If the only thing standing between your organization and a PCI DSS finding this year is an annual awareness video that every employee clicked through with the audio muted, 2026 is going to be uncomfortable. Requirement 12.6.1 — the security awareness training clause that applies to every person with access to the cardholder data environment — was rewritten in PCI DSS 4.0.1 to demand more than a once-a-year compliance ritual. This guide walks what the current text of 12.6.1 actually requires, who is in scope, how it differs from the developer training in 6.2.2, and exactly what a pci awareness training program has to look like to survive a QSA assessment in the current cycle.
Why Awareness Training Is Back in the Spotlight
For most of the 3.2.1 era, security awareness training was the quietest part of a Report on Compliance. An annual computer-based course covered phishing, passwords, and clean-desk rules; the QSA took the completion spreadsheet at face value; the conversation moved on. 4.0.1 changed the frame. The current text of 12.6.1 and its subrequirements (12.6.2 and 12.6.3) upgraded awareness from a box-check into an assessable program, with documented content expectations, role-aware customization, and explicit annual review. Organizations that treated the 2025 cycle as their first real exposure to the new bar are well-positioned. Organizations still running a 3.2.1-era awareness module are about to find out that the assessors have sharpened their questions and the evidence expectations are materially higher than they used to be.
The uncomfortable truth is that 12.6.1 is the easiest requirement to sleepwalk through — and therefore one of the most common sources of quiet findings in the 2026 cycle. Developer training (6.2.2) gets attention because it is newly enforced and technical. Awareness training gets overlooked because it has been there all along, and most compliance leaders assume the program they ran last year is the program they can run this year. It is not. The requirement text has moved, and a program that does not move with it will accumulate findings in areas compliance teams did not realize had changed.
What Requirement 12.6.1 Actually Says in 2026
The current text of Requirement 12.6.1 in PCI DSS 4.0.1 reads:
"A formal security awareness program is implemented to make all personnel aware of the entity's information security policy and procedures, and their role in protecting the cardholder data."
12.6.2 extends it to require that the awareness program be reviewed at least once every 12 months and updated as needed to address any new threats and vulnerabilities. 12.6.3 requires that personnel receive awareness training upon hire and at least once every 12 months, with additional training when their role changes in a way that affects their relationship to the cardholder data environment. Read together, the three subrequirements describe a program, not an annual event — and the word "program" is doing real work in the text. A QSA reading those clauses in 2026 is looking for evidence that the awareness content is current, role-aware, delivered to every in-scope person in a documented cadence, and that the content has been reviewed and updated since the last assessment.
"All personnel." Everyone. Not just developers. Not just engineers. Not just the security team. Every person in the organization whose access — physical or logical — touches the cardholder data environment or the systems that can connect to it. Administrative assistants with building access. Finance staff with payment data exposure. Help-desk staff with identity workflows. Contractors with badge access. Third-party support personnel with remote-access privileges. The scope of 12.6.1 is substantially broader than the scope of 6.2.2, and the evidence expectations scale accordingly.
"Information security policy and procedures." The training has to convey the content of the organization's actual policies — not a generic off-the-shelf curriculum that ignores the organization's specific controls. If your policy requires MFA on all remote access, the training should explain why. If your policy prohibits specific classes of external file sharing, the training should name them. A program whose content has no connection to the organization's own policies does not demonstrate that personnel were made aware of the entity's policies, which is the exact phrasing of the requirement.
"Their role in protecting the cardholder data." This is the role-relevance clause, and it is the clause most off-the-shelf programs struggle to satisfy credibly. A reception desk staff member's role in protecting cardholder data is different from a network engineer's role, which is different from a call center agent's. The training does not have to be a separate course for every role, but the content has to make the role-specific connection explicit — what this particular person sees, touches, or controls that matters for the cardholder environment, and what they are expected to do about it.
Who Is In Scope for PCI Awareness Training
Scope is the first place 12.6.1 programs fail quietly. Compliance teams often build their training rosters from HR systems or access management exports without cross-referencing them against the full list of people whose activity can affect the cardholder data environment. The assessor's scope question is broader than "who has a login". It is "who can, by any combination of access and action, influence the confidentiality, integrity, or availability of cardholder data or the systems that process it". That framing catches several categories that HR-driven rosters miss.
Full-time employees with CDE-adjacent access. The obvious category. Engineering, operations, support, finance, legal, HR, marketing — any employee whose workstation can route packets to the cardholder environment or whose credentials provide access to systems that can.
Contractors and temporary staff. Anyone with a badge, a VPN certificate, or system credentials, regardless of employment classification. Contract length does not matter — a two-week consultant with a temporary admin account is in scope the moment the account is provisioned. Awareness content has to be part of the onboarding workflow for contract roles, not a deferred requirement that gets addressed at the annual batch run.
Third-party support and managed-service personnel. Vendors who can log into your environment for support or maintenance. 12.8.x requires written agreements that address these vendors' PCI responsibilities; 12.6.1's awareness requirement extends to the vendor's personnel who actually use the access. The practical pattern is either the vendor runs its own 12.6.1-compliant program and provides evidence, or your organization provides a tailored module these vendors complete before access is granted.
Facilities, janitorial, and physical-access personnel. Often missed. A janitor who has after-hours badge access to a server room is in the scope of 12.6.1 because they have physical access to a system in the CDE. The content can be simplified — they do not need the same modules as a network engineer — but they do need awareness of the specific procedures that apply to them (badge hygiene, tailgating prevention, who to contact for anomalies).
Executive leadership and board observers. Leadership is not exempt. Executives frequently have broader access than their direct reports, and their role in the culture of security matters to the overall program. 12.6.1 applies to them on the same rolling cadence as everyone else, and many QSAs pay specific attention to whether the C-suite completed the training alongside the rank-and-file.
If your current roster does not reflect all five of these categories, the scope is almost certainly under-counted. The first deliverable of any 12.6.1 program refresh is a roster reconciliation exercise — HR data, access management exports, vendor agreements, facilities contracts — producing a single consolidated list of every person to whom the requirement applies.
What Content 12.6.1 Demands
The requirement text is high-level. The PCI Council's supplementary guidance documents and the patterns validated in public 2025 assessments fill in the detail. A defensible pci dss awareness training program for the 2026 cycle covers, at minimum, seven content areas — each mapped to a specific risk the awareness program is supposed to reduce.
1. The organization's information security policy, framed for the audience. Not a copy of the policy document, but an accessible summary with the clauses that affect day-to-day behavior explained in terms the audience understands. Passwords, acceptable use, remote work, data handling, incident reporting.
2. Phishing and social engineering awareness. The attack class responsible for a significant fraction of recorded CDE compromises in the 2024-2025 window. Content should include recognition patterns, reporting procedures, and explicit examples current enough to reflect 2026-era techniques (QR-code phishing, AI-voice impersonation, Teams and Slack-based pretexting).
3. Password and credential hygiene. MFA configuration, password manager usage, shared-credential prohibitions, session handling. The content has to align with the organization's actual authentication controls — training people on practices they cannot enforce in the production environment is a credibility problem the QSA will probe.
4. Acceptable use of corporate assets. Laptops, mobile devices, cloud accounts, email, messaging platforms. What can be connected, what can be installed, what can be shared. This is the section where the "information security policy and procedures" clause lives most concretely.
5. Physical security and facilities. Badge handling, tailgating, clean desk, device lockdown, visitor escort procedures, handling of printed materials containing cardholder data. For personnel with physical access to CDE facilities, this section expands; for remote-only personnel, it may be abbreviated to home-office and device-theft coverage.
6. Incident recognition and reporting. What a security incident looks like at the level this person would encounter it, and the exact escalation path to report it. Named channel, named team, named timeline. Generic "contact security" without a specific channel is a weak artifact.
7. Role-specific content where applicable. The additional modules that address a given role's specific exposure to cardholder data. A call center agent gets PAN-handling procedures and session recording notes. A finance manager gets chargeback-fraud awareness. An IT administrator gets privileged-access hygiene. This is the section that ties 12.6.1 to the "role in protecting cardholder data" clause in the requirement text.
The training does not have to be seven separate modules — some organizations deliver the first six as a single core course and handle role-specific content through targeted supplementary modules. The structure matters less than the coverage. A QSA reading the curriculum should be able to point to specific content for each of the seven areas and, for role-specific modules, see the assignment logic that connects roles to additional content.
How 12.6.1 Differs From 6.2.2 — And Why It Matters
A surprising number of organizations heading into 2026 have conflated developer training (6.2.2) and general awareness (12.6.1) into a single program — usually because a single vendor offered a bundled product that appeared to cover both. The requirements are structurally different, the assessors read them separately, and a program that blurs the line tends to fail both requirements at once. The distinction is worth drawing explicitly.
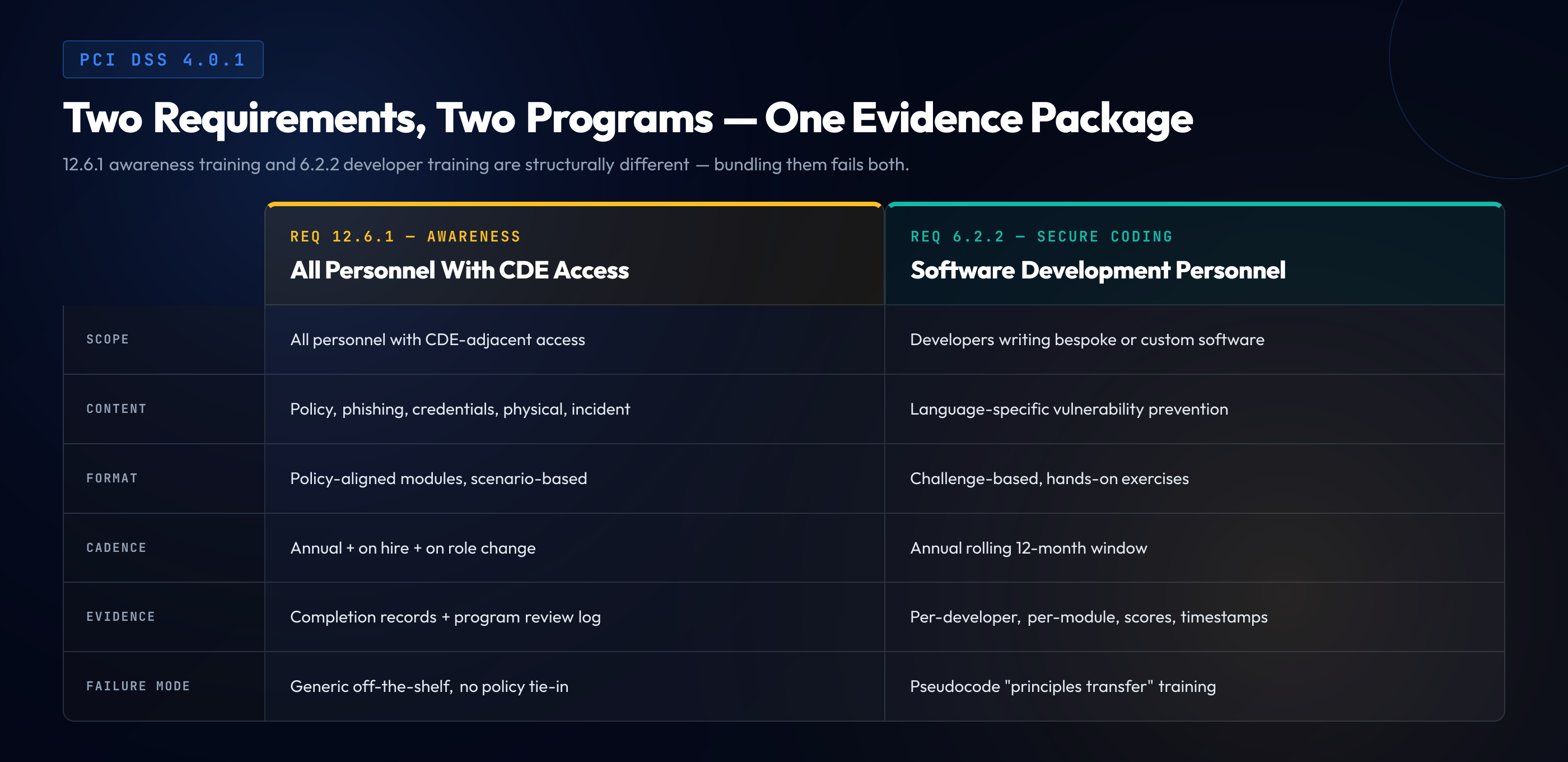
6.2.2 applies to "software development personnel working on bespoke and custom software". The content has to be language-specific, role-mapped to a developer's stack, and hands-on. The details of what qualifies are covered in our deeper guide to what PCI DSS 4.0.1 Requirement 6.2.2 actually demands, including the evidence artifacts a QSA will request. 12.6.1 applies to "all personnel" with a connection to the cardholder data environment. The content covers policy, behavior, and awareness — not coding technique. A developer needs both: a 12.6.1-compliant awareness course covering phishing, credential hygiene, and policy, plus a 6.2.2-compliant secure coding course covering injection defenses in their actual languages. A non-developer needs only 12.6.1.
| Dimension | 12.6.1 — Awareness | 6.2.2 — Developer |
|---|---|---|
| Scope | All personnel with CDE-adjacent access | Developers writing bespoke or custom software |
| Core content | Policy, phishing, credentials, physical, incident | Language-specific vulnerability prevention |
| Format | Policy-aligned modules, scenario-based | Challenge-based, hands-on exercises |
| Cadence | Annual + on hire + on role change | Annual rolling 12-month window |
| Evidence | Completion records + program review log | Per-developer, per-module, scores, timestamps |
| Biggest failure mode | Generic off-the-shelf content, no policy tie-in | Pseudocode "principles transfer" training |
A vendor or program that markets itself as "covering both 6.2.2 and 12.6.1" is not inherently wrong — but the architecture has to keep the two separate in content, assignment, and evidence. If the same twenty-minute video is handed to both the reception desk and the backend engineer, neither requirement is satisfied. If the developer sees role-mapped language-specific modules and the organization-wide awareness curriculum, both are satisfied, and the evidence package can separate them cleanly for the QSA.
Frequency, Format, and Documentation
12.6.3 specifies the cadence explicitly: upon hire, at least annually, and upon any role change that affects CDE exposure. In practice, the annual cadence operates as a rolling 12-month window per person, the same way 6.2.2 does. A batch campaign in January satisfies the letter of the requirement for people employed on 1 January, but it fails for anyone hired in March — who would otherwise go fifteen months between training events. The right instrumentation is an LMS or HR integration that tracks each person's most recent training date and triggers reminders at sixty and thirty days before the deadline.
Format flexibility. The requirement does not prescribe format. Computer-based training, live instructor-led sessions, scenario workshops, simulated phishing exercises, video modules, and reading-plus-quiz formats all qualify on paper. What matters is that the content is covered, that each person has completed it, and that the completion is evidenced. The quality difference between formats shows up in the behavior outcomes — a bored employee clicking through a video is evidence of completion but weak evidence of awareness, and programs that combine multiple formats (training modules plus simulated phishing plus incident-report drills) tend to produce the culture signal the Council envisioned when it rewrote the clause.
Program review cadence (12.6.2). The awareness program itself must be reviewed at least annually and updated to reflect new threats. This is the single most common compliance gap in 2026 assessments. Programs that were written in 2021 and never revisited do not reflect the current threat landscape — they miss QR-code phishing, MFA-fatigue attacks, AI-voice impersonation, business email compromise patterns that emerged through 2024, and the new generation of Slack and Teams-based social engineering. The annual review is an evidence artifact: a dated document showing what was reviewed, what was changed, and why.
Documentation depth. Per-person completion records with timestamps, the curriculum document itself, the annual review log, and (if simulated phishing or similar exercises are used) the exercise records. A QSA should be able to walk into the evidence review and pull the training record for any named person without the compliance team having to reconstruct it from multiple systems. Programs whose evidence lives across HR, a standalone LMS, and a shared drive of completion certificates tend to fall apart the moment the assessor asks a specific question about a specific person.
Red Flags in Off-the-Shelf Awareness Training
The awareness training market is mature and crowded. Most vendors have a product; not all products are designed for the 4.0.1 bar. The failure patterns worth watching for during a vendor evaluation are consistent.
Content that never mentions the customer's policies. A generic course that does not reference the organization's actual acceptable use, MFA, or remote-access policies cannot demonstrate awareness of "the entity's" policies, which is the exact phrasing of 12.6.1. The fix is either customization — the vendor edits modules to cite the customer's policy names — or a complementary in-house module that covers the organization-specific content and pairs with the vendor's generic foundation.
A single curriculum with no role awareness. Everyone gets the same course. Reception, engineering, finance, and executive leadership all sit through identical content. The content is usually generic enough that none of them find it relevant, and the program cannot demonstrate the role-specific connection the requirement implies.
Static content with no changelog. The vendor cannot show when the course was last updated or what was added in response to new threat patterns. A course shipped in 2022 and still being sold unchanged is not a course that reflects 2026 threats. The annual program review required by 12.6.2 becomes an exercise in documenting that nothing has changed — which is not a credible position for any awareness program in the current threat environment.
Completion tracking without assessment. The LMS records that the employee clicked through the module but not whether they learned anything. As with developer training, a program that includes any kind of assessment — a short quiz, a simulated phishing response, a scenario walkthrough — is materially stronger evidence than one that only records attendance.
No coverage of contractor and vendor personnel. The vendor product is priced and configured for full-time employees, and extending it to contractors requires manual workarounds that rarely get executed consistently. If 20% of your CDE-adjacent workforce is contract, a full-time-only product is a structural gap in the program.
Marketing that bundles 6.2.2 coverage into the same product. "One program for both awareness and developer training" is a reassuring pitch but a structurally weak product. The content, scope, assignment logic, and evidence expectations for the two requirements are different enough that trying to unify them usually compromises one or both. A vendor that acknowledges the distinction and offers differentiated modules is stronger than one that claims a single product solves both.
Building a Program That Passes Your QSA Assessment
The end-to-end checklist for a 12.6.1-compliant program in 2026 is not long, but every item corresponds to an evidence artifact the assessor will ask for. A program that has all of these in place is in strong position for the current cycle.
- Scoped personnel roster. Consolidated list of all employees, contractors, vendors, and facilities personnel with any form of CDE-adjacent access. Reconciled across HR, access management, and vendor records.
- Curriculum document. Written description of the awareness program, the modules it contains, the content each module covers, and the specific 12.6.1 / 12.6.2 / 12.6.3 clauses each addresses.
- Policy-aligned content. Training modules reference the organization's own information security, acceptable use, remote access, MFA, and incident-response policies by name.
- Role-relevance mapping. Documentation of which modules apply to which roles, with a clear path for role-specific supplementary content where CDE exposure warrants it.
- Annual cadence tracking. Per-person completion records with timestamps, automated reminders at 60 and 30 days before each person's deadline, and documented handling for personnel who miss the window.
- Onboarding integration. Awareness training completion is a hard gate in the new-hire workflow before CDE access is provisioned — for employees and contractors alike.
- Role-change trigger. Documented process for identifying role changes that require additional awareness training, with retraining completed before new access is granted.
- Annual program review log. Dated record of each annual review: what was assessed, what was updated, what new threat content was added, what was retired. At least one entry per calendar year.
- Assessment or response element. Each module includes a short assessment, scenario response, or simulated exercise; records include per-person scores or outcomes.
- Simulated phishing or equivalent reinforcement. Ongoing reinforcement activity beyond the annual module — simulated phishing, tabletop drills, targeted refresher microlearning — with records.
- Vendor and contractor coverage. Evidence that contractor and vendor personnel have completed the training, either through the organization's LMS or through the vendor's own 12.6.1-compliant program with documented verification.
- Incident reporting content. Specific escalation channel, team, and timeline referenced in the training, with evidence that the channel is live and monitored.
- Current threat coverage. Content that reflects the current year's threat landscape — QR-code phishing, MFA fatigue, AI-voice and AI-video impersonation, business email compromise patterns, messaging-platform pretexting.
- Evidence-retrieval capability. On request, the compliance team can produce any person's training record, the curriculum document, and the program review log within the same day.
A program that has these fourteen items in place is positioned well beyond the minimum — it is the kind of program that produces short, uncontested 12.6 conversations with the assessor. Programs that have seven or eight items are the ones that generate lengthy evidence requests and remediation timelines.
Onboarding, Contractors, and Role Changes
The three specific lifecycle events in 12.6.3 — hire, annual, role change — each create instrumentation requirements that many programs underbuild.
Onboarding. The hard version of 12.6.3's hire clause is: no person receives CDE-adjacent access before awareness training is complete. The soft version — common in practice, uncomfortable in assessments — grants access first and expects the training within the first thirty days. The soft version creates a window where a person has access without evidence of awareness, which is exactly the gap 12.6.3 was written to close. The instrumentation is a hard gate in the provisioning workflow: access management consumes an LMS completion signal, and the absence of the signal blocks account creation. Several identity platforms support this natively; most organizations that claim they cannot implement it have not actually tried.
Contractors. The common failure is a contractor-onboarding workflow that assumes the vendor has "their own compliance", which is rarely true in the specific form 12.6.1 requires. The practical pattern is a short, organization-specific module the contractor completes alongside their access provisioning. Fifteen minutes, covers the organization's policies, incident reporting channel, and the specific obligations the contract creates. Treated as a condition of access, not a nice-to-have. Vendor relationships that cannot accommodate this pattern are flagged during procurement, not during audit.
Role changes. The instrumentation gap that catches most programs. An engineer promoted to a role with broader CDE access keeps their old training record. From the LMS's perspective, nothing changed. From 12.6.3's perspective, a role change with expanded CDE exposure triggers additional training. The fix is a process that runs whenever access is re-provisioned or expanded: HR signals the change, security determines whether additional training applies, the LMS assigns any supplementary modules before the new access is live. The common operational pattern is a weekly review of access changes in a ticketing system, but any cadence that catches role changes before the next assessment is acceptable.
The Evidence Package for Your Report on Compliance
When a QSA works 12.6 in the assessment, they are looking for a specific bundle of artifacts. The bundle is smaller than the 6.2.2 evidence package, but it has to be complete and current.
- Awareness program curriculum document. Written description of the program, modules, coverage, and the subrequirements each module addresses.
- Personnel roster. Every person in scope, classified by role and by access category.
- Per-person completion records. Date completed, module(s) completed, assessment results where applicable.
- Currency report. A report showing each person's most recent training date and their status against the 12-month rolling window.
- Annual review log. Dated record of each annual program review, with what was changed and why.
- Onboarding evidence. For new hires and new contractors since the last assessment, records showing training completion before access provisioning.
- Role-change evidence. For personnel whose roles changed with expanded CDE access, records showing supplementary training completion.
- Reinforcement activity records. Simulated phishing runs, tabletop drills, or other reinforcement activities, with participation records.
Producing these eight artifacts cleanly — on request, without scrambling — is the single highest-value operational capability a compliance team can build around 12.6.1. The effort to build the capability once pays back across every subsequent assessment, every procurement due-diligence exchange, and every SOC 2 or ISO review. The same artifacts support adjacent frameworks, because the requirements are similar enough that the evidence transfers.
What Awareness Training Does Not Have to Be
The final thing worth saying about 12.6.1 is what a compliant program is not required to do — because the compensating overbuild is nearly as common as the underbuild. 12.6.1 does not require a content library with hundreds of modules. It does not require fancy production values, simulation games, or gamification. It does not require hours-long courses; a well-structured awareness curriculum can be delivered in sixty to ninety minutes of core content plus the reinforcement activity through the year. It does not require a premium LMS — an HR system, a simple LMS, or even a well-documented internal workflow can satisfy the evidence requirements if the content and tracking are sound.
What it requires is exactly what the text says: a formal program, addressing the policy and role-specific content, delivered to all personnel on the right cadence, reviewed annually, and evidenced. A program built around that literal reading — without trying to turn awareness training into a high-production spectacle — passes assessment consistently and leaves the compliance team with operational bandwidth to address the harder requirements elsewhere in the standard.
Awareness for 12.6.1. Secure Coding for 6.2.2. One Evidence Package.
SecureCodingHub's PCI DSS training program covers both the awareness training required by 12.6.1 and the developer-specific secure coding training required by 6.2.2 — delivered in separate, role-mapped curricula so the evidence your QSA reviews is cleanly structured against each requirement. If your 2026 assessment cycle is approaching, we are happy to walk your team through how our program maps to your organization's scope.
See Our PCI DSS ProgramClosing: The 2026 Cycle Rewards Programs That Move With the Standard
12.6.1 is not the headline requirement in PCI DSS 4.0.1. It does not generate the same panic as 6.2.2, it does not come with the same developer-specific evidence complexity, and it was not the subject of dedicated guidance reissues through 2025. That is precisely why it is the requirement most likely to produce quiet findings in 2026 assessments. The organizations that sailed through the 3.2.1 era on a generic annual awareness video are the ones most exposed to the current bar. The organizations that treated 2025 as the year to refresh their awareness program against the updated 12.6.1 / 12.6.2 / 12.6.3 text are well-positioned.
Awareness training, like developer training, is not a paperwork exercise in the 4.0.1 era. It is the Council formalizing a cultural expectation — that every person with a connection to the cardholder environment understands the policies that govern their role and the actions those policies expect them to take. The programs that deliver that cultural outcome also pass assessments cleanly. The programs that cannot deliver it end up passing assessments by accident in easier years and failing them in harder ones. The 2026 cycle is a harder year. Building the program to the literal text of the requirement is the cheapest way to stop worrying about which kind of year it turns out to be.
For the financial side of an assessment that goes the wrong way — what card brand assessments, monthly fines, forensic investigation, and breach liability actually add up to — see the companion guide on PCI DSS non-compliance fines and penalties.