If you ship code at a company that takes security seriously, sooner or later a finding from a bug bounty program will land in your queue — a triaged report from an external researcher, a reproduction that works, and an SLA on the fix. The recurring question from developers seeing this for the first time is the obvious one: what is a bug bounty program, who are these researchers, why is the company paying them, and what is expected of you when the ticket arrives? This guide answers those questions end to end. It walks how bug bounty programs work, the major bug bounty platforms in 2026, the distinction between bug bounty vs penetration testing vs vulnerability disclosure, what determines whether a program succeeds or stalls, and what happens on the developer's side once a finding is validated.
What Is a Bug Bounty Program?
A bug bounty program is a structured arrangement in which an organization invites external security researchers to find and report vulnerabilities in a defined scope of its systems, in exchange for monetary rewards — bounties — paid out when a finding is valid, in-scope, and previously unknown. The premise is straightforward: the organization's internal team and contracted pentesters cannot test as broadly or as continuously as a global pool of independent researchers, so the program creates a legal and economic channel for that pool to surface real vulnerabilities and get paid for them.
Programs come in two flavors. A public program is open to any researcher who registers on the hosting platform — anyone can read the scope, test in scope, and submit. A private program is invitation-only; the organization picks researchers based on platform reputation and skills relevant to its stack. Most mature programs start private and graduate to public once the team can absorb the volume of submissions a public program produces.
A related but distinct concept is the Vulnerability Disclosure Program (VDP). A VDP is a public commitment to receive vulnerability reports without legal threats, but it does not pay out. The VDP exists to give well-intentioned researchers a safe channel to report findings; the bug bounty program adds the economic incentive on top. Most security-mature organizations run a VDP as the legal-safe-harbor backstop and a bug bounty program as the proactive, paid layer above it.
Bug bounty programs are now common at organizations of every size. Google, Microsoft, GitHub, Shopify, Apple, every major fintech, and an increasing share of mid-market SaaS companies run them. The pattern is no longer exotic — for any developer working on internet-facing software, encountering a bounty-sourced ticket is now a routine event rather than a rare one. The basic flow on every program is the same: researcher finds a bug, researcher submits to the platform, triage validates, the engineering team fixes it, the researcher gets paid.
How Bug Bounty Programs Work
The mechanics of a bug bounty program live in three documents: the scope, the rules of engagement, and the severity rubric. Together they define what researchers can test, how, and how much they get paid for what they find.
Scope is the asset list — the specific domains, applications, APIs, mobile apps, and sometimes hardware that researchers are authorized to test. A good scope is precise: *.example.com in scope, marketing.example.com out of scope, the iOS app on App Store in scope, third-party integrations out of scope. Vague or overly broad scopes are a leading cause of disputes, because researchers test what they reasonably believe is in-scope and the program later argues it wasn't.
Rules of engagement define what testing methods are allowed. Most programs prohibit denial-of-service testing, automated scanners that produce traffic floods, social engineering of employees, and any testing that would access real user data. Programs that want clean reports often require researchers to use designated test accounts and refrain from pivoting beyond the initial finding. Crossing the rules of engagement turns a researcher's good-faith work into legally risky behavior — the same finding that would have earned a bounty becomes a violation if it was found by methods outside the rules.
Severity rubrics define the payout tiers. Most programs use either CVSS v3.1/v4 scores mapped to tiers (Critical / High / Medium / Low) or the platform's own rubric — Bugcrowd's Vulnerability Rating Taxonomy (VRT) is the dominant alternative. The rubric matters because it determines payout amounts and sets researcher expectations: a stored XSS that exfiltrates session tokens is high or critical depending on impact and earns five-figure payouts at top programs; a self-XSS or low-impact information disclosure earns the floor of the scale or nothing.
The submission flow is consistent across platforms. Day 0: researcher submits a report through the platform with reproduction steps, expected impact, and proposed severity. Day 1-3: the program's triage team — either in-house or platform-managed — validates the finding, dedupes against existing reports, and assigns severity. Day 7-30: the engineering team reproduces, fixes, and ships, with critical findings on a tighter SLA than lower-severity issues. Once the fix is verified, the researcher is paid and the report typically remains private until the organization opts to disclose. The flow surfaces vulnerability classes ranging across the OWASP Top 10 and beyond — what shows up depends on what your application's attack surface actually exposes.
The Major Bug Bounty Platforms in 2026
The platform layer is where most bug bounty programs live, because running a program requires triage capacity, payout infrastructure, researcher reputation systems, and legal scaffolding that very few organizations want to build in-house. The 2026 platform landscape has consolidated around five dominant options, plus a small set of self-hosted exceptions.
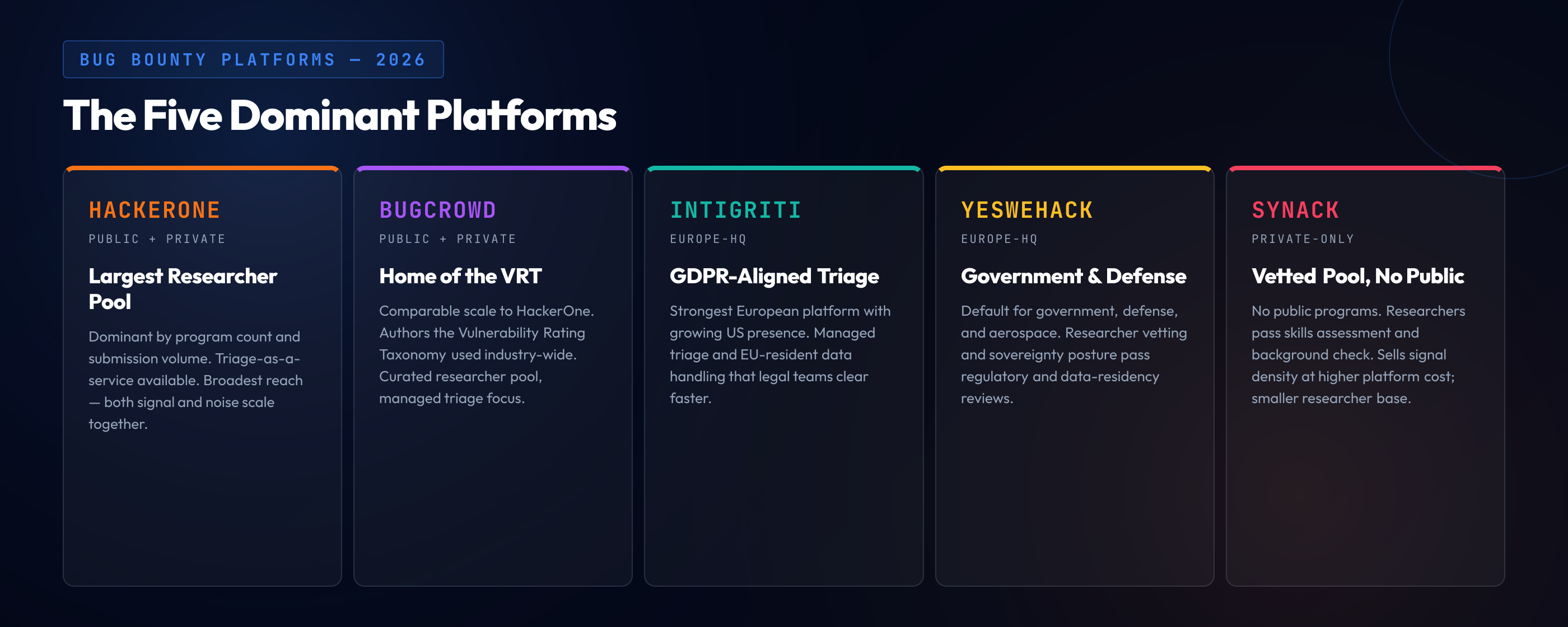
HackerOne is the largest platform by program count and researcher base. It hosts public and private programs across most industries, runs a researcher reputation system that programs use to filter invitations, and provides triage-as-a-service for organizations that don't want to staff triage internally. Its size means a public HackerOne program reaches the broadest pool of researchers and produces the highest volume of submissions — both the high-quality reports and the noise.
Bugcrowd is comparable in scale to HackerOne and is the home of the Vulnerability Rating Taxonomy, an open severity rubric that many programs adopt even outside the platform. Bugcrowd emphasizes managed triage and a curated researcher pool ranked by skill and prior performance, which appeals to organizations that want signal density over raw submission volume.
Intigriti is the dominant Europe-headquartered platform and has been growing US presence steadily. Its differentiation is strong managed triage, GDPR-aligned data handling that European organizations find easier to clear with legal, and a researcher community that skews toward European time zones.
YesWeHack is also Europe-based and is particularly strong with government, defense, and aerospace customers. Its researcher vetting and platform compliance posture make it the default choice for organizations that have regulatory or sovereignty constraints on where research data lives.
Synack is the private-only platform — there are no public Synack programs. Its researcher pool is vetted through a skills assessment and background check, and the platform sells itself on signal quality and the absence of the noise that public programs generate. The tradeoff is a smaller researcher base and a higher platform cost.
A handful of FAANG-scale organizations run self-hosted programs — Google's Vulnerability Reward Program, Microsoft's bounty programs, Apple Security Bounty — without a platform layer. This is uncommon and usually only viable at the scale where the organization has a dedicated security team large enough to handle triage and a brand strong enough that researchers will register directly. For everyone else, a platform is the default. GitHub Security Advisories is a related-but-distinct channel for OSS maintainers to coordinate CVE assignment and disclosure on open-source repositories — it is a coordination tool, not a bounty platform.
Bug Bounty vs Penetration Testing vs VDP
The three nearby concepts — bug bounty, penetration testing, and VDP — are routinely confused, including by people building security programs. They are not interchangeable. They answer different questions and they fit different parts of a security program.
Penetration testing is a paid engagement with a fixed scope, fixed time window, and a small named team. The deliverable is a report — findings, severity ratings, recommendations — produced at the end of the engagement. Pentests are deep, structured, and well-suited to compliance requirements that demand a documented test by a qualified third party. They are also bounded: the test ends when the engagement ends, the team that ran it is small, and any vulnerability introduced after the test exists undetected until the next test.
Bug bounty is continuous, broad scope, with many independent researchers. The deliverable is individual reports as they are found, validated, and paid. Bug bounty trades the depth and structure of a pentest for breadth and continuity — there are far more researchers looking, and they look continuously rather than within a fixed window.
VDP is the legal-safe-harbor channel: a public commitment to receive vulnerability reports without threatening the reporter, with no payout obligation. The VDP catches the well-intentioned drive-by reports that would otherwise have nowhere to go, and gives the program a documented commitment that researchers acting in good faith will not be prosecuted.
| Dimension | Pentest | Bug bounty | VDP |
|---|---|---|---|
| Cadence | Time-boxed engagement | Continuous | Continuous (passive) |
| Researcher pool | Single contracted team | Many independent researchers | Anyone who reports |
| Payout | Fixed engagement fee | Per-finding bounty | None |
| Scope | Narrow, predefined | Broad, listed assets | Whatever the reporter found |
| Deliverable | Report at end | Individual reports as found | Individual reports as received |
| Compliance fit | Strong (audit-ready) | Supplementary | Required by some frameworks |
Most mature programs run all three: pentest for depth and compliance, bounty for breadth and continuous coverage, VDP as the legal backstop. Treating them as alternatives rather than complements is the most common mistake — a bounty program does not replace a pentest, a pentest does not replace a VDP, and a VDP without a bounty doesn't motivate the researchers who would have produced the most valuable findings.
What Makes a Bug Bounty Program Succeed (or Fail)
Not all bug bounty programs work. The pattern that separates the productive programs from the stalled ones is consistent across platforms and industries. The success determinants are practical and the failure modes are recognizable.
Clear scope. Researchers need to know exactly what is in-scope before they invest time. A scope that says "the API" without listing endpoints, or that includes wildcards without exclusions, generates disputes and discourages serious research. The strongest programs publish an asset list with explicit inclusions and exclusions, version-controlled changelog when the scope changes, and clarification channels for edge cases.
Competitive payouts. Top programs in 2026 pay $500 to $1,500 for low-severity, $2,000 to $5,000 for medium, $5,000 to $15,000 for high, and $15,000 to $50,000 or more for critical findings — with the highest single payouts at FAANG and major fintech programs reaching six figures for chained criticals. Programs paying floor rates compete poorly for researcher attention, because researchers prioritize programs where the expected payout per hour is highest. A program offering $50 for high-severity findings will be ignored by anyone with options.
Responsive triage SLA. Researchers leave platforms with slow triage. The programs that retain top researchers respond to submissions within 24-72 hours, even if only to acknowledge receipt. Programs where reports sit for weeks before any response see their submission quality decline as researchers stop bothering. Triage SLA is the single biggest predictor of which programs attract reputation-sensitive researchers.
Tight integration with engineering workflow. Once a finding is triage-validated, it has to land in the engineering team's normal ticketing system with enough context for a developer to act. Programs that route bounty findings to a side channel that engineers ignore produce the worst outcome: researchers paid, reports filed, vulnerabilities not fixed.
Public transparency. Hall-of-fame pages, average-payout disclosures, and disclosed reports — the public artifacts of an active program — signal to researchers that the program rewards quality work and has receipts. Programs that stay opaque struggle to attract researchers who could choose between a transparent competitor and an unknown.
The failure modes are the negation of each of the above. Vague scope produces dispute culture — researchers test what they think is in-scope, the program rejects the finding as out-of-scope, the relationship sours. Low payouts produce researcher disengagement — reports thin out and the ones that arrive are low-effort drive-bys. Triage backlog turns submissions into a black hole — the researcher waits, the response never comes, the researcher tells peers and the platform community and quality submissions stop arriving. Won't-fix-without-explanation closures from engineering teams burn researcher trust permanently. Legal threats over good-faith research are the nuclear failure mode and have ended programs that took years to build. The best programs avoid these patterns by treating researchers the way successful companies treat external auditors — as partners producing genuinely useful output, not as adversaries to be managed. Building that fluency on the developer side starts with teaching developers attacker mindset: the more your engineers think the way researchers do, the better they triage submissions and the less the program friction-burns the relationship.
From Submission to Fix: The Developer's Side
From the developer's seat, a bug bounty finding looks like any other security ticket — but with a few differences worth understanding. A triage-validated bounty ticket typically arrives with reproduction steps the researcher provided, a triaged severity, the affected code path or endpoint, and often a suggested mitigation. The triage layer has already verified the bug exists; the developer's job is to fix it correctly.
The developer's responsibilities on a bounty ticket are straightforward but each step matters. Reproduce the bug in the local or staging environment. The reproduction the researcher provided is usually correct, but local conditions sometimes differ — verify before fixing. Confirm the scope of impact. This is the step most often skipped and most often regretted. The reported endpoint may not be the only one with the flaw; if the root cause is a missing authorization check in a shared middleware, or an unsanitized template helper, every consumer of that pattern is also vulnerable. Search the codebase for the same pattern before assuming the fix is local. Write the fix, ideally in a way that addresses the underlying class rather than the specific instance. Write the regression test that proves the fix works and will keep working — this matters more for bounty findings than for routine bugs because the same researcher (or the next one) will retest the same flow, and a regression that lets the bug return is reputationally expensive. Ship through the standard release process for medium and lower-severity findings, or through a hotfix path for criticals where the program SLA demands faster turnaround.
The common pitfalls are the predictable ones. Under-fixing — patching the specific instance the researcher reported without addressing the broader pattern — leaves the codebase vulnerable to the next researcher who tests a different endpoint with the same flaw, and produces the embarrassing pattern of three researchers reporting variations of the same root cause across a year. Introducing regressions in the fix is its own failure mode; rushed fixes under bounty SLA pressure are more likely to break adjacent functionality than fixes written under normal pressure. Missing related endpoints with the same flaw is the under-fixing pattern's specific manifestation — the researcher reported the one they found, but the same vulnerability exists in three other places they didn't test.
One of the most underappreciated values of a sustained bug bounty program is the dataset it produces. Over a year, the program accumulates a labeled record of the actual vulnerability classes researchers find in your code: 30% XSS, 20% authentication issues, 15% access control, 10% SSRF, and so on. That distribution is one of the best signals available for what to train developers on next — if 30% of valid findings are XSS, the secure coding training program needs an XSS module that uses the team's actual code patterns, and the engineering team needs to internalize XSS prevention beyond the level it currently holds. Automated testing tools complement the bounty program but do not replace it; the IAST vs DAST vs SAST comparison covers how scanners catch a different fraction of the vulnerability surface than human researchers do, and the two layers together produce coverage that neither produces alone.
Should Your Organization Run a Bug Bounty Program?
Not every organization should launch a bug bounty program, and the ones that should have a sequence to follow. Launching too early or with the wrong structure is a known failure mode that damages security program credibility and can take years to recover from.
The prerequisites are concrete. A working VDP first — the VDP is the legal-safe-harbor floor and should exist before any payout layer. Without a VDP, well-intentioned researchers reporting findings have ambiguous legal standing, and the program risks the worst-case outcome of a researcher being threatened over a good-faith report. A security team that can triage — either in-house or via the platform's managed triage service — at the rate submissions will arrive. A public program on a major platform produces dozens of submissions per week; a team without triage capacity drowns. A developer team that can remediate within reasonable SLAs — if engineering cannot ship security fixes within the SLAs the program publishes, the program produces backlog rather than fixes. Executive support for the inevitable findings and the inevitable embarrassment of public disclosure on some of them.
The anti-pattern to avoid is launching a public bounty program before the basic security program is in place. Researchers will surface a flood of low-hanging fruit faster than the team can fix it, the backlog grows, the team gets blamed for slow remediation, and the program's reputation in the researcher community collapses. Once a program is known as a black hole, attracting back the researchers who left is harder than it was to attract them the first time.
The path that works in practice is staged. Stage 1: VDP first. A public commitment to receive reports, with no payout, that bounds legal exposure and creates the channel. Stage 1 can run for months while the security and engineering teams build the muscle to handle inbound reports without breaking. Stage 2: private invite-only program with 5-10 researchers. A small, managed researcher pool produces a controlled volume of submissions that the team can absorb, learn from, and use to calibrate triage and remediation processes. Stage 3: broaden the private program over several months, increasing the researcher count as the team demonstrates it can handle the volume. Stage 4: graduate to public only when the program's internal metrics — triage time, remediation time, payout consistency — are stable enough that public submission volume will not break them.
Cost is a real consideration. Platform fees for HackerOne, Bugcrowd, Intigriti and similar run from low five-figures to mid-six-figures per year depending on tier, with managed triage adding meaningfully on top. Expected payouts for a serious mid-market program land in the $50,000 to $500,000 range annually, with the variance driven by program scope, severity distribution, and how many critical findings show up. Triage capacity — in-house or platform-managed — is the third cost line and is often underestimated by programs budgeting only for platform fees and payouts.
Findings Without Developers Who Can Fix Them Are Just Reports
A sustained bug bounty program produces something rare and valuable: a labeled dataset of the vulnerability classes researchers actually find in your code. That data is one of the strongest signals for what to train developers on next, and it only translates into safer software when the engineering team is fluent enough to read the findings, identify the underlying class, and ship durable fixes. SecureCodingHub is how teams turn that data into developer fluency that closes the actual classes researchers find — not just the specific instances reported.
Request a demoClosing: Findings Without a Fix Are Just Reports
The recurring lesson from every successful bug bounty program is that the program is only as good as the engineering team's ability to do something with what it surfaces. Top programs in the industry — at Google, Microsoft, Shopify, GitHub, the major fintechs — are run by organizations whose developers are fluent enough in security to interpret findings, prioritize correctly, and ship durable fixes that address the underlying class rather than just the specific instance reported.
A sustained program produces an extremely useful dataset alongside the patched bugs: the actual vulnerability classes that researchers find in your code, weighted by how often each class shows up. That distribution should drive the topics in the secure coding training program, the depth of internal code review on each class, and the architectural priorities for the next iteration of platform-level mitigations. The teams that get the highest return on a bug bounty program treat it not as an isolated cost line but as part of an integrated loop: bounty surfaces classes, training builds developer fluency on those classes, fluent developers prevent the next instance, and the residual flow of bounty submissions calibrates the loop.
Complementary to the program, CTF for developers builds the offensive thinking that helps engineers triage incoming bounty findings, recognize the vulnerability class quickly, and reach for the right structural fix. The CTF builds the intuition; the bounty program produces the data that tells the team where to focus that intuition. Together they make the difference between a security program that absorbs findings reactively and one that systematically reduces the rate at which findings appear.