The question "what is the pci dss non compliance fee" produces a single number on the first page of most search results, and the number is wrong. There is no single fee. There is a layered set of charges — monthly assessments from the acquiring bank, card brand assessments triggered by a breach, mandatory forensic investigation, per-card liability, increased processing rates, brand damage, and the eventual loss of merchant agreements — that combine into a real total which routinely exceeds a hundred times the headline figure. This guide walks the actual cost surface of PCI non-compliance in 2026: what each layer charges, where the numbers come from, why the most-cited estimates skip the largest costs, and what the comparison looks like against the cost of running a compliant program in the first place.
Why "PCI Non-Compliance Cost" Is a Misleading Single Number
The questions developers and small business owners actually search — pci non-compliance fee charges who pays, pci non compliance fee, pci fee, pci violation consequences, pci penalties — all have the same problem: there is no single answer. The pci non-compliance fee charges are split across the acquiring bank (who pays the monthly non-compliance fee, which the bank then often passes through to the merchant), the card brands (who assess separately), the PCI Forensic Investigator (whose costs the merchant covers directly), and the downstream remediation work the merchant funds out of pocket. Understanding who pays which fee is essential to understanding the actual cost exposure — and to making the case for the PCI risk assessment work that prevents the cost from materializing in the first place.
Most articles answering "what is the pci non compliance cost" give a single dollar range — usually "$5,000 to $100,000 per month" — and stop there. The number is not made up. It corresponds to a real category of charges (monthly fines from the acquiring bank when a merchant is out of compliance) and is roughly accurate for that specific category. The problem is that the monthly fine is the smallest layer of the actual cost surface. Treating it as the answer to the cost question is like answering "what does a car cost" with "the gas you put in it last week".
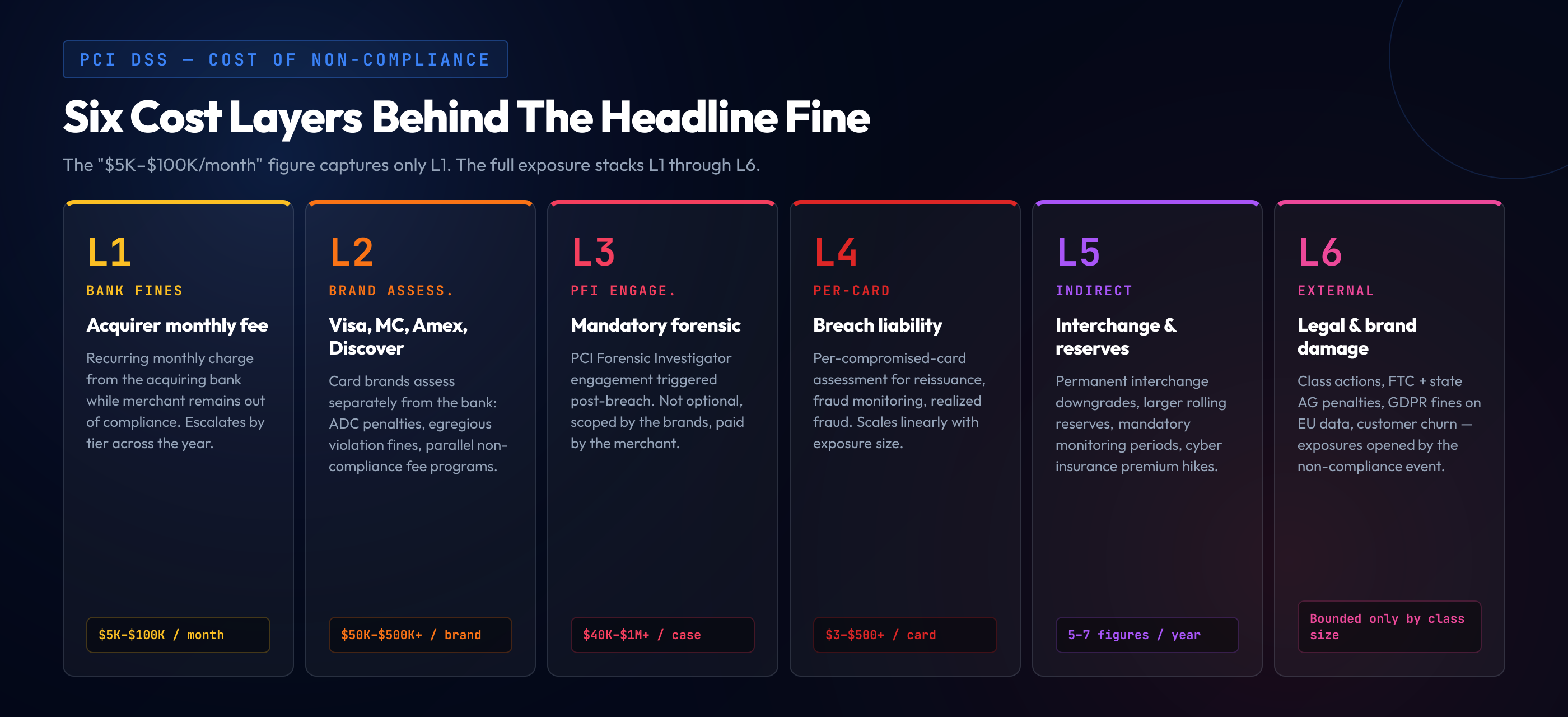
A PCI non-compliance event in 2026 generates costs across at least seven independent layers. The acquiring bank charges a monthly non-compliance fee while the merchant remains out of compliance. The card brands — Visa, Mastercard, American Express, Discover — charge separate assessments, and those assessments escalate sharply if non-compliance is discovered through a breach rather than through routine reporting. A breach triggers a mandatory PCI Forensic Investigator engagement, which is not optional and not cheap. The card brands assess per-compromised-card fees that scale linearly with the size of the data exposure. Card brand operating regulations allow for downgraded interchange tiers — a permanent increase in processing cost. Mandatory monitoring periods and quarterly reporting obligations extend for years after the event. And the brand-damage and customer-trust costs, while harder to quantify, are real enough that most public breach disclosures include them in their 8-K filings.
Reading any of these layers in isolation produces a misleading answer. Reading all of them together — which is what a CFO doing real risk analysis ends up doing — produces a number that makes the cost of compliance look like a rounding error. This guide goes through each layer in order of how often it is missed, starting with the layer most articles do cover and ending with the layers most do not.
The Monthly Fines: $5K to $100K From the Acquiring Bank
The most-cited pci dss non compliance charge is the recurring monthly fee an acquiring bank charges a merchant who is out of compliance. The fee is not specified in the PCI DSS standard itself — it is a contractual term in the merchant agreement between the bank and the merchant. The bank, in turn, is contractually obligated to the card brands to ensure its merchants are PCI-compliant, and the brands assess the bank if the merchants are not. The bank passes that exposure through to the merchant via the monthly fine.
The exact schedule varies by bank and merchant level, but the broad pattern is consistent across the industry:
- Months 1-3 of non-compliance: $5,000 to $10,000 per month. The introductory tier — the bank's signal that compliance has lapsed and remediation is expected.
- Months 4-6: $25,000 to $50,000 per month. The escalation tier — the bank is now incurring real exposure to the card brands and is passing more of the cost through.
- Months 7+: $50,000 to $100,000 per month. The terminal tier — sustained non-compliance at this point typically also triggers a notice of intent to terminate the merchant agreement.
For a small merchant, the lower end of this schedule is meaningful but survivable. For a Level 1 merchant processing more than six million Visa transactions per year, the upper end of the schedule is the floor — actual fines on Level 1 merchants who have lapsed without breach exposure routinely run at $25,000 monthly minimum, with the bank's specific schedule documented in the merchant agreement.
The most important thing to understand about the monthly fine layer is that it accumulates. A merchant who is out of compliance for nine months without a breach has paid somewhere between $200,000 and $700,000 in monthly fines alone, before any breach-driven costs are considered. Compliance teams that defer the annual AOC submission for "just one more quarter" while a project finishes are usually unaware of the schedule their merchant agreement specifies, and the first invoice they receive from the bank tends to clarify the math.
Card Brand Assessments: Visa, Mastercard, American Express, Discover
The next layer up — and the layer most "cost of pci non compliance" articles entirely skip — is the assessments levied directly by the card brands. These are separate from the acquiring bank's monthly fee, separate from the breach-related costs, and separate from any forensic investigation. They are the card brand's own enforcement mechanism, applied through the acquiring bank but originating from the brand.
Account Data Compromise (ADC) penalties. When card data is compromised — even before a full breach is confirmed — the brands assess ADC fees on the bank, which are passed through to the merchant. Visa and Mastercard's ADC programs operate on tiered schedules that depend on the number of accounts at risk, the merchant's level, and whether the merchant was PCI-compliant at the time of the incident. ADC fines for a non-compliant merchant typically start at $50,000 and can run to $500,000 per incident on the Visa side alone, with parallel assessments from Mastercard.
Egregious Violation Fines. Visa's most severe category, applied when a merchant has materially violated the operating rules — storing prohibited data (full track, CVV2, PIN block), failing to remediate after a breach, or operating without a valid AOC in a high-risk segment. Egregious violation fines start in the low hundreds of thousands and have no upper bound published; the brands have used them as the lever to recover meaningful fractions of breach response costs from merchants whose negligence was material to the breach.
Non-Compliance Fee Programs. Each major brand operates a non-compliance fee program parallel to the acquiring bank's. Mastercard's Merchant Compliance Program and Visa's PCI DSS Compliance Validation Program each include their own fine schedules for merchants who are persistently non-compliant. These run on top of the acquiring bank's monthly fee — the merchant pays both.
American Express and Discover. Both brands operate their own compliance enforcement separately from the Visa/Mastercard duopoly. American Express's Data Security Operating Policy includes its own schedule of fines, and Discover's Information Security & Compliance program operates on similar lines. A merchant who accepts all four brands and is out of compliance is potentially exposed to four parallel fine schedules. Most merchants are not consciously tracking all four because the acquiring bank handles the consolidated billing — until a breach makes the per-brand exposure visible.
The aggregate pci compliance fines picture across the four brands, before any breach-specific costs, can run to several hundred thousand dollars for an extended non-compliance period. After a breach, the assessments are an order of magnitude higher.
Forensic Investigation Cost (PFI Engagement)
If a breach occurs and card data is suspected to have been compromised, the card brands require a PCI Forensic Investigator (PFI) engagement. This is not optional. The PFI is selected from the PCI Council's qualified register, the engagement scope is defined by the brands, and the merchant pays. The forensic investigation is a discrete cost layer on top of everything else discussed so far — and it is the cost layer where the headline number is least predictable.
Typical PFI cost ranges. A simple, well-scoped PFI engagement on a small merchant with limited environments and clear evidence runs $40,000 to $75,000. A mid-sized engagement with multiple in-scope environments, mixed cloud and on-prem infrastructure, and significant log analysis runs $75,000 to $200,000. A complex engagement on a Level 1 merchant with multi-tenant environments, ambiguous initial scope, and contentious findings can run substantially higher — six-figure ranges trending into seven figures for the largest engagements are not unusual.
What drives PFI cost. The investigation has to determine the entry vector, the dwell time, the data exfiltrated, the systems compromised, the controls that failed, and the timeline of the event. The more environments in scope, the more complex the network architecture, the more cloud services involved, the longer the dwell time, the more interview hours required — each of these multiplies the engagement length. A merchant with strong logging, clear network segmentation, and well-documented controls produces a faster, cheaper PFI report. A merchant whose pre-breach posture was disorganized produces an investigation that has to reconstruct evidence the merchant cannot itself produce, and the cost reflects that.
What the PFI report does to subsequent costs. The PFI report is the input the card brands use to calibrate their per-card assessments and the egregious violation fines discussed above. A report that finds the merchant was substantially compliant and the breach exploited a novel vector results in lower brand-side assessments. A report that finds the merchant was storing prohibited data, ignoring scan failures, or operating without controls that should have been in place results in materially higher brand-side assessments. The PFI report is, in practical terms, the document that determines whether the breach costs the merchant millions or tens of millions.
The Real Killer: Breach Liability and Per-Card Fines
The largest cost layer — by an order of magnitude over everything discussed so far — is the per-card assessment imposed by the brands when card data is confirmed compromised. This is the layer that turns a six-figure incident into a nine-figure incident, and it is the layer that almost no public "pci dss fines and penalties" estimate captures correctly.
How the per-card math works. The card brands assess the issuing banks for the cost of reissuing compromised cards, the cost of fraud monitoring, the cost of fraudulent transactions that occur on the compromised cards before they are deactivated, and the operational cost of handling the event. The brands then pass those costs through to the breached merchant, as a multiplier per compromised card. The per-card assessment varies by brand, by card type, by region, and by the negotiation that follows the PFI report — but the practical range for a non-compliant merchant whose breach the PFI found preventable is roughly:
- Low end: $3 to $10 per compromised card. Reissuance cost, basic fraud monitoring, no significant fraud realized. Applies when the PFI report is favorable to the merchant.
- Mid range: $20 to $50 per compromised card. Reissuance plus enhanced fraud monitoring plus realized fraud losses on a fraction of the compromised set.
- High end: $100 to $500+ per compromised card. Significant realized fraud, premium card categories (corporate, high-limit personal), egregious violation findings adding multiplier exposure.
Why the aggregates get large fast. A breach exposing 100,000 cards at $20 per card is a $2M assessment. A breach exposing 1,000,000 cards at $50 per card is a $50M assessment. A breach exposing 10,000,000 cards at $100 per card — the kind of number publicly disclosed in the largest historical incidents — is a $1B assessment, and that is just the per-card layer, separate from the egregious-violation fines, the PFI cost, the forensic remediation, the legal exposure, and the regulatory penalties from data-protection authorities (which are themselves a separate cost layer in the GDPR and US-state-AG framework).
The negotiation reality. The per-card assessment is not literally invoiced at the rate-card level — there is a negotiation between the breached merchant, the acquiring bank, and the brands, mediated by the PFI report. The negotiation can compress the headline number, sometimes substantially. But the negotiation starts from the rate-card position, and a merchant whose pre-breach posture was weak negotiates from a much weaker starting point than a merchant whose only failure was a novel exploit on otherwise-strong controls. The single largest variable in the size of the eventual settlement is the merchant's pre-breach compliance posture as documented by the PFI.
Indirect Costs Most Estimates Skip
Beyond the direct fines and assessments, a non-compliance event — and especially a breach-triggered event — generates a long tail of indirect costs that compound over years. These are the costs that show up in the 8-K filings of public companies after a breach disclosure but rarely appear in the front-page pci non compliance penalties guides.
Increased interchange rates. When a merchant is downgraded by the brands following non-compliance or a breach, the interchange tier they qualify for shifts. The downgrade is not always reversible on a short timeline. The merchant pays a higher interchange rate on every transaction for the duration of the downgrade — typically a year minimum, often longer. For a merchant processing $100M in card volume annually at a 25 basis point downgrade, the annual cost is $250,000. Sustained downgrade tiers across multiple years compound into seven-figure operating cost increases that never appear under the heading "non-compliance fines".
Mandatory monitoring and reporting periods. Following a breach or material non-compliance event, the brands typically impose extended monitoring obligations — quarterly enhanced reporting, additional ASV scan frequency, mandatory third-party assessment beyond the normal QSA cycle, sometimes for two to five years. The cost of producing this enhanced reporting falls on the merchant, on top of the normal compliance program cost.
Loss of merchant agreement. The most severe indirect cost is the loss of the merchant agreement itself. A bank that has decided a merchant is uneconomical to keep — typically after multiple cycles of escalation, sustained non-compliance, or a particularly damaging breach — exercises the termination clause in the merchant agreement. The merchant has to find a new acquiring bank, in a market where their compliance history is now visible to every prospective partner. The replacement bank, if one accepts the merchant at all, prices the relationship for the elevated risk: higher reserves, higher interchange, stricter compliance covenants. The cost of the replacement relationship over its life is often greater than any of the direct fines.
Increased reserves. Banks holding merchant accounts for higher-risk merchants typically require larger rolling reserves — funds held against potential chargebacks. A merchant moved from a 0% rolling reserve to a 5% or 10% reserve has a meaningful chunk of working capital trapped, with corresponding cost-of-capital impact.
Cyber insurance premium increases. Cyber insurance underwriters factor PCI compliance posture and breach history heavily into premium calculations. A merchant whose compliance lapsed or whose breach was traced to remediable weaknesses faces materially higher premiums on renewal — often double or triple the prior period's rate, with reduced coverage limits and increased self-insured retentions. Across a five-year renewal cycle, the cumulative premium increase is substantial.
Legal, regulatory, and class-action exposure. Beyond the card-brand layer entirely, a breach involving payment card data triggers parallel exposure to the FTC, state attorneys general, and class-action plaintiffs' bar. GDPR fines apply when EU residents' card data is involved. State-level data breach notification laws each carry their own per-record civil penalty schedules. Class-action settlements following major card breaches have run from low-eight-figures to nine-figures depending on the class size. None of this exposure is part of the PCI fine schedule — but a non-compliance event is the predicate that opens it up.
Brand and trust damage. The hardest to quantify and frequently the largest. Customers who learn their card data was exposed at a specific merchant change their purchasing behavior; some never return. The reputational impact compounds with social media coverage, news cycles, and the general loss of confidence in the brand's care for customer data. Public companies typically reflect the impact in revenue guidance for several quarters after a major incident.
The Most Common Path to Non-Compliance
For all the catastrophic numbers, the path to non-compliance is rarely dramatic. It is a slow drift — usually a combination of four or five quiet operational gaps that, individually, look survivable and, in combination, fail an assessment or surface a vulnerability that turns into a breach.
Silent expiration of the AOC. The Attestation of Compliance is annual. Organizations whose previous QSA relationship ended without a clear renewal path, whose internal compliance owner left without handover, or whose business reorganization moved compliance ownership without notice, end up with an AOC that quietly expires. The acquiring bank flags it during the next reporting cycle. The merchant is now non-compliant and the monthly fine schedule starts.
Scope creep without controls. A new product line, a new payment integration, a new cloud account, or a new third-party service provider gets added to the cardholder data environment without the corresponding controls, scans, training, or attestation work. The next assessment finds the new scope un-attested, and the merchant is non-compliant for the new scope even if the rest of the program is solid.
Missing 11.3 scans. A quarter passes without an ASV scan. Or a significant change happens without the rescan. Or the internal scans were unauthenticated, missing entire categories of findings. The deeper mechanics are covered in our guide to PCI DSS vulnerability scanning under Requirement 11.3, and missed scans are one of the most common single-point causes of a finding that turns into non-compliance.
Training gaps under 6.2.2 and 12.6.1. The developer secure-coding training required by 6.2.2 was not completed for the new hires this year, or the awareness training required by 12.6.1 across all CDE-adjacent personnel was not refreshed against the current threat content. The QSA finds the gap, the merchant cannot produce evidence, the AOC is not granted.
Documentation drift. The risk-ranking policy, the significant-change definition, the scope document, the network diagram — each was current at some point, none is current now. The QSA reads the documents, walks the environment, finds the divergence, and writes the finding. None of these are individually breach-causing, but together they describe a program that cannot satisfy the 4.0.1 evidence bar.
The pattern these failures share is that none of them are visible until the assessment, the bank inquiry, or the breach forces them to the surface. By that point, the cost of remediation is materially higher than the cost of having maintained the program continuously.
What 6.2.2 Secure Coding Training Costs vs What Skipping It Costs
The most concrete way to read the cost-of-non-compliance picture is against the cost of the specific training, scanning, and program elements that, if maintained, prevent the non-compliance event. The numbers favor compliance by a margin most CFOs find clarifying.
The cost of compliant secure coding training (Req 6.2.2). A defensible 6.2.2-aligned training program — language-specific modules covering each developer's actual stack, hands-on challenges, role-mapped curriculum, evidence-grade completion records — costs in the low five figures annually for a small engineering organization, mid five figures for a mid-sized organization, and into the low six figures for a large enterprise with multiple stacks and hundreds of developers. The full mechanics of what 6.2.2 requires and how a compliant program is structured are covered in our guide to PCI DSS 4.0.1 Requirement 6.2.2 secure coding training.
The cost of skipping it. The training program is one of the requirements the acquiring bank's compliance team checks during the annual reporting cycle. Skipping it produces a finding. The finding produces non-compliance status. The non-compliance status produces the monthly fine schedule. Three to six months of the lower tier of monthly fines exceeds the annual cost of the training program for any organization size. Three to six months of the higher tier exceeds it by an order of magnitude. And that is before any breach-triggered cost layer is considered — the layers where the per-card assessments turn the investment math from "favorable" into "comically favorable".
The same comparison for scanning and awareness. The pattern repeats for every PCI requirement that produces a maintenance cost: the annual ASV subscription, the internal scanning tooling, the awareness training program for the broader workforce, the QSA engagement itself. Each of these is a known, predictable, budgetable line item. The cost of operating without each is unbounded — the monthly fines are bounded by the schedule, but the breach-driven exposure is bounded only by the size of the cardholder data environment and the severity of the eventual incident.
The hidden multiplier. Compliance investments compound. A program that maintains the AOC every year, runs the scans every quarter, and trains the personnel every cycle produces evidence as a continuous byproduct. The marginal cost of producing the AOC in year three is materially lower than the cost of producing the first one, because the systems, the documentation, the workflows, and the team familiarity already exist. A program that lapses and has to be rebuilt mid-cycle pays the full standup cost twice — once before the lapse, and once again to recover. Continuity is the cheapest mode.
A Compliant Training Program Costs Less Than One Month of Non-Compliance Fines
SecureCodingHub's PCI DSS training program covers the developer-specific secure coding training required by Requirement 6.2.2 and the awareness training required by 12.6.1 — language-specific, role-mapped, with the per-developer evidence package your QSA expects. For most organizations, the full annual program runs at a fraction of even the introductory tier of acquiring-bank non-compliance fees. If you want to see exactly how the program would map to your organization's scope and stack, we are happy to walk through it directly.
See a DemoClosing: Compliance Is the Cheapest Path
The numbers in this guide are uncomfortable in aggregate, and the discomfort is the point. The framing of pci dss non compliance fee as a single dollar figure has helped a generation of compliance leaders build budget cases that are too small, because they were sized against a number that captures a fraction of the actual exposure. The real cost of non-compliance is layered: monthly fines from the acquiring bank, separate assessments from each card brand, mandatory PFI engagements after breaches, per-card assessments that scale with the size of the data exposure, increased interchange and reserves, mandatory monitoring periods, loss of the merchant agreement, cyber insurance premium increases, parallel regulatory and class-action exposure, and brand damage that materially impacts revenue for quarters after the event.
The compliance program — secure coding training, awareness training, ASV scans, internal scans, documentation, the AOC, the QSA engagement — exists as a continuous cost line item that every organization processing card data has to budget for. That cost is bounded, predictable, and amortizable. It is also small relative to the bottom layer of any of the breach-driven cost categories. The CFO who reads the comparison correctly does not see compliance as overhead; they see it as the cheapest insurance the organization can buy against a known and quantifiable risk surface, where the policy premium is the operating cost of the program and the deductible-equivalent is the size of an unreduced settlement after a breach traced to remediable failure.
The 2026 cycle is the first full year of PCI DSS 4.0.1 enforcement without grandfather treatment, and the assessor and acquirer posture has hardened across the industry. Organizations that have built defensible programs against the current text — secure coding for 6.2.2, awareness for 12.6.1, scanning for 11.3, documentation for the broader 12 series — pass their annual cycles cleanly and never appear in the cost layers this guide describes. Organizations that have not are exposed, and the exposure is not a policy abstraction. It is a multi-layer financial liability with an upper bound that is, in practical terms, the size of the cardholder data environment itself. The cheapest path through the rest of the decade is the one that starts with an honest reading of where the program is today, against the standard's current text, and a commitment to closing the gap before the cost surface above gets a chance to assert itself.