Most security teams are dramatically outnumbered. In a typical enterprise, you'll find one security engineer for every hundred developers. No amount of tooling or automation can close that gap on its own. The organizations that ship secure software at scale have figured out a different approach: they embed security knowledge directly into development teams through a security champions program.
The Scale Problem
Consider the math. A security team of five people is responsible for reviewing the output of five hundred developers. Those developers ship dozens of pull requests per day across multiple repositories, languages, and frameworks. Even if each security engineer could review ten PRs daily, that's fifty reviews against hundreds of changes. The backlog grows. Reviews become bottlenecks. Developers start seeing security as the team that slows them down.
Automated tools help — SAST scanners, dependency checkers, and secret detectors can catch the obvious issues. But the vulnerabilities that matter most are the ones tools miss: broken authorization logic, insecure business flows, race conditions in payment handling, and data exposure through overly permissive API responses. These require human judgment, and that judgment needs to exist inside the development team, not outside it.
What Is a Security Champion?
A security champion is not a full-time security engineer who happens to sit with developers. They are a developer first — writing features, fixing bugs, participating in sprints — who also serves as the security point-of-contact for their team. They're the person teammates turn to when they're unsure whether a particular implementation is safe. They're the one who raises a flag during design reviews when a proposed architecture has a trust boundary issue.
The role is part-time by design. Champions don't replace the security team. They extend it. They handle the common 80% — reviewing code for well-known vulnerability patterns (increasingly including AI-generated diffs), ensuring security controls are applied consistently, and answering basic security questions — so the central security team can focus on the remaining 20% that requires deep expertise: threat modeling new architectures, responding to incidents, and setting organization-wide security policy.
Identifying Champions
The most common mistake when building a champions program is selecting candidates based on seniority alone. The most senior developer on a team may be brilliant at system design but have zero interest in security. A champion who doesn't care about the role will treat it as a checkbox, and the program will fail quietly.
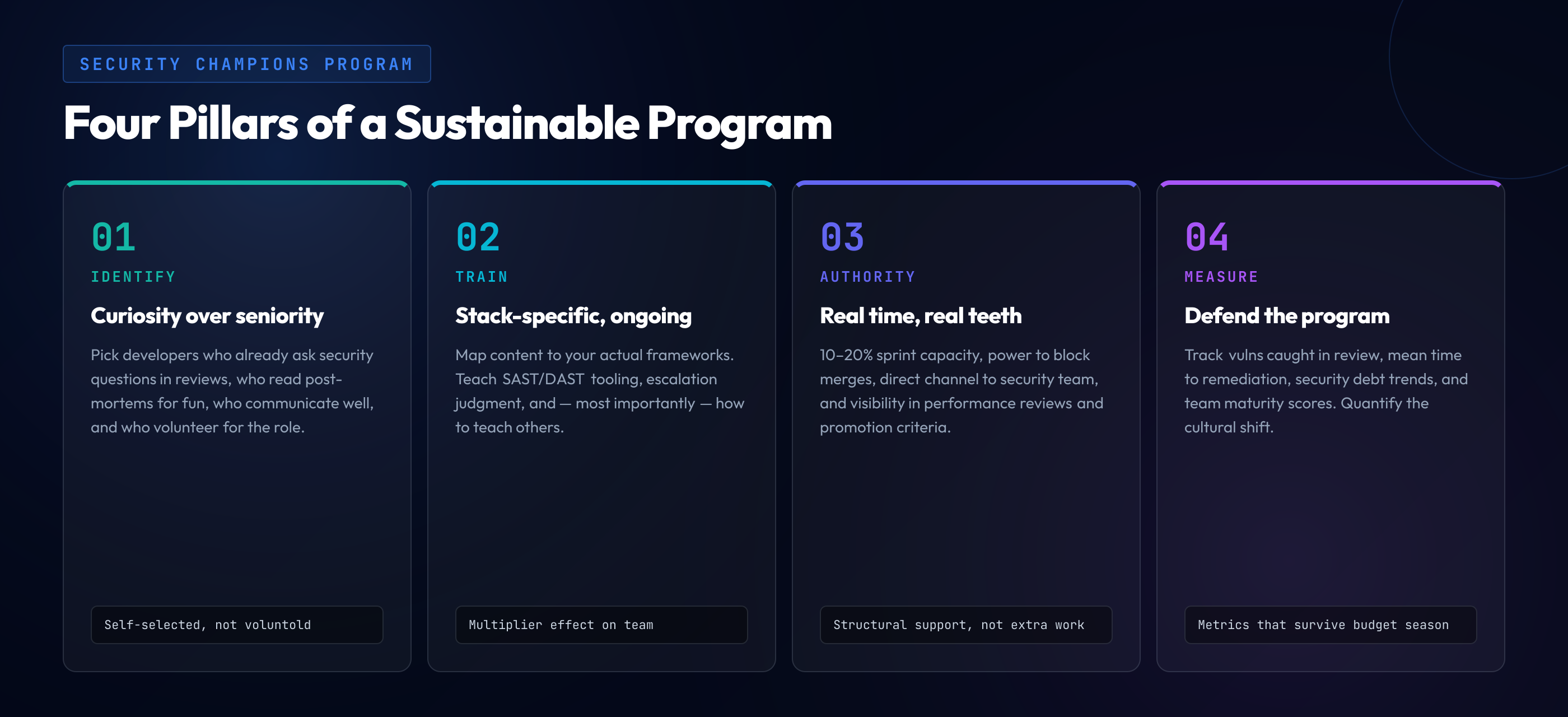
Instead, look for these traits:
- They already ask security questions in code reviews — Before any formal program exists, some developers naturally comment on missing input validation, question authentication flows, or flag hardcoded secrets. These people have the instinct. Build on it.
- They're curious about how things break — Not just how features work, but how they can fail or be abused. Developers who enjoy debugging, who read post-mortems for fun, who ask "what happens if someone sends a negative number here?" are natural fits.
- They communicate well — A champion's primary job is translating security concepts into language their team understands. Technical depth without communication skills means the knowledge stays locked in one person's head.
- They volunteer, not get voluntold — Champions who choose the role outperform those who are assigned to it. Make the program visible, explain the benefits, and let interested developers self-select.
"The best security champions aren't the most senior developers on the team. They're the most curious ones — the people who read the CVE database the way others read tech news."
Training Your Champions
Selecting the right people is only the beginning. Champions need structured training that goes beyond a one-time workshop or a link to the OWASP Top 10. The training should be ongoing, practical, and directly relevant to the technologies your teams use.
Common vulnerability patterns in your stack
Generic security training wastes everyone's time. If your teams write Node.js and React, your champions need to understand prototype pollution, server-side rendering injection risks, and JWT implementation pitfalls — not buffer overflows in C. Map training content to the actual languages, frameworks, and infrastructure your organization uses.
Security tooling proficiency
Champions should know how to configure and interpret results from your SAST and DAST tools, run dependency scans, and understand what the findings mean in context. A champion who can explain why a Semgrep rule flagged a particular pattern — and whether it's a true positive — is infinitely more useful than one who just forwards scanner output to the security team.
Escalation judgment
Not every security question requires the central security team's involvement. Champions need clear guidelines on what they can handle themselves (reviewing a PR for common injection patterns, ensuring HTTPS is enforced) versus what to escalate (a potential authentication bypass, a new third-party integration that handles PII, an architecture change that affects trust boundaries).
Teaching others
The highest-leverage skill a champion can develop is the ability to teach. When a champion explains why a particular code pattern is dangerous — not just that it needs to change — every developer on the team gets a little better at security. This multiplier effect is the entire point of the program. One champion who teaches ten developers creates ten people who catch issues independently.
Giving Champions Real Authority
This is where most programs fail. Organizations identify champions, train them, and then expect them to do security work on top of their full development workload with no structural support. Within months, the champions burn out, and the program dissolves.
For a champions program to survive beyond the initial enthusiasm, champions need real investment:
- Dedicated time — Allocate 10-20% of their sprint capacity for security activities. This means fewer feature tickets, and their managers need to agree to this explicitly. If security work is always the first thing cut when deadlines loom, the program is dead.
- Authority to block merges — Champions need the ability to request changes on pull requests for security reasons, with the same weight as a required reviewer. If their security feedback can be overridden by anyone, the role has no teeth.
- Direct channel to the security team — A dedicated Slack channel, regular syncs, or office hours with the security team. Champions are the bridge between security and development. That bridge needs to be open in both directions.
- Recognition and career growth — The champion role should be visible in performance reviews. It should count toward promotion criteria. If it's treated as "extra work" with no recognition, you're selecting for martyrs, and they won't last.
Measuring Success
A champions program without metrics is a program you can't defend when budget season arrives. Track these indicators to demonstrate impact and identify areas for improvement:
- Vulnerabilities caught in code review — How many security issues are champions finding before code reaches production? Track both count and severity. This is the most direct measure of the program's value.
- Mean time to remediation — When security issues are identified (by scanners, pen tests, or bug bounty), how quickly do teams with champions fix them compared to teams without? Faster fix times directly reduce risk exposure windows.
- Security debt trends — Is the backlog of known security issues growing or shrinking? Teams with effective champions should show a declining trend in open security findings over time.
- Team security maturity scores — Assess each team periodically on security practices: Do they threat model new features? Do PRs include security considerations? Are security tests part of CI/CD? Champions should measurably lift their team's baseline.
The most important metric, though, is one you can't easily quantify: the cultural shift. When developers start asking security questions without being prompted, when "did we think about the security implications?" becomes a natural part of design discussions, when security is no longer something that gets bolted on after the fact — that's when the champions program has truly succeeded. It's not about creating a few security experts. It's about making security a shared responsibility across every team that writes code.