DevSecOps engineering has stopped being a buzzword and become a job description. The function — building the security pipeline every developer commits through, every build runs against, and every deploy passes by — sits in dedicated roles at most engineering orgs of meaningful size. This guide describes what the role does in 2026, the skills that distinguish a strong engineer from a tool operator, how it compares to SRE and traditional security engineering, the toolchain, org patterns, career pipelines, and the anti-patterns that wreck programs no matter how much budget they were given.
What Is DevSecOps Engineering?
DevSecOps engineering is the discipline of integrating security into the software delivery pipeline so that security testing, policy enforcement, and remediation happen continuously alongside the build, test, and deploy flow rather than as a separate gating activity tacked on at the end. The defining property is continuity: a DevSecOps program is a set of always-on controls that produce findings as code is written, dependencies are added, containers are built, and infrastructure is deployed.
It is worth distinguishing DevSecOps engineering from "DevOps with security awareness." A DevOps team that runs a SAST scan once a quarter and patches when something breaks is doing security-adjacent work; it is not running a DevSecOps program. DevSecOps is its own function with dedicated tooling, dashboards, SLAs, and headcount that owns the security signal end to end. Organizations with a real DevSecOps function track how long critical findings stay open and how the rate of new findings trends over time. Organizations doing "DevOps with security awareness" track whether the last scan ran.
The terminology has stabilized. From roughly 2018 to 2022 the dominant title was "AppSec engineer," focused on application security testing — SAST, DAST, code review, threat modeling. As the scope expanded into infrastructure as code, container security, runtime detection, and pipeline security itself, AppSec became too narrow. By 2024-2026 "DevSecOps engineer" had become standard at most organizations of meaningful size — one umbrella function with subspecialties inside it.
What a DevSecOps Engineer Actually Does
DevSecOps responsibilities fall into a recognizable set of duties, each with a tooling and a human dimension. The job is not "run scanners" — the job is to operate a continuous security feedback loop in which scanners are one input among several.
Owns the security tooling pipeline. SAST in pull requests, DAST in staging, IAST when the application supports it, SCA for dependency scanning, container image scanning, IaC scanning for Terraform and Kubernetes manifests, secret scanning across source and build artifacts. The DevSecOps engineer chooses the tools, integrates them into CI/CD, configures them for the org's languages, and keeps them running as the org evolves.
Designs and tunes detection rules and severity policies. Out-of-the-box SAST and DAST configurations are noisy. A real DevSecOps engineer tunes rule sets to the team's actual code, writes custom rules, and calibrates severity so what reaches a developer's queue is worth their attention.
Runs the triage flow. Raw scanner output is not actionable. The DevSecOps engineer deduplicates, validates, contextualizes, and routes findings to the team that owns the affected code. A finding without an owner is a finding that doesn't get fixed.
Partners with platform and SRE teams on infrastructure security controls. Network policy enforcement, IAM model design, runtime detection on the container platform, secret management — these usually live in platform or SRE teams, but the DevSecOps engineer collaborates on the security requirements and operates the rules deployed to the runtime layer.
Maintains the security gates in CI/CD. Which findings break the build, and which warn? The DevSecOps engineer owns the break-vs-warn policy and operates the exception process. Get this wrong and developers either bypass gates or hate the program.
Produces metrics for engineering leadership. Mean time to remediate by severity, finding density per service, security debt trends, percentage of services with clean security gates. Leadership needs to see program impact in numbers.
Responds to security incidents at the application and pipeline layer. When a vulnerability hits the news that affects the org's stack, the DevSecOps engineer is in the response. Pipeline incidents — compromised build server, malicious dependency — sit specifically with this role.
Trains developers on the toolchain and remediation patterns. The DevSecOps engineer is the person who explains what the tools find, why a finding matters, and how to fix it correctly. Every new finding is a teaching moment if the team uses it that way.
Skills That Define a Strong DevSecOps Engineer
DevSecOps skills form a hybrid that does not match any single traditional engineering track. A strong DevSecOps engineer reads code like an application engineer, operates infrastructure like an SRE, and thinks about adversaries like a security engineer. The combination is rare; people who have it tend to assemble it intentionally.
Technical skills. Comfortable in two or three languages used by the engineering org — not expert, but fluent enough to read code, understand what a finding is reporting, and write a proof-of-concept fix when needed. Fluent in CI/CD: GitHub Actions and GitLab CI are dominant in 2026, with Jenkins still common at older orgs and ArgoCD for the deploy side. Comfortable with Kubernetes and at least one major cloud, with IAM models being the part that matters most because IAM is where most cloud security findings actually live. Familiar with the SAST, DAST, and IAST tooling categories (covered in our IAST vs DAST vs SAST comparison) so they can choose tools intelligently rather than buying whatever the loudest vendor is selling. Able to write detection rules — Semgrep patterns, CodeQL queries, OPA/Rego policies, custom YARA-style rules. Can read incident response timelines and reverse engineer how a flaw reached production.
Soft skills. Persuasion is a recurring requirement: security ROI is an argument the DevSecOps engineer makes many times to many audiences. Facilitation matters because finding owners is half the work — the DevSecOps engineer is constantly negotiating which team owns code or infrastructure that nobody wants to claim. The most underrated skill is the ability to tell developers "no" without becoming a blocker. The diplomatic move is to redirect rather than refuse: "this pattern is unsafe, but here's the equivalent that meets the requirement safely." A DevSecOps engineer who only says no becomes the team's least favorite person; one who redirects becomes the most useful.
DevSecOps Engineer vs SRE vs Security Engineer
DevSecOps vs SRE is the most common confusion, but the boundaries among DevSecOps engineers, SREs, and traditional security engineers are routinely blurred — including by leaders staffing the functions. The clearest way to see the distinction is side by side.
| Responsibility | DevSecOps Engineer | SRE | Security Engineer (traditional) |
|---|---|---|---|
| Vulnerability triage | Owns | Consumes | Co-owns at app layer |
| Infrastructure hardening | Co-owns with SRE | Owns | Reviews |
| Incident response | App and pipeline incidents | Reliability incidents | Security incidents end to end |
| On-call rotation | Often shared with platform | Always | Security on-call (separate) |
| Code review | Security-focused | Reliability-focused | Deep security review |
| Threat modeling | Participates | Rarely | Owns |
| Runtime detection | Owns rules and tuning | Owns platform | Reviews coverage |
| Compliance evidence | Pipeline evidence | Infra evidence | Program-level evidence |
The overlap is real. At smaller organizations — under roughly 200 engineers — one person often wears all three hats, splitting time across pipeline security, infrastructure reliability, and security incident response. At larger orgs the roles separate but collaborate intensely on shared tooling. The runtime detection platform is a typical example: the SRE team owns the platform infrastructure (the agent, the data pipeline, the storage), the DevSecOps engineer owns the rules deployed to it, and the traditional security engineer reviews coverage and contributes threat-modeled detection requirements. The same shared-tooling pattern applies to vulnerability management dashboards, IAM tooling, and secret management infrastructure.
The DevSecOps Toolchain
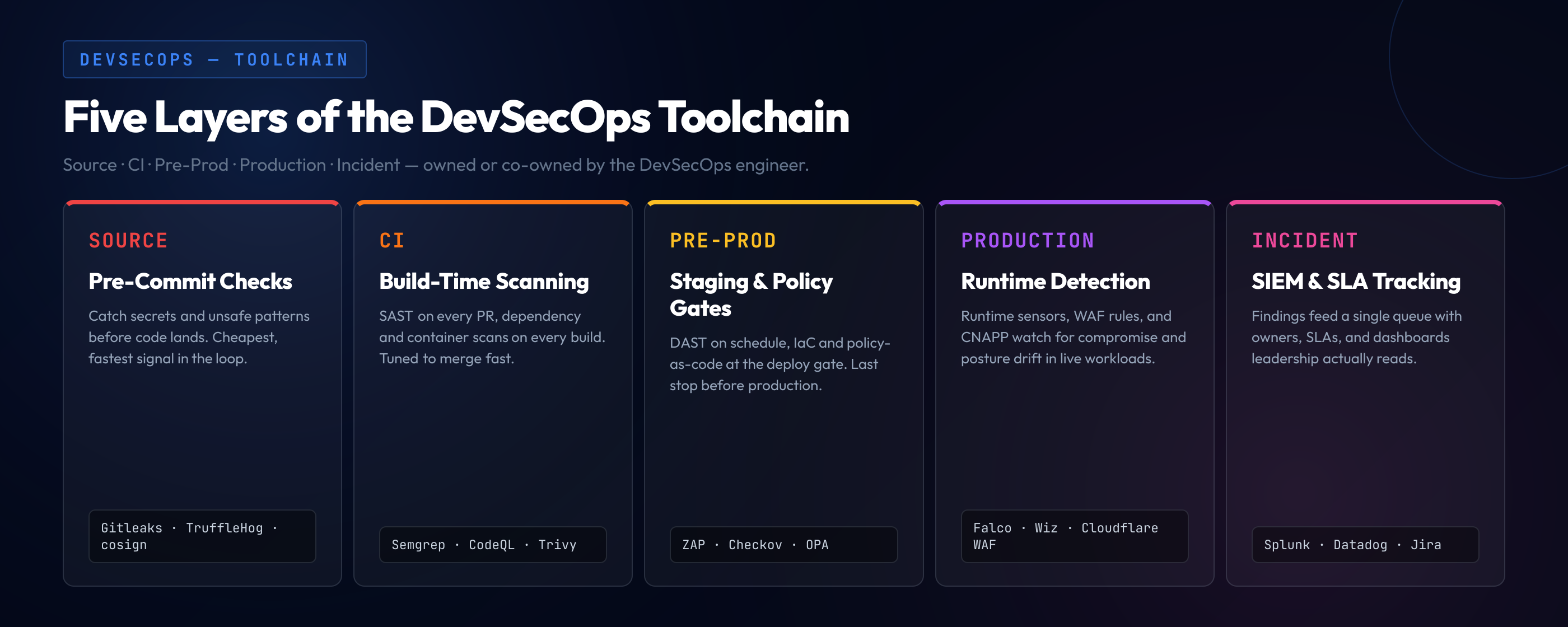
The DevSecOps toolchain in 2026 spans five layers. A 2026 DevSecOps engineer typically owns or co-owns tools in every layer and tunes them to the specific stack the org runs.
Source layer. Pre-commit hooks for the cheapest, fastest checks — secret scanning to catch credentials before they hit history, basic linting for security-relevant patterns, signed commit enforcement at orgs that require it. Tools: Gitleaks and TruffleHog for secret scanning, Sigstore/cosign for commit signing.
CI layer. SAST runs on every pull request — fast enough that developers see results before merge, tuned enough that what they see is real. Dependency scanning checks every lock-file change. Container scanning runs on every image build. Tools: Semgrep, Snyk Code, GitHub CodeQL for SAST; Snyk, Dependabot, Renovate for dependency scanning; Trivy and Grype for container scanning.
Pre-prod layer. DAST scans staging on a schedule. IaC scanning checks every Terraform plan or Kubernetes manifest before apply. Policy-as-code engines enforce architectural constraints — no public S3 buckets, no privileged containers, no IAM wildcards — at the deployment gate. Tools: ZAP and Burp Suite Enterprise for DAST; Checkov, tfsec, and KICS for IaC scanning; OPA and Kyverno for Kubernetes policy.
Production layer. Runtime detection watches for behaviors that indicate compromise — unexpected process trees, suspicious network connections, file integrity violations. WAF rules block known attack patterns at the edge. CSPM and CNAPP tools continuously assess cloud posture and surface drift. Tools: Falco for runtime detection; Cloudflare and AWS WAF at the edge; Datadog Security, Wiz, Lacework, and Orca Security for CNAPP.
Incident layer. SIEM aggregates findings and runtime alerts into a single feed for the on-call engineer. Security ticket SLA dashboards expose which findings are open, how long they have been open, and which teams own them. Tools: Splunk, Elastic, and Datadog for SIEM; Jira or Linear with custom dashboards for ticket SLAs.
An important point about toolchain composition: it matters less than the integration. A great DevSecOps engineer running one open-source tool per category — Semgrep, Trivy, Checkov, OPA, Falco — integrated tightly will outperform a mediocre engineer running the most expensive enterprise stack with default configuration. The bottleneck is rarely tool capability and almost always integration quality, signal-to-noise tuning, and routing to owners.
How DevSecOps Fits Into the Engineering Org
Three org patterns dominate in 2026, each with different tradeoffs. The right pattern depends on the size of the engineering org, the maturity of the security program, and how much variance there is across product teams.
Embedded. DevSecOps engineers sit inside platform or infrastructure teams and share on-call rotations with SREs. The advantage is proximity to delivery — the DevSecOps engineer sees the same incidents the SREs see and is in the room when platform decisions are being made. The disadvantage is depth: an embedded engineer often becomes a generalist with limited bandwidth to develop deep expertise in any one area of the toolchain.
Centralized. A security platform team that owns the tooling and consults across teams. The advantage is depth — engineers can specialize in SAST tuning, IaC policy, or runtime detection and produce expertise the org could not develop with embedded headcount alone. The disadvantage is queue contention: every product team competes for the central team's attention, and the central team becomes a bottleneck.
Federated. Security champions inside each product team, with a small central DevSecOps platform team owning shared infrastructure. The champion is usually a developer with security interest who spends 10-30% of their time on security work. The advantage is reach — every product team has somebody local who can triage. The disadvantage is that federated requires a strong champion program: training, ongoing community, role recognition, and a baseline of developer fluency that makes the role viable. Many orgs anchor the champion program with the kind of fluency baseline a secure SDLC assumes — without that baseline, champions are champions in name only.
The 2026 trend is hybrid: a small central DevSecOps team owning the platform, with embedded champions in each product team handling day-to-day triage. Hybrid takes the depth of centralized and the reach of federated, at the cost of more coordination. Large orgs that have iterated on structure end up at hybrid; those that haven't are usually at one of the pure patterns feeling the corresponding pain.
Career Paths Into DevSecOps Engineering
Five pipelines feed into DevSecOps engineering, each with a recognizable starting point and a known set of gaps to close. Understanding the pipeline you came in on tells you what to focus on next.
DevOps or SRE to DevSecOps. The most common pipeline. People from this direction arrive with strong infrastructure fluency — they know Kubernetes, the cloud IAM models, and CI/CD systems intimately because they built them. The gap to close is application security: they need to learn OWASP-class vulnerabilities at the depth required to read a SAST finding and assess whether it is real, and develop the adversarial intuition the security side depends on.
Application security engineer to DevSecOps. The second most common pipeline. People from AppSec arrive with strong vulnerability fluency — they have read the OWASP Top 10 in actual code many times and run threat models. The gap is pipelines and infrastructure: CI/CD systems deeply enough to integrate tools and operate gates, and IaC and container platforms well enough to participate in infrastructure-side conversations.
Software engineer to DevSecOps. Less common but rising. People from product engineering arrive with strong code-reading speed and the ability to talk to other developers as peers — a real advantage in the persuasion and facilitation parts of the role. The gap to close is the security toolchain and the mental model that comes from breaking things rather than building them.
Security analyst or SOC to DevSecOps. People coming from a SOC arrive with strong detection and incident fluency — they know what an attack looks like in logs and have triaged real incidents. The gap to close is build pipelines and the developer-facing parts of the role: SOC work is often disconnected from the engineering org, and adapting to a function that lives inside engineering requires a workflow shift.
Direct entry from security-focused new grad programs. Rare but growing. A handful of universities have meaningful security curricula and a handful of large engineering orgs have new-grad rotations that include DevSecOps. The gap is breadth: theoretical knowledge but limited operational experience, with the first 12-18 months closing that gap on the job.
The pattern across all five pipelines: bring whichever depth you have, recognize the gaps, and close them deliberately. The security mental model is the hardest piece for engineers from non-security backgrounds because it comes from breaking things rather than building them. CTF for developers and bug bounty programs are the standard self-development paths — both expose you to the offensive perspective in a structured environment and produce an artifact that demonstrates the perspective is real rather than claimed.
Anti-Patterns That Wreck DevSecOps Programs
The failure modes of DevSecOps programs are recognizable across organizations and industries. Each one is the result of treating the function as a tool deployment rather than as an operational program with its own discipline.
Tools without practice. The team buys SAST, DAST, IAST, SCA, and container scanning. The dashboards fill with thousands of findings. Nobody triages, nobody remediates, nobody tunes the rules. After a few months the dashboards become background noise and people stop opening them. The budget was spent, the tools are running, the program is failing. This is the most common failure mode and the one that wastes the most money.
Gates without exception process. Security CI checks are configured to block builds for every finding regardless of severity, with no exception path for false positives or cases where severity does not justify a release block. Developers learn to bypass the gates or to hate the program. Either outcome is bad for security.
Findings without owners. Security tickets pile up in a generic "security backlog" that no team owns. There is no SLA because there is no owner to enforce it against, no escalation path because there is no defined chain, and no closure rate because nobody is responsible. This pattern is the single biggest predictor of program stagnation.
Metrics without context. The org reports "we ran 47,000 scans this quarter" instead of "we reduced critical findings open more than 30 days from 47 to 6." Activity metrics are easy to produce and meaningless to leadership; outcome metrics are what leadership actually needs to see. A program producing activity metrics tends to be running but not improving.
Security as policy police rather than engineering partner. The DevSecOps team spends its time enforcing rather than enabling — saying no without offering the redirect, blocking work without offering the path forward, treating findings as a way to demonstrate value rather than as material to drive the engineering org toward safer patterns. Programs in this mode become blockers rather than multipliers and lose the political capital they need to do their actual job.
Closing: A Pipeline of Findings Nobody Closes Is Not a Security Program
The recurring lesson across every successful DevSecOps program is the same: the engineer's job is not to surface findings. The tools surface findings. The job is to make sure findings reach the right developer with enough context to fix them, that the fix lands within an SLA appropriate to severity, and — most importantly — that the same class of finding does not recur. A program that surfaces 10,000 findings and closes 200 is unsuccessful, because the open 9,800 are the actual security posture and they are getting worse over time.
Preventing recurrence depends on something outside the toolchain: developer fluency in the vulnerability categories the tools surface. A great DevSecOps program produces a closed loop. Tools find issues. Developers fix them and learn the pattern. Training reinforces the pattern. Future code has fewer of those issues. The cycle accelerates as developers internalize the patterns and the residual finding flow gets more interesting because the easy categories have been engineered out.
One category is where DevSecOps tooling has the highest leverage: security misconfiguration. IaC scanning catches infrastructure misconfiguration before deployment that DAST would only catch after, runtime detection catches drift from approved configuration, and policy-as-code engines prevent the entire class from reaching production at all. Getting that one category right is often the difference between a DevSecOps program that's just running and one that's actually moving the needle. Misconfiguration also produces the cleanest signal — a Checkov finding on a Terraform plan is reproducible, actionable, and rarely a false positive — making it the best starting point for a program that wants to demonstrate value quickly.
Pipelines Surface Findings. Developers Close Them.
The most expensive part of running a mature DevSecOps program is not the tooling — it is the volume of findings the pipeline generates faster than developers can fix them, accumulating into security debt that grows quarter over quarter. Closing that gap is a developer-fluency problem, not a tooling problem, and SecureCodingHub solves it at the PR level by building the security intuition that lets engineers read a finding, recognize the class, and ship a durable fix the first time.
Request a demoSecureCodingHub builds the developer fluency that makes the DevSecOps pipeline produce closed findings rather than open tickets. The toolchain decides what gets surfaced; the engineering team decides what gets fixed. A DevSecOps engineer who invests in fluency on the categories the tools surface most often gets a compounding return: the next quarter's finding flow is smaller, mean time to remediate is faster, and the security posture is genuinely better — not just more thoroughly measured.