Most application code in 2026 is not written by the team shipping it. Between framework runtimes, transitive dependency trees, container base images, and language standard libraries, the typical production service is somewhere between 80% and 95% third-party code by line count, and the proportion has been climbing every year for a decade. Software composition analysis — SCA — is the discipline of knowing what is in that supply chain, what is vulnerable, what is reachable, and what is exploitable, and of producing the artifacts (the SBOM, the CVE inventory, the license report) that regulators, customers, and incident responders increasingly demand. This guide walks SCA from a developer's perspective: how it differs from SAST and DAST, where the false-positive crisis comes from, what the tool landscape actually looks like in 2026, how to integrate scanning without drowning the team in noise, and the traps that break SCA programs in their second year.
What SCA Is and How It Differs from SAST and DAST
Software Composition Analysis is the category of tooling that inventories an application's third-party components — the npm packages, the Maven artifacts, the Python wheels, the Go modules, the Rust crates, the container layers — and matches each component against vulnerability databases, license catalogs, and policy rules. Where SAST analyzes the application's own source code for vulnerable patterns, and DAST exercises the running application from the outside, SCA looks sideways at the dependency tree the application pulls in at build or runtime. The three categories are complementary, not competing — a program that runs SAST and DAST but not SCA is missing the largest single attack surface in modern applications, and a program that runs only SCA is blind to vulnerabilities the team itself wrote.
Open source vulnerability scanning emerged as a category in the early 2010s as open-source adoption accelerated and the first wave of high-profile dependency vulnerabilities — Heartbleed in OpenSSL (2014), Shellshock in Bash (2014) — made clear that organizations could not patch what they did not know they had. The early SCA tools were essentially CVE matchers: take a list of installed packages, look up each in the National Vulnerability Database, report the matches. The category has since absorbed license compliance, dependency-update automation, malicious package detection, reachability analysis, SBOM generation, and supply-chain provenance verification, but the core function — knowing what is in the dependency tree and which of it is vulnerable — remains the foundation everything else builds on.
SCA differs from SAST in scope and method. SAST parses the application's source code, builds a control-flow and data-flow graph, and matches the graph against vulnerability patterns the team owns the code for. SCA parses the application's manifest files (package.json, pom.xml, requirements.txt, go.mod, Cargo.toml, Gemfile.lock) and lockfiles, resolves the full transitive dependency tree, and matches each component against external vulnerability databases. SAST findings are about code the team wrote and can fix directly; SCA findings are about code the team uses and must update, replace, or accept the risk of. The remediation pathways are different, the false-positive profiles are different, and the integration points in the SDLC are different.
SCA also differs from DAST in the breadth-versus-depth tradeoff. DAST sees only the endpoints it can reach and the payloads it knows to send; its findings are runtime-confirmed but coverage-limited. SCA sees every declared dependency in the build manifest; its coverage is exhaustive at the inventory level but is downstream of whether the dependency is actually reachable from any executed code path — which is exactly where the false-positive crisis we will cover in section four originates.
Why Dependencies Are 80%+ of Modern Application Code
The percentage of an application that is third-party code is not a guess; it is measurable and consistently startling. A trivial Express.js service in 2026 — a "hello world" with two routes — pulls in roughly 60 direct dependencies and somewhere between 800 and 1,500 transitive ones depending on the version of Express and the Node.js minor it targets. A typical React application with TypeScript, a UI library, a router, and a state manager pulls in 1,500 to 3,000 packages. A Java Spring Boot service is in the same range when you count the runtime classpath. A Python Django app is smaller in package count but larger in code volume per package. The numbers are universal across ecosystems, with only the specific shape of the curve varying.
The economics that produced this state are obvious in retrospect. Open-source libraries solve well-defined sub-problems — date parsing, HTTP client behavior, schema validation, CSV reading — better and faster than any one team can re-solve them. Package managers made the cost of adding a dependency essentially zero at install time. The cultural norm in every major ecosystem is "if it's a one-liner you could write yourself, prefer the dependency anyway." The result is dependency trees that no individual developer on the team has read, much less audited, and a security posture that depends on the integrity of code the team has never seen.
This shift is what makes SCA non-optional in 2026. When the team writes 5% of the code that ships to production, securing only that 5% leaves 95% of the attack surface unmonitored. The OWASP Top 10 has reflected this for years — A06:2021 "Vulnerable and Outdated Components" exists precisely because dependency vulnerabilities are now one of the most common root causes of breach. The 2025 Top 10 update kept A06 in place, and the consensus across industry incident reports is that supply-chain attacks have become the single fastest-growing category of application-security incidents.
The recent incidents that drove this awareness home are worth naming because they shape the threat models SCA programs respond to. Log4Shell (CVE-2021-44228), in late 2021, was a remote-code-execution vulnerability in log4j-core, a logging library buried so deep in Java application stacks that most teams could not initially answer "do we use log4j?" without weeks of investigation. The ua-parser-js compromise (October 2021) saw a popular npm package (8 million weekly downloads) hijacked through credential theft and shipped with a cryptominer and credential stealer. The node-ipc protestware incident (March 2022) saw a maintainer push code that wiped files on machines with Russian or Belarusian IP addresses to a package depended on by tens of thousands of other packages. The xz-utils backdoor (March 2024) saw a multi-year social-engineering campaign land a sophisticated SSH backdoor in a compression library shipped by every major Linux distribution; it was caught by a Microsoft engineer noticing a 500-millisecond latency anomaly in SSH login. The axios npm incident (March 2026) repeated the credential-theft pattern: a long-lived publishing token was used to push malicious versions of one of the most-installed HTTP clients in the JavaScript ecosystem, carrying a cross-platform RAT into every CI environment that ran install before the registry could yank. Each of these incidents reached production-grade software through the dependency channel; each is the kind of incident SCA exists to detect, contain, or — in the xz case — at least make the post-incident remediation tractable.
The Transitive Dependency Problem
If applications were built only on directly declared dependencies, SCA would be a much simpler problem than it is. The hard part is that direct dependencies pull in their own dependencies, those pull in further dependencies, and the resulting transitive tree typically dominates the package count by an order of magnitude. The team picks 30 direct dependencies and inherits 2,000 transitive ones, including packages whose existence they had no knowledge of, maintained by people they have never heard of, with security postures they have not evaluated.
The lockfile is the artifact that makes this tree concrete. package-lock.json (npm), yarn.lock (Yarn), pnpm-lock.yaml (pnpm), poetry.lock (Python), Cargo.lock (Rust), go.sum (Go), Gemfile.lock (Ruby) — each ecosystem has a lockfile that pins every package, direct and transitive, to a specific version with an integrity hash. Lockfiles serve two purposes that matter for security: they make builds reproducible (the same lockfile produces the same dependency tree on every machine) and they make the dependency inventory auditable (the lockfile is the authoritative source of "what is in this build"). A team without a committed lockfile has neither property — every build resolves potentially different versions, and there is no single document the SCA scanner can read to know what was deployed.
A dependency tree fragment that demonstrates the depth problem:
$ npm ls --all
my-app@1.0.0
└─┬ express@4.18.2
├─┬ accepts@1.3.8
│ ├─┬ mime-types@2.1.35
│ │ └── mime-db@1.52.0
│ └── negotiator@0.6.3
├─┬ body-parser@1.20.1
│ ├── bytes@3.1.2
│ ├─┬ debug@2.6.9
│ │ └── ms@2.0.0
│ ├─┬ http-errors@2.0.0
│ │ ├── depd@2.0.0
│ │ ├── inherits@2.0.4
│ │ ├── setprototypeof@1.2.0
│ │ ├── statuses@2.0.1
│ │ └── toidentifier@1.0.1
│ ├── iconv-lite@0.4.24
│ ...Express alone (a single direct dependency) pulls in dozens of transitive packages, several of which — debug, http-errors, body-parser — have themselves had security advisories in the past. The team's risk surface is the union of vulnerabilities across this entire tree, not just the version of Express they pinned.
The trust-chain problem compounds the depth problem. Every package in the tree is published by some maintainer (or maintainer collective) the team has not vetted. The npm registry alone has roughly 3 million packages and 1.5 million publishers in 2026. The team trusts the entire chain transitively when it installs a single direct dependency — if any maintainer in that chain pushes a malicious update, the application picks it up on the next dependency resolution unless versions are pinned and integrity hashes are verified. This is the structural weakness the supply-chain attacks of the last five years have exploited, and it is the reason lockfiles, pinned versions, and integrity hashing are no longer optional best practices but baseline hygiene.
A package.json fragment showing the difference between unpinned, range-pinned, and exactly-pinned versions:
{
"dependencies": {
"express": "*", // any version — unsafe
"lodash": "^4.17.21", // 4.x.x compatible — minor/patch drift
"axios": "~1.6.5", // 1.6.x — patch drift only
"left-pad": "1.3.0" // exactly 1.3.0 — pinned
}
}The caret range (^4.17.21) means "compatible with 4.17.21" and will pull in any 4.x.y version with x ≥ 17 or x = 17 and y ≥ 21. The tilde range (~1.6.5) means "approximately 1.6.5" and will pull in any 1.6.y version with y ≥ 5. The exact pin (1.3.0) gets exactly that version. The lockfile resolves all of these to specific versions on first install, but if the lockfile is regenerated, the resolution can drift within the constraint. The discipline that produces consistent, auditable supply chains is to commit lockfiles, pin direct dependencies as tightly as your update cadence allows, and verify integrity hashes on every install.
CVE Scanning vs Reachability — The False-Positive Crisis
The first generation of SCA tools, and the majority of free scanners shipped today, perform CVE matching: they enumerate the packages in the dependency tree, look up each package-version pair in a vulnerability database, and report any match as a finding. This produces exhaustive coverage and an industrial volume of false positives. A typical 2026 enterprise application with 2,000 dependencies will produce 80 to 200 CVE findings on first scan; an honest reachability analysis of those findings will conclude that 5 to 15 are actually exploitable in the application's specific code paths and configuration. The remaining 90% are real CVEs in real packages but in code paths the application does not exercise, in functions the application does not call, or in configurations the application does not enable.
The false-positive ratio is the single largest predictor of whether an SCA program succeeds or fails. A team that gets 200 CVE findings and triages them all by hand will burn out within two sprints; a team that gets 200 findings and ignores them all will miss the five that matter. The middle path — actually distinguishing the exploitable findings from the noise — requires either expensive senior-engineer triage time on every finding or a tool that does reachability analysis automatically.
Reachability analysis is the technique that closes this gap. Rather than reporting every CVE in every dependency, a reachability-aware scanner traces from the application's entry points (its public API, its CLI handlers, its job processors) through the call graph into the dependency code, and reports only CVEs in functions that the application actually calls. The technique has been productized by Snyk's "reachability" feature, Endor Labs' "Reachable Vulnerabilities," Mend's "Effective Usage Analysis," and Socket's runtime analysis, and is one of the most active research areas in SCA tooling. The tradeoffs are significant — reachability is computationally expensive, has its own false-negative profile (dynamic loading and reflection break static call-graph analysis), and produces different results across language runtimes. A team that invests in reachability analysis typically cuts triage volume by 60-80% and concentrates engineering attention on the findings that actually matter.
A npm audit output that demonstrates the volume problem:
$ npm audit
# npm audit report
minimist <0.2.4
Severity: critical
Prototype Pollution in minimist
fix available via `npm audit fix --force`
semver <5.7.2
Severity: high
semver vulnerable to RegEx DoS
fix available via `npm audit fix`
47 vulnerabilities (3 low, 18 moderate, 21 high, 5 critical)Forty-seven findings on a small project is typical. Triaging each requires asking: does my code path actually call the vulnerable function? Is the vulnerable code reachable from any HTTP route, message handler, or scheduled job? Is the impact in my deployment context what the CVE describes, or is it muted by my runtime configuration? These are research questions, and they are the work that distinguishes SCA-as-noise from SCA-as-signal.
SBOM Generation — Required by US EO 14028 and EU CRA
The Software Bill of Materials — SBOM — is the artifact that makes a software product's composition machine-readable. It is a structured list of every component (with version, license, supplier, and integrity hash) that goes into a build, in a format that downstream tools can consume for vulnerability scanning, license checking, and supply-chain verification. SBOMs were a compliance curiosity until 2021; in 2026 they are mandatory for any software sold to the US federal government (under Executive Order 14028 and the implementing OMB memos), required for products entering the EU market under the Cyber Resilience Act, and increasingly demanded by enterprise procurement teams as a precondition for contract award.
The two formats that matter in practice are CycloneDX (originated by OWASP, JSON or XML) and SPDX (originated by the Linux Foundation, JSON or YAML or tag-value). CycloneDX is the more developer-friendly format and dominates in CI/CD contexts; SPDX has deeper roots in license-compliance tooling and is required by some procurement frameworks. Modern SCA tools generate both, and modern build systems are increasingly producing them as a side effect of compilation rather than as a separate step.
A trimmed CycloneDX SBOM fragment showing the structure:
{
"bomFormat": "CycloneDX",
"specVersion": "1.5",
"serialNumber": "urn:uuid:3e671687-395b-41f5-a30f-a58921a69b79",
"version": 1,
"metadata": {
"timestamp": "2026-04-25T10:00:00Z",
"tools": [{ "vendor": "anchore", "name": "syft", "version": "1.0.0" }],
"component": {
"bom-ref": "my-app@1.0.0",
"type": "application",
"name": "my-app",
"version": "1.0.0"
}
},
"components": [
{
"bom-ref": "pkg:npm/express@4.18.2",
"type": "library",
"name": "express",
"version": "4.18.2",
"purl": "pkg:npm/express@4.18.2",
"licenses": [{ "license": { "id": "MIT" } }],
"hashes": [
{ "alg": "SHA-256",
"content": "9e1f3..." }
]
}
]
}The Package URL (purl) — pkg:npm/express@4.18.2 — is the canonical identifier that downstream tools use to look up the component in vulnerability databases. The integrity hash binds the SBOM to the specific bytes that were in the build; if the package contents change, the hash invalidates the SBOM, and supply-chain verification tools detect the mismatch.
The regulatory pressure on SBOM is unlikely to recede. EO 14028 has produced a stream of follow-on regulations from CISA, NIST, and federal procurement; the EU CRA's compliance window closes through 2027 and pulls every product sold in the EU market into a labeling and disclosure regime that includes SBOM-equivalent reporting. The teams that have integrated SBOM generation into their build pipelines treat it as a side effect of CI rather than a quarterly compliance scramble; the teams that haven't are increasingly finding themselves unable to bid on procurement opportunities or facing CRA non-compliance fines.
Dependency Confusion, Typosquatting, and Namespace Hijacking
The supply-chain attacks of the last five years have shifted from "exploit a CVE in a popular package" to "get the team to install a malicious package on purpose." This category — sometimes grouped under "supply-chain attacks" or "package-ecosystem attacks" — is where SCA's traditional CVE matching is least effective and where dedicated supply-chain scanners have emerged as a separate tier of tooling.
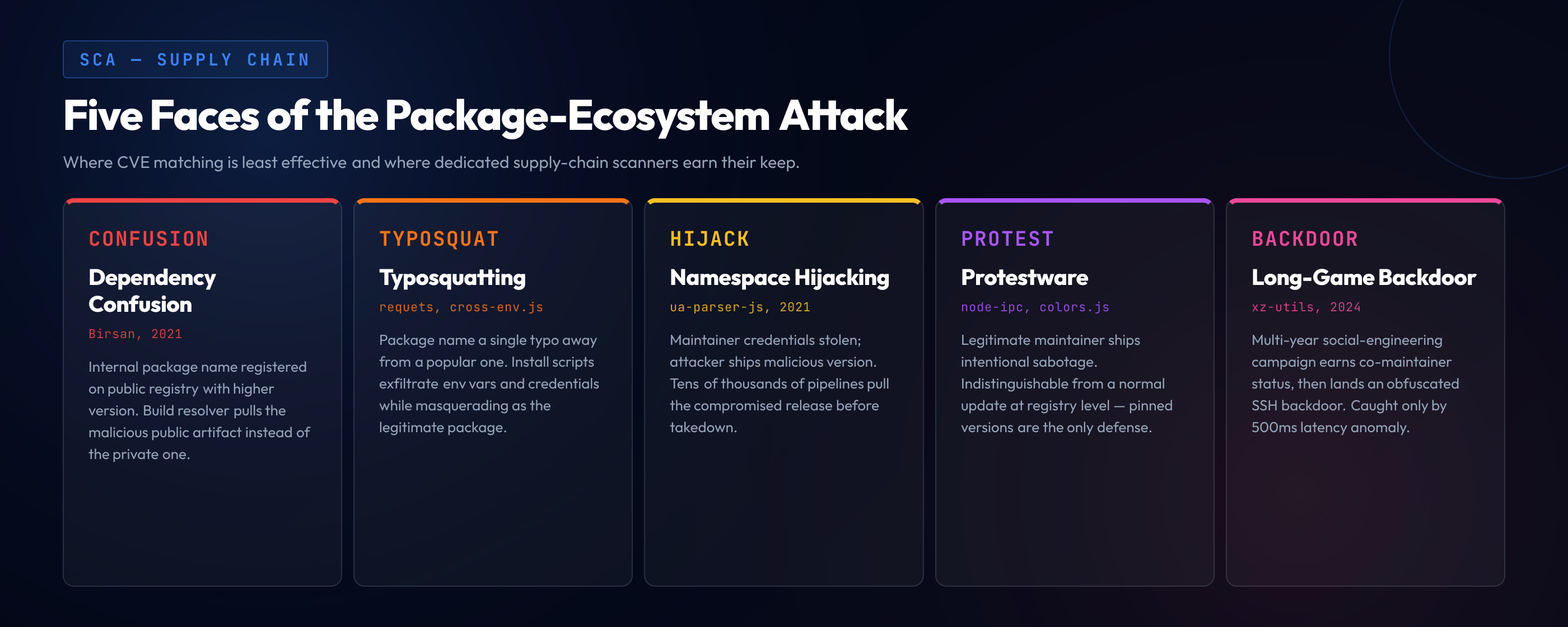
Dependency confusion attack. Discovered and demonstrated by Alex Birsan in 2021 against Apple, Microsoft, PayPal, and dozens of other major companies. The attack works against any organization that uses internal package names alongside public registry packages: the attacker registers the internal name on the public registry with a higher version number than the internal one, and any build system configured to prefer the highest available version pulls the public (malicious) package instead of the internal one. The fix is to either pin the registry source per package (npm's overrides field, scoped packages with private-registry resolution) or to configure the package manager to fail rather than fall back to the public registry for known-internal names. Modern SCA tools detect the misconfiguration that enables dependency confusion before an attacker exploits it.
Typosquatting. The attacker registers a package with a name very close to a popular one — requets instead of requests, cross-env.js instead of cross-env, colors capitalized differently — and waits for typos in install commands or copy-paste from documentation. The malicious package typically does the legitimate thing the user intended (so the install appears successful) plus exfiltrates environment variables, credentials, or browser cookies. The npm and PyPI registries take down typosquats when reported but cannot detect them proactively at the rate they are published. Tools like Socket and Phylum scan packages at install time for behaviors that suggest typosquatting (network calls during install scripts, access to credential files, post-install hooks that download additional code) and block them before they execute.
Namespace hijacking and account takeover. The maintainer of a popular package has their npm or PyPI credentials stolen, and the attacker pushes a new version with malicious code. The ua-parser-js compromise of 2021 followed this pattern: the maintainer's account was compromised, three malicious versions were published over the course of an hour, and tens of thousands of build pipelines pulled the compromised version before the issue was detected. The structural defenses are 2FA enforcement on package publishing (npm now requires this for high-impact packages, PyPI does for top-1% packages), package signing (Sigstore for npm, PEP 458 for PyPI, both still partial in adoption), and integrity verification on every install. The operational defense is to delay automatic dependency updates by 24-72 hours and to monitor security advisories during that window — the malicious version of ua-parser-js was identified and pulled within four hours of publication.
Protestware. A maintainer pushes a politically motivated update — the node-ipc incident of March 2022 wiped files on machines with IP addresses geolocated to Russia or Belarus, the colors.js incident of January 2022 introduced an infinite loop that broke any CLI using the package. The malicious code is shipped intentionally by the legitimate maintainer rather than by an attacker who has hijacked the account, which makes it indistinguishable from a normal update at the registry level. The defenses are the same as for any malicious update — pinned versions, delayed update windows, behavioral analysis of new versions, and the operational practice of treating every dependency update as a code-review event rather than a rubber-stamp.
The xz-utils backdoor. Disclosed in March 2024, the most sophisticated supply-chain attack documented to date. A maintainer (operating under the persona "Jia Tan") gained co-maintainer status on xz-utils through a multi-year social-engineering campaign, then introduced a carefully obfuscated SSH backdoor into the build process. The backdoor was caught by Andres Freund, a Microsoft engineer investigating a 500ms latency anomaly in SSH logins on a Debian testing system, before it reached stable releases of major Linux distributions. The incident demonstrated that even with reproducible builds, signed packages, and integrity verification, a sufficiently patient attacker can land a backdoor through the maintainer-trust channel. SCA tooling cannot defend against this class on its own; defense requires reproducible-build verification, the broader SLSA framework for supply-chain integrity, and human auditing of dependencies that occupy critical-path positions in the trust graph.
The 2026 Tool Landscape — Honest Tradeoffs
The SCA tool market has consolidated around a small number of dominant commercial vendors, a healthy ecosystem of open-source scanners, and a layer of supply-chain-focused tools that emerged in response to the post-2021 incident wave. The tools differ in coverage, accuracy, integration depth, pricing, and the specific problems they solve. No single tool is a universal best choice; the right combination depends on the team's stack, regulatory context, and engineering capacity.
GitHub Dependabot. Free, integrated into GitHub, the default starting point for most teams. Detects vulnerable dependencies, generates pull requests for updates, supports most major ecosystems. Its strengths are zero-cost adoption and automatic remediation PRs; its weaknesses are that it relies on the GitHub Advisory Database (which is comprehensive but not exhaustive), it has no reachability analysis, and its triage workflow is limited compared to dedicated tools. For a team starting from zero on a small-to-medium codebase, Dependabot covers the basics adequately. For a team with thousands of repositories, complex monorepo structures, or compliance requirements, Dependabot is a foundation that needs additional tooling layered on top.
Snyk Open Source. The dominant commercial SCA tool by adoption. Strong vulnerability database (Snyk Intel), good reachability analysis, deep IDE integration, and broad ecosystem support. Its strengths are its triage workflow, its license-compliance features, and the integration depth of its developer tooling; its weaknesses are that pricing scales steeply with team size, and the proprietary database has periodically lagged GitHub Advisory in publishing speed for high-profile CVEs. For an organization above 100 engineers with a real budget for security tooling, Snyk is a defensible default. For a smaller team or one with strong open-source preferences, the price-to-value ratio is harder to justify.
Mend (formerly WhiteSource). Long-established commercial SCA, especially strong in enterprise Java and .NET ecosystems. The "Effective Usage Analysis" feature — Mend's branding for reachability — is mature. Pricing and complexity are enterprise-tier; integration setup is non-trivial. Mend competes with Snyk for the same enterprise budgets and is the more common choice in older Java-heavy organizations.
Socket. A newer entrant focused specifically on supply-chain attacks rather than CVE matching. Socket scans packages at install time for behaviors associated with malicious code — install scripts that touch the network, access to credential files, obfuscated payloads, sudden permission expansions across versions — and blocks suspicious packages before they reach the build. Socket complements rather than replaces traditional SCA; teams that have dealt with supply-chain attacks generally run Socket alongside their CVE scanner.
OSV-Scanner. Google's open-source SCA tool, built on the OSV (Open Source Vulnerabilities) database. Free, fast, supports the major ecosystems, integrates cleanly with CI. The OSV database aggregates vulnerability data from GitHub Advisory, PyPA, RustSec, Go's vulnerability database, and ecosystem-specific sources; coverage is comparable to Dependabot's underlying GitHub Advisory feed. OSV-Scanner does not have reachability analysis, but it is the strongest free option for teams that want SCA without committing to a paid vendor.
Trivy. Aqua Security's open-source scanner, originally focused on container images but extended to filesystem and dependency scanning. Fast, well-maintained, and broadly adopted in cloud-native environments. Trivy's particular strength is container scanning — analyzing the OS packages, language packages, and configuration of a container image in a single pass — which makes it the de facto standard in Kubernetes contexts.
Grype and Syft. Anchore's open-source scanner (Grype) and SBOM generator (Syft), often used together. Syft generates an SBOM in CycloneDX or SPDX format from a filesystem, image, or directory; Grype takes the SBOM (or scans directly) and produces vulnerability findings. The split — generate the SBOM once, scan it many times — is operationally useful in pipelines that produce SBOMs as compliance artifacts.
The npm audit alternatives landscape. Most teams discover SCA through npm audit (or yarn audit, pnpm audit) and find quickly that the experience is unsatisfying — high false-positive rates, narrow ecosystem coverage, limited triage workflow. Modern alternatives — Snyk, OSV-Scanner, Socket, Trivy — improve on the basic audit experience in different directions. For a team feeling friction with npm audit, the question is not "which tool is best" but "which axis of npm audit's friction matters most" — false positives, supply-chain attacks, license compliance, or build-time integration.
An honest summary of the tradeoffs: Dependabot is the right starting point for most teams. Snyk is the right next step if budget allows and reachability matters. OSV-Scanner is the right alternative if budget is constrained or the team prefers open-source. Socket is the right complement when supply-chain attacks are a real concern. Trivy vs Grype is the dominant container-scanner question, and it typically lands on Trivy for broad cloud-native coverage and on Grype for SBOM-centric workflows. The teams that have mature SCA programs in 2026 typically run two or three of these in combination, not one in isolation.
Pipeline Integration — PR-Time, Build-Time, Runtime
SCA produces value only when its output reaches developers in time to act on it. The integration question — where in the SDLC the scanner runs, how findings are surfaced, and how they block (or don't block) progress — is the difference between an SCA program that catches vulnerabilities and one that produces dashboards no one reads.
PR-time scanning. The scanner runs on every pull request that modifies a manifest or lockfile, comparing the new dependency tree against the old and reporting only the deltas — new vulnerabilities introduced, existing vulnerabilities resolved, license changes. PR-time scanning is the integration point most likely to influence developer behavior because the finding appears in the same context as the change that introduced it; the developer reviewing their own PR can adjust the dependency choice immediately rather than dealing with a backlog ticket weeks later. The tradeoff is that PR-time scanning sees only the diff, not the full inventory, and can miss findings that exist in dependencies the PR did not touch.
A GitHub Actions snippet running OSV-Scanner on every pull request:
name: SCA Scan
on:
pull_request:
paths:
- 'package.json'
- 'package-lock.json'
- 'pom.xml'
- 'requirements.txt'
- 'go.mod'
- 'Cargo.lock'
jobs:
scan:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v4
- name: Run OSV-Scanner
uses: google/osv-scanner-action@v1
with:
scan-args: |-
--recursive
--skip-git
./
- name: Generate SBOM
uses: anchore/sbom-action@v0
with:
format: cyclonedx-json
output-file: sbom.json
- uses: actions/upload-artifact@v4
with:
name: sbom
path: sbom.jsonBuild-time scanning. The scanner runs on the full dependency tree as part of CI, on every commit to main or on a scheduled cadence. Build-time scanning produces the comprehensive inventory — every dependency, every CVE, every license — and is the input to compliance reporting and SBOM publication. The output is too voluminous to review on every commit; the workflow that succeeds is a triaged dashboard, an alert system that fires on new high-severity findings, and a periodic review cadence for the long tail. Build-time scanning is also where reachability analysis runs, because reachability requires the full call graph of the application and its dependencies — an analysis too expensive to run on every PR.
Runtime scanning. The newest integration tier, where the scanner observes the running application and identifies which dependencies are actually loaded at runtime. Runtime SCA — productized by Sysdig, Datadog ASM, Snyk's runtime monitoring, and others — closes the reachability gap from a different angle: rather than statically analyzing whether a vulnerable function could be reached, it observes whether the function is actually called in production traffic. Runtime data is the gold standard for triage; a CVE in a function the application has never loaded in production is far less urgent than one in a function called on every request.
The blocking-versus-warning tradeoff. A scanner that fails the build on every CVE finding produces revolt within two weeks. A scanner that only warns produces findings the team learns to ignore. The middle path is to fail builds on a narrow, high-confidence policy — critical-severity CVEs introduced by the current PR, license violations on copyleft-incompatible licenses, missing SBOM for compliance-required builds — and warn on everything else. The blocking policy should be small enough that violations are rare and obvious; the warning policy should feed a triage workflow that periodically clears the backlog.
If you want hands-on practice integrating SCA into a realistic pipeline — including the triage workflow that actually scales to a production codebase — our platform's hands-on labs walk through the integration patterns end-to-end with real vulnerable dependencies and real fix paths.
License Compliance — Often Bundled with SCA
Most commercial SCA tools include license-compliance features alongside vulnerability scanning, and the combination makes operational sense — both questions ("is this dependency vulnerable?" and "is this dependency's license compatible with our distribution model?") are answered from the same dependency inventory. The license question gets less attention from security teams than the vulnerability question but produces real legal exposure when ignored.
The license categories that matter for compliance: permissive licenses (MIT, BSD, Apache 2.0) that allow essentially any use including commercial redistribution; copyleft licenses (GPL, AGPL) that require derivative works to be released under compatible licenses, with AGPL extending the requirement to networked services; weak-copyleft licenses (LGPL, MPL) that allow linking from proprietary code with conditions on the licensed code itself; and "non-standard" or "non-commercial" licenses that introduce per-use legal review requirements. The combination that produces sudden surprises is a SaaS product that has accumulated AGPL-licensed dependencies through transitive resolution — the AGPL's network-distribution clause potentially requires the entire service to be released as AGPL, which most SaaS business models cannot tolerate.
The mature license-compliance practice is to maintain an allowlist of acceptable licenses (typically the major permissive licenses plus the company's specific accepted weak-copyleft list) and to fail the build on any introduction of a non-allowlisted license. The triage cost on first adoption is high — every existing dependency gets reviewed once — but the steady-state cost is low because new license introductions are rare in mature codebases. The companies that handle this well treat license compliance as a compliance function adjacent to security; the companies that ignore it discover the problem during due diligence on an acquisition or partnership and pay multiples to remediate retroactively.
Common SCA Traps and How to Avoid Them
SCA programs fail in predictable ways. The traps are not exotic; they are common mistakes that recur across organizations and industries, and recognizing them in advance saves more program-time than any specific tool choice.
The dashboard-without-action trap. The team buys an SCA tool, integrates it into CI, and produces a dashboard with 800 findings. No one is responsible for triaging the dashboard. The dashboard accumulates findings over months. The number reaches 2,000. At some point, the team treats the dashboard as background noise. The investment in tooling produces no risk reduction. The fix is to assign a specific owner — a security champion, a designated rotation, a dedicated team — to the triage workflow before the tool is deployed, and to define the cadence at which the backlog is reviewed.
The blocking-everything trap. The team configures the scanner to fail the build on any finding. Every PR fails for the first month. The team disables the scanner. The investment in tooling produces no risk reduction. The fix is to start with a narrow blocking policy (critical-severity, current-PR-only, easily-remediated) and expand the policy as the team's triage workflow matures and the backlog shrinks.
The lockfile-not-committed trap. The team scans manifests but not lockfiles. The scanner reports CVEs based on the version range declared in the manifest, not the version actually resolved at install time. The findings are theoretical; the actual deployed dependency tree is unmonitored. The fix is to commit lockfiles, scan lockfiles, and reproduce builds from lockfiles — the basic hygiene that makes SCA findings correspond to actual deployed risk.
The SBOM-as-PDF trap. The team generates SBOMs for compliance, exports them as PDFs, files them in a SharePoint folder, and never re-reads them. The SBOM is a compliance artifact, not an operational input. The fix is to publish SBOMs in machine-readable form (CycloneDX or SPDX JSON), store them alongside builds in a registry that downstream tools can consume, and run continuous vulnerability scanning against the SBOM inventory rather than treating the SBOM as a one-time output.
The patch-without-test trap. The team accepts every Dependabot PR automatically. A minor-version dependency update introduces a regression. The team ships the regression to production. Confidence in automatic updates collapses. The team disables Dependabot. The fix is to invest in test coverage that catches regressions on dependency updates, to merge automatic updates into a staging environment first, and to use canary deployments that catch runtime regressions before they reach all users.
The transitive-update-impossible trap. A vulnerable transitive dependency cannot be updated because the direct dependency that requires it has not released a compatible version. The team is stuck — the SCA scanner reports the CVE, and there is no upstream fix. The options are to fork and patch the dependency (high engineering cost, long-term maintenance burden), use an override mechanism (npm overrides, Yarn resolutions, Maven dependency management) to force a compatible version, accept the risk after reachability analysis confirms the vulnerable function is not called, or replace the direct dependency entirely. The right answer depends on the specific case; the wrong answer is to ignore the finding and hope nothing happens.
The vendor-locked-database trap. The team relies entirely on a single vendor's vulnerability database. A high-profile CVE is published with a delay in that vendor's database. The team is unaware of the vulnerability for days while other teams using other databases are already patching. The fix is to consume multiple sources — GitHub Advisory, OSV, the vendor's database, ecosystem-specific sources — and treat the union as the working set rather than relying on any single source.
SCA Tools Find Vulnerable Dependencies. Developers Decide What to Do About Them.
A scanner that flags 200 CVEs in CI is the start of the work, not the end. The hard part of an SCA program is the triage — distinguishing the exploitable findings from the noise, deciding when to update, when to override, when to fork, and when to accept the risk after reachability analysis. SecureCodingHub's platform builds the dependency-aware judgment that turns SCA from a backlog generator into operational signal: developers who understand transitive trust chains, who know how to read a reachability report, who can navigate dependency-update tradeoffs without senior-engineer hand-holding. If your team is drowning in CVE findings or struggling to operationalize SBOM compliance, we'd be glad to walk you through how our program changes the triage side of that pipeline.
See the PlatformClosing: SCA as Continuous Practice, Not One-Time Compliance
The mistake that the largest number of SCA programs make is treating the discipline as a compliance line-item: a quarterly scan, a generated PDF, a checkbox on the audit form. Every analysis above — the false-positive crisis, the transitive-trust problem, the runtime-versus-static-reachability debate, the supply-chain attack landscape — points the other direction. SCA is not a periodic audit. It is a continuous practice that runs alongside development, integrates into PR-time and build-time and runtime, produces ongoing findings that require ongoing triage, and changes shape as the threat landscape changes shape. The xz-utils backdoor was not on anyone's threat model in 2023; it dominated the threat model for the next year. The dependency-confusion attack was a research curiosity in 2020; it became a baseline misconfiguration concern in 2021. The threat landscape evolves, the tooling evolves with it, and the SCA program that does not evolve with both becomes the program that ships the next high-profile incident.
The teams that have mature SCA programs in 2026 share a small set of practices. They commit lockfiles and pin versions tightly. They generate SBOMs as a side effect of every build, in machine-readable formats, stored alongside the artifacts. They run multiple scanners — at minimum a CVE scanner with a strong database and a supply-chain scanner with behavioral analysis. They have explicit owners for the triage workflow and explicit cadences for backlog review. They invest in reachability analysis, either through tooling or through senior-engineer judgment, to keep the noise floor manageable. They treat dependency updates as code-review events, not rubber-stamps. They monitor the security advisory streams for the ecosystems they depend on. They have an incident-response playbook for "we shipped a vulnerable dependency to production" that does not start from scratch on the day it happens.
None of these practices is exotic. The institutional commitment to apply them consistently — across the full dependency tree, across every build, across every team — is what separates SCA programs that produce signal from SCA programs that produce dashboards. For developers, the takeaway is that SCA is not a tool you buy or a scan you run. It is a way of thinking about the third-party code that makes up the bulk of what you ship, and a discipline of treating that code with the same rigor you treat the 5% you wrote yourself. The supply chain is the largest attack surface in modern applications; securing the cryptographic foundations and the application code is necessary but not sufficient if the dependency tree is unmonitored. Knowing what is in your software, what of it is vulnerable, what of it is reachable, and what of it is exploitable — that is the working definition of software composition analysis, and it is the practice that the rest of application security increasingly depends on.