat modeling concepts, trust boundaries, principle of least privilege — and a coding-level component where the developer practices writing or reviewing code that applies the techniques. Theory-only training misses half the requirement.
"Also including, if security testing tools are used, how to use the tools for detecting vulnerabilities." Conditional clause. If your organization uses SAST, DAST, SCA, or IAST — and if you are in PCI scope, you almost certainly do, because 6.3 and 11.3 require vulnerability identification — then training on how to use those tools is part of the requirement. Not "they exist in our stack". How to use them, including interpreting their output and acting on it.
"Relevant to Job Function and Development Languages" in Practice
The job function and language clauses are where programs most often quietly fail. A QSA working the 2026 cycle will ask three specific questions about this, and the answers have to be in writing, not verbal.
Question one: "How did you determine what is relevant for each developer's job function?" The correct answer is a documented mapping. Role X (backend engineer on payment service) has training requirements A, B, C. Role Y (frontend engineer on checkout UI) has requirements B, D, E. Role Z (mobile engineer on wallet app) has requirements F, G, H. The mapping is usually a living document maintained by the security team in collaboration with engineering leadership. It is not a generic "all developers do the same training" policy, because that policy cannot demonstrate relevance.
Question two: "How does the training cover the specific languages your developers use?" A correct answer names the languages and shows the language-specific content. Node.js, TypeScript, Java, Python, C#, Go, Swift, Kotlin, PHP — whatever is actually in your codebase, the training needs corresponding material. For each language, the content should include at minimum: injection defenses (SQL and OS command), authentication and session handling, authorization checks, input validation, output encoding, cryptography primitives, and logging. A program that teaches SQL injection in pseudocode only does not demonstrate language-specific coverage.
Question three: "What evidence do you have that each developer completed the training relevant to their specific role and languages?" The answer is completion records that tie each developer to the specific role-mapped content they consumed, with timestamps and pass criteria if any assessment was included. "Everyone completed the same course" is the wrong answer here — even if the course contains all the languages, the assessor wants to see that each developer engaged with the content relevant to them, which usually means per-language modules with per-developer completion tracking.
The 6.2.4 Connection: OWASP, Common Attacks, and the Full Training Picture
Requirement 6.2.2 does not stand alone. It sits inside a cluster of related requirements — 6.2.1 (documented software development practices), 6.2.3 (code review before release), 6.2.3.1 (manual code review for bespoke software), and 6.2.4 (software engineering techniques and other methods to prevent or mitigate common software attacks). The assessor reads them together. A training program that meets 6.2.2 on paper but does not cover the specific attack classes named in 6.2.4 is a finding against both requirements at once, because the training is supposed to equip developers to apply 6.2.4's techniques. Findings are not abstract bookkeeping — see what PCI DSS non-compliance actually costs for the full breakdown of monthly acquiring-bank fines, card-brand assessments, and per-card breach liability that attach when training-program findings escalate into a real compliance failure.
Requirement 6.2.4 explicitly names the attack categories the program must address. The list reads almost exactly like the OWASP Top 10, which is not a coincidence — the PCI Council's guidance documents reference OWASP directly. In practice, this means a defensible application security training program in 2026 includes dedicated coverage of injection attacks, attacks on authentication and session management, attacks on access control, attacks on cryptographic implementations, and attacks via insecure deserialization or business logic. Any serious owasp top 10 training program that your team already runs can satisfy most of 6.2.4's content requirements if — and only if — it is delivered in language-specific form and tied to developer job functions per 6.2.2.
The practical bridge between the two requirements is worth stating explicitly. 6.2.4 describes what developers must be able to prevent. 6.2.2 describes the training that teaches them to prevent it. The two requirements have to be satisfied by the same program, documented the same way. A QSA will ask for evidence linking specific training modules to specific 6.2.4 techniques, and will note gaps where a named technique in 6.2.4 does not map to any training module.
What PCI DSS Training Actually Means for Developers in 2026
Most of the writing about pci dss training is aimed at compliance leads and QSAs. The requirement, however, lands on a developer's keyboard — not a compliance team's spreadsheet. Reading 6.2.2 from the developer's seat changes how the rule feels. It is not a blanket corporate obligation to be cleared with a click-through video. It is a specific, per-person, per-language capability requirement that your employer has to be able to evidence against your name every twelve months. Everything below is what that actually means in practice for the individual developer whose day job is writing code in PCI scope.
Why PCI DSS Training Is Not What Your HR Portal Called It Last Year
In the 3.2.1 era, pci training was almost always a single mandatory annual video — twenty minutes, a three-question quiz, a completion certificate in an HR archive. That format satisfied a looser reading of the older standard because the older standard treated training as a blanket control. 4.0.1 deliberately split developer training (6.2.2) from general security awareness (12.6.1). If the training your employer is asking you to complete is the same training your finance team and your receptionist completed, it is almost certainly the wrong artifact for 6.2.2. Awareness training covers social engineering, password hygiene, physical security — content appropriate for everyone, covered separately in our PCI DSS awareness training guide for Requirement 12.6.1. Developer training covers injection defenses, authentication patterns, cryptographic usage, and framework-specific pitfalls — content only meaningful if you write code. The two have different requirements, different evidence expectations, and different assessment treatment. They are not interchangeable.
What "Relevant to Your Job Function and Development Languages" Looks Like for You
If you are a Node.js backend engineer on a service that processes cardholder data, qualifying training is supposed to show you SQL injection in JavaScript — not pseudocode — with parameterized queries in the actual pg or Prisma or Knex pattern your codebase uses. It should show you JWT validation pitfalls in the jsonwebtoken library idioms your team has, and framework-specific concerns for Express or Fastify or NestJS. If you write Java for a payment adapter, the training is supposed to show the same concepts in Java, in the Spring or Quarkus or Micronaut idioms your team actually ships. A Python engineer on a Django billing service gets Django-specific content. A mobile engineer on a wallet app gets iOS or Android content in Swift or Kotlin. The principle is simple: the code the training shows should look like the code you already write. If the examples are in a language you do not work in, or are in pseudocode with a "principles transfer" disclaimer, the program has failed the language-specific clause regardless of whether anyone inside your organization has noticed yet.
How Much Time This Should Legitimately Take
The honest answer varies by role, but here is a defensible floor. A developer working primarily in one language on in-scope code, receiving 6.2.2-compliant training that includes design-level content, language-specific vulnerability prevention, hands-on practice, and assessment, should expect a minimum of four to six hours of training annually — often more. A developer working across languages (a common pattern on smaller teams) runs longer. If your compliance team is offering you a twenty-minute annual video as your sole 6.2.2 artifact, that is not a program that has been upgraded for 4.0.1; it is a 3.2.1-era program still being deployed for the new standard. The time investment is meaningful by design. The Council's position, reflected in the standard text and in its supplementary guidance, is that passive short-form content cannot produce the applied capability the requirement describes.
What Happens If You Miss the Deadline
The rolling twelve-month window in 6.2.2 is per-developer, not per-organization. If your last qualifying training was completed on 4 June 2025, the next cycle must be completed no later than 4 June 2026 for your record to keep the organization's compliance posture clean. Missing the deadline does not immediately trigger a compliance failure — QSAs assess findings against documented programs and remediation timelines — but a developer whose training is out of window at the point the Report on Compliance is compiled is a finding against the program, which becomes a corrective-action item for that cycle and a target for re-examination on the next. Most organizations track this with an HR system or LMS that sends reminders at sixty and thirty days before the deadline. If your organization does not, the practical responsibility for tracking your own training date falls to you, because the organization-level reminder will not catch what the organization is not instrumented to see.
What to Ask If the Training You've Been Given Feels Off
If you are a developer whose instinct reading this section is "my training doesn't look like that", the two questions worth bringing to your security or engineering leadership are concrete and constructive. First: is the training we use mapped to the specific programming languages I work in, and is there documentation showing that mapping? Second: is our training structured to the 4.0.1 version of 6.2.2, or is it a carryover from 3.2.1 that has not been reviewed for language specificity and role relevance? Leadership usually appreciates the signal, because the gap is often invisible to teams who have not read the current standard text themselves. Reading 6.2.2 once is the cheapest action a developer can take to understand what an employer owes them under this regime — and what the developer can legitimately ask for if the current offering falls short.
Why Most "Compliance Training" Fails the 6.2.2 Bar
A surprising fraction of organizations heading into the 2026 cycle are relying on training programs that were designed for the 3.2.1 era and never updated. That era rewarded a specific pattern: a single annual video covering generic concepts, a three-question quiz at the end, a completion certificate, and an annual spreadsheet filed in a compliance share. That pattern does not meet 6.2.2, and the reason it does not meet 6.2.2 is structural, not cosmetic. Walking the failure modes is the fastest way to see what a qualifying program looks like by contrast.
Failure mode one: generic, pan-language content. The typical compliance training product on the market teaches vulnerabilities in pseudocode or in one arbitrary language the vendor picked. A QSA asking "show me how this covers your Node.js team's actual languages" gets a shrug and a promise that the principles transfer. The principles do transfer, for developers who already know them. The training is supposed to be for the developers who do not. Principle-only content fails the language-specific clause the moment it is scrutinized.
Failure mode two: passive delivery, zero practice. A watched video is not evidence that a developer can apply a technique. Retention research on passive training has been clear for decades — single-exposure lectures deliver well under 20% retention at six weeks. 6.2.2 does not explicitly require hands-on practice, but the surrounding framework (6.2.4 expects the techniques to be applied, audit findings get reopened when vulnerabilities keep appearing in the same categories) means a program that cannot demonstrate retention will be re-examined on the next cycle. The assessors are getting more sophisticated about this with each cycle.
Failure mode three: one-time annual batch. The compliance team picks a week in January, sends every engineer a link, tracks completions, and moves on until next January. Problem one: developers hired after January are out of cycle by the following January. Problem two: the rolling 12-month clock was the explicit design choice, not an accident. A calendar-year batch only complies if completion records are tracked per person with individual due dates, which most "batch" programs do not do. Problem three: content shown in January is not remembered in November when the developer is writing payment code. The annual ritual is better than nothing but worse than distributed reinforcement.
Failure mode four: no assessment or pass criteria. "Completion" without any measure of whether the developer learned anything is weak evidence for an auditor looking at the word "trained" in the requirement. The 4.0.1 guidance document does not strictly require a passing score, but a program that includes one — with remediation when a developer fails — is a materially stronger compliance posture than one that does not. This is the single cheapest upgrade most programs can make.
Failure mode five: no tie-in to the organization's actual vulnerabilities. If your last SAST run surfaced authentication issues in the payment API and your training program does not specifically reinforce authentication patterns for the team that owns that API, the program is disconnected from reality. The QSA may not catch this on first pass, but it shows up the next time a vulnerability in the same category is found in a subsequent scan. "We train annually" and "the same vulnerability keeps appearing" in the same Report on Compliance is an uncomfortable pairing.
Failure mode six: no provision for contractors, third-party developers, or code generated by AI tools. 6.2.2 covers "software development personnel working on bespoke and custom software" — that phrase explicitly includes anyone writing code that lands in the in-scope environment, regardless of employment status. Programs that only train full-time employees miss contractors. Programs that assume every line of code was written by a human miss the new reality of AI-assisted development, where a substantial fraction of commits began as a Copilot or Claude suggestion. The PCI Council has not yet issued specific guidance on AI-generated code, but the reasonable reading of 6.2.4's "common software attacks" clause is that the developer accepting an AI suggestion is responsible for the security of what they accepted, which means training has to prepare them to recognize AI-generated vulnerabilities. Ignoring this category is a finding waiting to happen.
What Actually Qualifies as Secure Coding Training Under 6.2.2
A qualifying program in 2026 shares five characteristics. These are not opinions about best practice. They are the intersection of the requirement's literal text, the PCI Council's supplementary guidance, and the patterns that QSAs have been publicly validating in 2025 assessments.
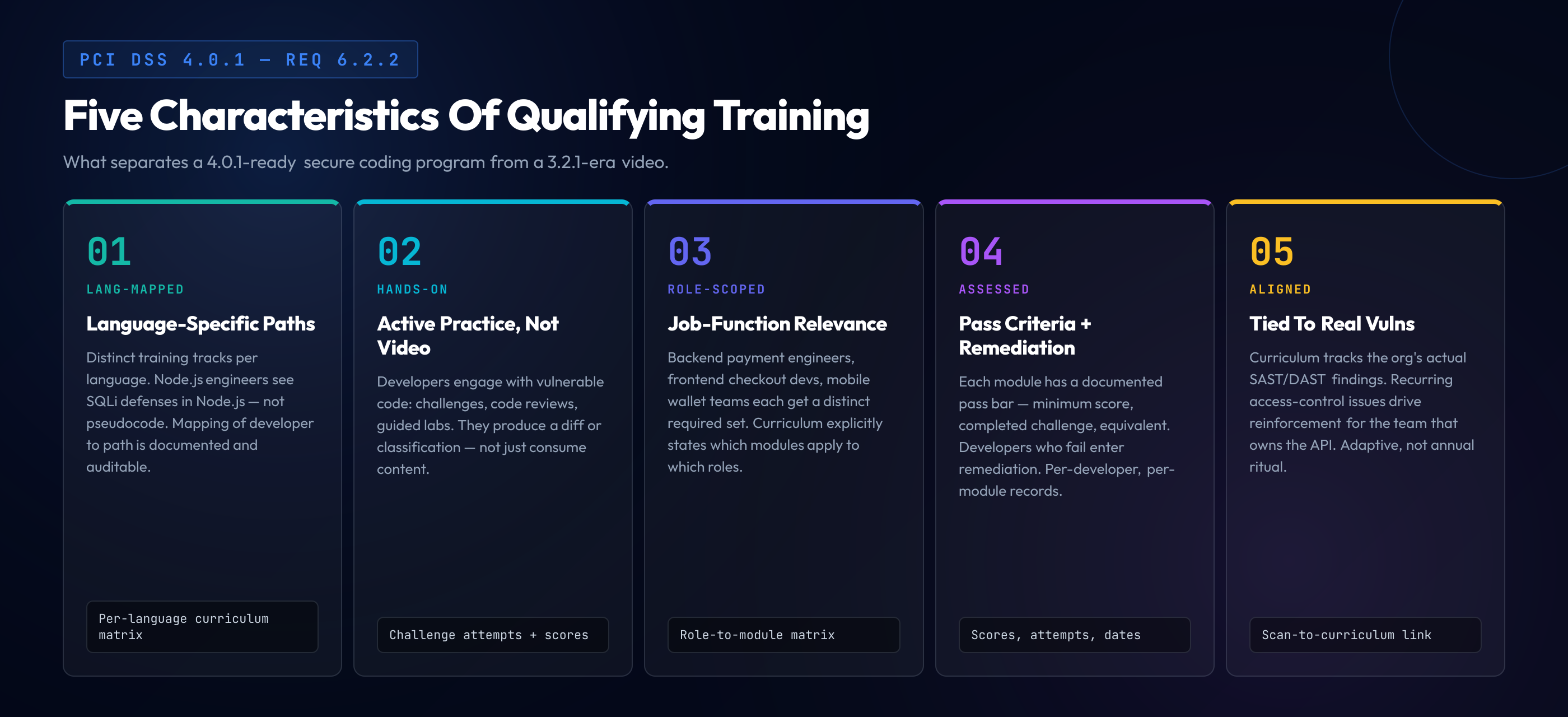
Characteristic one: language-specific content mapped to each developer's actual stack. The program publishes distinct training paths per language. A Node.js developer sees injection defenses, auth patterns, and input validation demonstrated in Node.js code. A Java developer sees the same concepts in Java. The mapping between developers and paths is documented and auditable. If your developers work in multiple languages, they take multiple paths, not a single "general" path.
Characteristic two: hands-on practice, not just video or text. A qualifying program includes a component where the developer engages with vulnerable code and practices identifying or fixing it. This can be interactive challenges, code review exercises with vulnerable pull requests, or guided labs. The key property is active engagement — the developer produces something (a classification, a diff, a written analysis) rather than just consuming content. Modern secure coding training platforms deliver this through challenge-based interactive formats, which is why they are replacing the video-first generation of tools.
Characteristic three: job-function relevance documented in the curriculum. The program's curriculum explicitly states which modules apply to which job functions. Backend engineers on payment services get a specific required set; frontend engineers on checkout UI get a different set; mobile developers get a different set again. Developers can take additional content beyond their required set, but the minimum is tailored to their role.
Characteristic four: measurable completion with assessment. Each training module has a pass criterion — a minimum score on an assessment, successful completion of a challenge, or equivalent. Developers who do not pass receive remediation. Completion records track per-developer, per-module, with dates and scores. A spreadsheet of names and "completed yes/no" entries is weaker evidence than a system that captures attempt counts, scores, time spent, and module-level completion.
Characteristic five: alignment with the organization's observed vulnerability profile. The program reflects what the organization's code actually looks like. If SAST is surfacing recurrent access control issues, the training emphasizes access control for the teams involved. If DAST finds authentication gaps, the auth module is reinforced. This characteristic is not in the 6.2.2 text itself but it is the factor that distinguishes a training program that prevents future findings from one that simply satisfies this year's audit.
The Annual Cycle and What Evidence the Assessor Wants
An assessor walking into your 6.2.2 evidence review in 2026 is looking for seven specific artifacts. Having all seven turns a potentially adversarial conversation into a short one.
- Training curriculum document. What modules exist, what each one covers, which languages and job functions each module applies to. Version-controlled, reviewed annually.
- Developer-to-role mapping. Every in-scope developer's current role, primary languages, and the specific curriculum path assigned to them. Tied to HR records so new hires and role changes update automatically.
- Per-developer completion records. For each developer, each assigned module, the date completed, the score or pass status, and any remediation undertaken.
- Currency verification. A report showing every developer's most recent training date and whether they are within the rolling 12-month window. Developers out of window are flagged for re-training, with documented timelines.
- Tool training evidence (if tools are used). Separate records showing developers trained on how to use the SAST, DAST, SCA, or IAST tools deployed in the environment.
- Gap analysis. A documented analysis showing how the training curriculum maps to 6.2.4's attack categories, identifying any gaps and the remediation plan to close them.
- Program review record. Evidence that the training program itself is reviewed at least annually — the curriculum updated, new attack categories added, feedback from developers and from the organization's incident data incorporated.
Producing these seven artifacts is, in practice, the single highest-value thing a compliance team can do to prepare for the 2026 cycle. The artifacts also turn out to be useful beyond compliance — they are the same artifacts a CISO needs to demonstrate program maturity to a board, the same artifacts a due-diligence team asks for in an acquisition, and the same artifacts that a SOC 2 CC1.4 or CC7.2 review expects. One program, multiple uses.
How Training Integrates with the Rest of the SDLC
A training program that passes 6.2.2 in isolation is an island. A training program that ties into the rest of your secure development lifecycle is a competitive advantage. The integration points matter for the QSA — 6.2.3 (code review) and 6.2.4 (engineering techniques to prevent common attacks) are adjacent requirements that the assessor will ask about in the same conversation — and they matter for the actual security posture the training is supposed to produce.
Code review (6.2.3). The training should equip developers to perform the manual code review that 6.2.3.1 requires for bespoke software. If your training teaches a developer to recognize SQL injection in Java, your code review process should require them to actually apply that recognition when reviewing a teammate's pull request. Integration here is as simple as a code review checklist that explicitly references the training topics, and a pull request template that prompts the reviewer to check for the specific vulnerability categories covered in the curriculum.
Engineering techniques (6.2.4). 6.2.4 requires engineering techniques that prevent common attacks. Parameterized queries, output encoding, framework-level access control, cryptographic libraries — the standard set. The training should demonstrate each technique in the languages the team uses and should be reinforced by linters, static analyzers, and framework configuration that make the secure path the easy path. A training that teaches "use parameterized queries" pairs naturally with a SAST rule that blocks raw string concatenation into SQL calls. The two reinforce each other, and the assessor sees both in the 6.2 conversation.
Vulnerability management (6.3 and 11.3). When a new vulnerability class emerges or an internal or external PCI vulnerability scan finds a recurring pattern, the training curriculum should update within the next cycle. This is where the program review artifact from the evidence list earns its keep. Documenting that the training curriculum was updated in Q2 2026 to cover a specific class of issues after they appeared in internal scans turns "we train annually" into "we train adaptively", which is materially stronger compliance language and materially better security.
Developer onboarding. New developers should receive 6.2.2-compliant training as part of onboarding, before they are assigned to bespoke software work. A common pattern is a mandatory training module as part of week-one onboarding, with the full curriculum completed within the first 60 days. This pattern also solves the rolling 12-month window problem by anchoring each developer's clock to their start date rather than to a calendar event.
Building a Program That Qualifies: The Concrete Checklist
If you are the security leader or compliance manager walking into this as new-in-role, or if you are auditing your existing program against 6.2.2 for the first time, here is the end-to-end checklist. Each item corresponds to evidence the QSA will ask about. A program that has checked all fifteen is in strong position for the 2026 cycle.
- Developer roster. Complete list of in-scope developers (employees, contractors, anyone who has committed code to the bespoke software environment in the past 12 months), tied to HR or access management records.
- Role-to-curriculum map. Documented mapping of each developer role to the specific training modules they must complete. Reviewed annually.
- Language coverage. Every programming language in the in-scope codebase has corresponding training content. Gaps identified and plan to close.
- Design + coding content. Curriculum includes both secure design topics (threat modeling, trust boundaries, defense in depth) and secure coding techniques (language-specific vulnerability prevention).
- Hands-on practice component. At least one module format where developers produce output — challenges, exercises, code reviews — not passive video only.
- 6.2.4 attack coverage. Mapping of curriculum to the attack classes that 6.2.4 and OWASP Top 10 require developers to be able to prevent.
- Tool training. Separate modules on how to use each security testing tool in the environment — SAST, DAST, SCA, IAST — if any are deployed.
- Assessment and pass criteria. Each module has a documented pass criterion; developers who do not pass enter remediation.
- Per-developer completion records. System-of-record tracking training completion per person, per module, with dates and scores.
- Rolling 12-month compliance. Report showing every developer's most recent training is within 12 months, with automated alerting on approaching deadlines.
- New-hire onboarding. Mandatory training module completed before new developers commit to in-scope code, with full curriculum within 60 days.
- Contractor coverage. Training requirements apply to contractors and external developers writing in-scope code; evidence of completion retained.
- AI-assisted code coverage. Training addresses review of AI-generated code for the vulnerability patterns common to model output; policy clarifies developer accountability for accepted suggestions.
- Annual program review. Documented annual review of the curriculum, with updates based on new attack classes, internal incident data, and developer feedback.
- Integration with code review. The code review checklist used in 6.2.3 references the training topics; reviewers are expected to apply what the training taught.
Choosing a PCI DSS Compliance Training Platform for Developer Teams
If your organization is selecting a pci dss compliance training platform for the 2026 cycle, the number of vendor options on the market has not been this high in a decade — but the number of platforms that actually satisfy the literal text of 6.2.2 has not caught up to the marketing. The failure modes described earlier in this guide map directly to specific architectural choices a training vendor has made. Walking the concrete evaluation criteria exposes which vendors are designed for the 4.0.1 bar and which are still shipping 3.2.1-era products under a refreshed UI.
The Six Questions Every Vendor Should Answer Specifically
A qualifying pci dss training platform for developer teams should answer these six questions with documentation, not vague assurances. Each question maps to a clause in the requirement; an evasive answer to any of them is a signal about the product's fit.
1. Which programming languages do you deliver native content in, and how do I see the delta between your coverage and my team's stack? The correct answer is a published language matrix the vendor will put in writing. The weak answer is a claim that "our content applies to all major languages" or "the principles transfer" — both of which fail the language-specific clause the moment the QSA asks for evidence.
2. Is your training challenge-based or video-based at the core? The correct answer is challenge-based, with video as supplementary explanation rather than the primary delivery mechanism. Video-first products will usually describe "interactive elements" in their pitch; the honest framing is that interactive elements in a video-first product are usually knowledge-check quizzes, not code-level exercises where the developer produces a diff or a classification. The standard does not forbid video, but the "hands-on practice" clause is a property of the architecture, not of a feature toggle.
3. How does role-mapping work — can I assign a different curriculum path to my Node.js backend team versus my React frontend team versus my Swift mobile team? The correct answer is a role-to-curriculum mapping controlled by the security lead, with per-learner assignment visibility. The weak answer is a single catalog learners self-select from. 6.2.2's "relevant to job function" clause is structurally about assignment, not availability; a library of great content is not the same artifact as a mapping that proves each developer consumed what their role required.
4. What does per-developer completion evidence look like when my QSA asks for it? The correct answer is a system-of-record export: per-learner, per-module, timestamps, scores, attempt counts, retention evidence. The weak answer is a PDF summary with aggregate completion percentages, or a CSV of names and "completed: yes" entries. The assessor is looking for per-person traceability; summaries are weaker evidence than raw records.
5. How does content stay current with new attack classes? The correct answer is a versioned content library with a published changelog, or an editorial roadmap showing how new threat categories get incorporated. The specific frontier matters: AI-generated code review, prompt injection, MCP-related threats, and other attack classes that emerged through 2025-2026 should already be represented or on the near-term roadmap. A program that has not been updated since the 3.2.1 era is a program that will keep a QSA re-asking the same questions year over year.
6. What is the total time commitment per developer per year? The correct answer is a number in hours with a breakdown per module. A vendor that cannot answer this has not benchmarked its program against the 6.2.2 bar, which means the buyer cannot either.
Red Flags That Signal a 3.2.1-Era Platform
Several product signals reliably distinguish platforms architected for the older standard from those built for 4.0.1. None are deal-breakers in isolation, but in combination they indicate a vendor whose product team has not ingested the new requirement.
The library is browsable by topic, with self-service completion. This is appropriate for awareness training. It is not how 6.2.2-compliant programs are structured — job-function relevance has to be assigned, not self-selected, because the assessor wants evidence that each developer consumed the content mapped to their role, not content they happened to pick.
The primary content format is video, with quizzes. The standard does not forbid video, but a video-first product cannot credibly deliver the language-specific hands-on practice the requirement expects. When the vendor's demo opens with a sizzle reel of a slick lesson video, watch how fast they can show the actual coding exercise where a learner produces a diff.
Reporting is a PDF with completion percentages. A QSA wants per-developer, per-module records with attempt details. A completion percentage is a summary, not evidence. Platforms that cannot generate per-learner exports force compliance teams to rebuild that evidence manually, which is exactly the labor 6.2.2 was designed to eliminate.
Pricing is flat per-user regardless of role. Role-structured content usually prices differently across tiers, because content production cost varies by tier. Uniform per-seat pricing often signals the vendor has not actually differentiated content by role — they priced a library, not a mapped curriculum.
Budgeting and Rollout Timeline
A realistic rollout of a 6.2.2-compliant training program for a hundred-developer organization, from vendor selection to first full compliance cycle, runs three to four months: vendor selection (two to three weeks), content customization and role mapping (three to four weeks), pilot rollout with ten to fifteen developers for feedback (two to three weeks), full rollout (two to three weeks), first assessment-ready evidence package (one to two weeks). Organizations that try to shortcut to a four-week rollout usually miss the role-mapping and language-specificity steps, which is the exact gap the QSA will find on audit. The timeline compresses for smaller organizations and lengthens for larger ones, but the sequence — select, map, pilot, roll out, evidence — does not change, and skipping a step does not save time on the assessment side; it just defers the cost to the corrective-action phase.
Built for the 4.0.1 Bar from Day One
SecureCodingHub delivers language-specific, challenge-based secure coding training with per-developer completion tracking, role-mapped curricula, and integrated assessment — the exact architecture the Council intended Requirement 6.2.2 to describe. If you are preparing for the 2026 assessment cycle and want to walk through how our program maps to your team's stack, we are happy to show you directly.
See Our PCI DSS ProgramClosing: The 2026 Assessment Is About Substance, Not Paperwork
The shift from PCI DSS 3.2.1's annual compliance video to 4.0.1's role-specific, language-specific, assessed training program is not a paperwork upgrade. It is the Council formalizing what the security community has known for years — generic security training does not produce secure code, and the organizations being breached are rarely the ones without any training at all. They are the ones whose training existed to satisfy an auditor rather than to equip a developer.
The 2026 assessment cycle is the first time this shift is enforced with teeth. QSAs have been sharpening their 6.2.2 questions through the 2025 cycle and will be more rigorous through 2026 and 2027 as the Council continues to publish guidance. Organizations that treated 2025 as the year to start preparing are in good shape. Organizations still running a 3.2.1-era video program are not, and the gap is harder to close retroactively than it looks — an audit window closing in three months is not enough time to stand up a language-specific, role-mapped curriculum from nothing.
The good news is that the investment pays off beyond compliance. A secure coding training program that qualifies for 6.2.2 also serves SOC 2, ISO 27001, HIPAA, and the emerging EU Cyber Resilience Act requirements. The developer skills it produces are the same skills that reduce vulnerability density in production code — the ones that do not just pass audits but prevent breaches. An application security training program built to these standards is not a compliance line item. It is part of how your organization ships safer software.
If you are the person deciding what to tell your CFO about the budget line for secure coding training in the 2026 plan, the framing is straightforward. 6.2.2 is assessable for real now. A qualifying program is not a nice-to-have. It is the difference between a clean Report on Compliance and a finding that will be reopened until the program exists. Budget accordingly. And if you need to show the CFO what a qualifying program actually looks like — role-mapped paths, language-specific content, hands-on challenges, per-developer tracking — SecureCodingHub was built around exactly these requirements. That is why we wrote this guide.